Key Takeaways
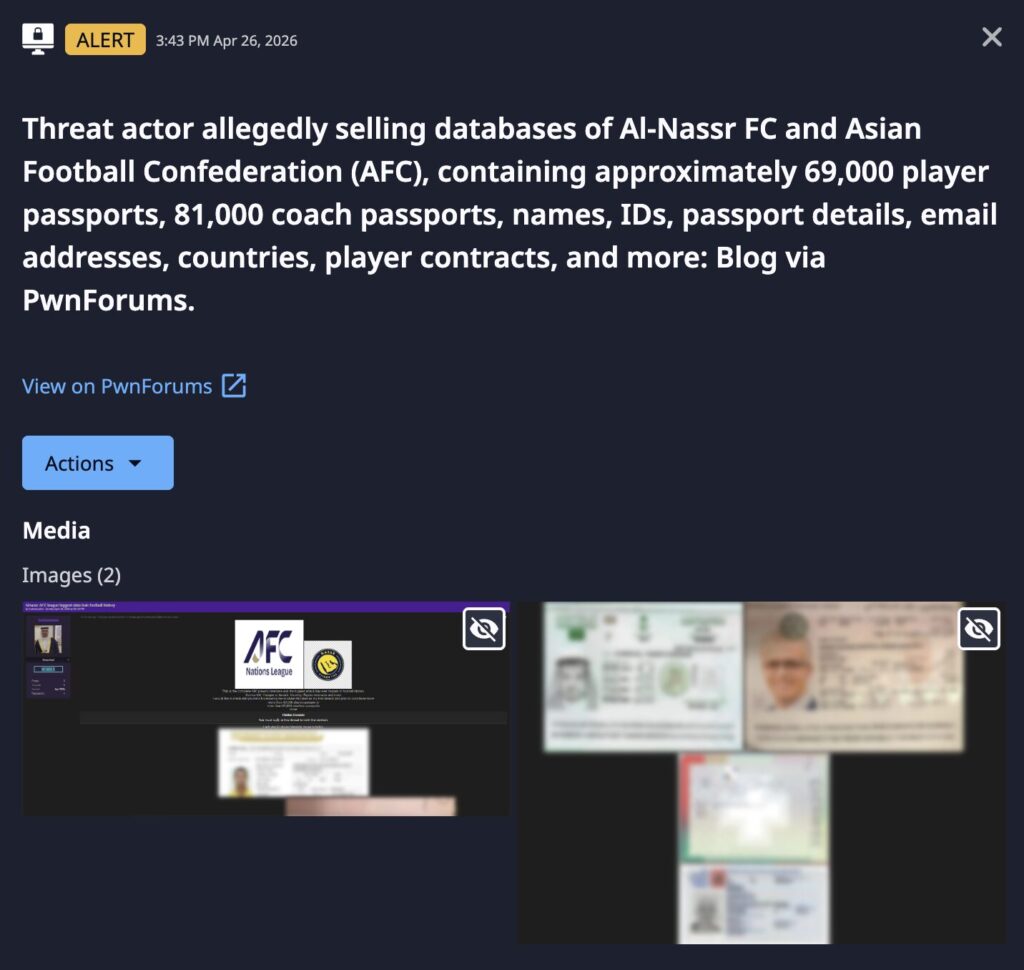
- A threat actor crediting ShinyHunters claims to have leaked the complete AFC player and coach database — allegedly comprising 150,000+ player and coach passports, contracts, emails, and AFC Champions League Elite registration records.
- The combination of passport scans, verified email addresses, and player contract data creates a highly actionable package for financial fraud, contract manipulation, and targeted social engineering against some of the world’s highest-earning athletes.
- The timing is critically significant: the 2026 FIFA World Cup officially kicking off on June 11th, with multiple AFC member nations actively competing — meaning compromised player and official data is live and operationally relevant right now.
- Diplomatic passport scans among the leaked materials elevate this beyond a standard sports breach, with potential national security implications across multiple AFC member nations and FIFA’s broader tournament infrastructure.
Incident Overview
On April 27, 2026, a threat actor published an alleged data leak on a prominent cybercrime forum targeting the entire Asian Football Confederation (AFC) and Al Nassr FC, one of the top clubs in both the men’s and women’s Saudi Premier Leagues. The actor is crediting ShinyHunters with facilitating the share and characterizes it as the largest breach in football history. A personal jab referencing rival football fan communities suggests the actor is embedded in football fan culture and may be baiting public controversy for amplification.
The timing carries compounded significance. The 2026 FIFA World Cup is starting on June 11th, with AFC member nations including Japan, South Korea, Australia, Iran, and Saudi Arabia among the competing sides. Outside of AFC member nations, there are four players on Al Nassr FC who play for European countries in the World Cup – Cristiano Rinaldo (Portugal), Sadio Mané (Senegal), Marcelo Brozović (Croatia), and Aymeric Laporte (Spain).
Player registration data, passport documentation, and contact details held by the AFC directly overlap with the personal and travel infrastructure underpinning World Cup participation. FIFA’s own player eligibility and registration systems maintain data-sharing relationships with confederations including the AFC, meaning the blast radius of this breach may extend into FIFA’s tournament operations and the integrity of competition documentation at the highest level of the sport.
Separately, the AFC was under active institutional scrutiny following its March 2026 ruling against the Football Association of Malaysia for fielding ineligible players using manipulated passport and nationality documentation — placing the AFC’s document verification systems directly in the public spotlight prior to this incident. Al Nassr FC’s inclusion is similarly contextual, given the club’s central role in high-profile Saudi Pro League governance disputes throughout early 2026.
In a separate incident, AFC Ajax disclosed in March 2026 that an attacker accessed its systems via exposed APIs and shared access keys. Football organizations are structurally vulnerable due to the volume of third-party integrations involved in registration, transfer, and player management platforms — consistent with ShinyHunters’ known initial access methods.
Breach Details
The breach allegedly includes 150,000+ player and coach passports IDs, verified email addresses, contracts, and competition registration forms. Included in this count is a number of diplomatic passports, which greatly expands the risk surface beyond the sports sector. Additional data includes:
- Full legal name
- Passport number and scans
- Date of birth
- Nationality
- Playing position
- Jersey name and number
- AFC ID
- Club name and country
- Competition
- Group
- Venue
- Match date details
For the FIFA World Cup, AFC member nation squads will submit player registration and passport data through confederation channels. The overlap between leaked AFC registration data and active FIFA tournament rosters, once they’re submitted, means compromised records are not historical — they are current, verified, and tied to individuals whose movements, accommodations, and schedules are publicly known for the duration of the tournament. This creates a narrow but serious physical security consideration alongside the cyber and financial risks.
The combination of verified email addresses and player contract data creates a particularly high risk of financial fraud. Contract details expose salary figures, agent relationships, renewal clauses, and transfer fee structures. Paired with verified contact information, this enables highly convincing business email compromise (BEC) attacks impersonating agents, club executives, or legal representatives — targeting wire transfers, signing bonuses, image rights payments, or endorsement fee transactions. Players and coaches in the dataset should be considered at elevated risk for fraudulent transfer requests and contract renegotiation scams. The post-World Cup transfer window represents a particularly high-risk period for this type of fraud.
In addition to fraud risk, there is also significant identity fraud risk. Full passport scans combined with dates of birth, nationality data, and AFC IDs provide sufficient detail to open fraudulent financial accounts, apply for credit, or construct synthetic identities — particularly concerning for high-net-worth professional athletes.
Threat Actor and Motivation
The threat actor is assessed as a forum-level operator leveraging the credibility of ShinyHunters, a financially motivated group affiliated with the Scattered LAPSUS$ Hunters (SLH) alliance with a well-documented history of large-scale exfiltration and extortion. Motivation is assessed as primarily financial, with a secondary hacktivism or reputational disruption component given the theatrical framing and football fan culture references in the post.
Target selection reflects a convergence of factors that made the AFC and Al Nassr simultaneously high-profile, symbolically valuable, and operationally vulnerable: the passport forgery scandal, VAR and governance controversies at the AFC Champions League Elite level, PIF favoritism allegations surrounding Al Nassr, geopolitical disruption across the Gulf region, a contracting Saudi sports investment environment that likely stretched cybersecurity operational focus, and the global visibility of the 2026 FIFA World Cup providing maximum reputational impact for any actor seeking to embarrass football’s governing infrastructure.
Immediate Actions & Recommendations
Organizations across the sports industry — including clubs, leagues, federations, and their commercial and legal partners — should treat this incident as a sector-wide warning. ShinyHunters and affiliated actors do not limit their targeting to a single organization, and the TTPs on display here are directly transferable to any institution managing athlete data, contracts, or identity documentation.
- Audit How You Store Athlete and Personnel Data: Any organization holding passport scans, contract details, or verified contact information for athletes, coaches, or officials should immediately review where that data lives, who has access to it, and whether it is adequately protected. Unencrypted document stores and over-privileged access accounts are primary targets.
- Harden Third-Party Integrations: Sports organizations routinely share data across registration platforms, transfer management systems, and competition administration tools. Each integration is a potential entry point. Audit all third-party vendor access, enforce least-privilege principles, and rotate API keys and shared credentials as a precautionary measure.
- Protect Financial Workflows Against BEC: Agents, club finance teams, and legal representatives should implement mandatory out-of-band verification for any financial instruction received by email — particularly those involving transfer fees, contract payments, signing bonuses, or image rights transactions. With contract data now potentially in circulation, convincing impersonation attempts should be anticipated.
- Treat the Post-World Cup Transfer Window as a High-Risk Period: The summer transfer window that follows the tournament is one of the highest-value periods in world football for financial transactions. Organizations involved in transfers should apply heightened scrutiny to all communications and payment requests during this window.
- Raise Awareness Among High-Profile Personnel: Players, coaches, and officials should be briefed on the elevated risk of targeted phishing, identity fraud, and social engineering. Individuals whose passport data may be compromised should monitor financial accounts and consider fraud alerts with relevant institutions.
- Review Document Handling Practices: Organizations that routinely collect and store passport scans and identity documents as part of registration or eligibility processes should evaluate whether current retention policies, access controls, and encryption standards are adequate — and whether all stored documents are genuinely necessary to retain.
- Monitor for Opportunistic Follow-On Attacks: Breaches of this scale and profile typically generate secondary activity — including phishing campaigns targeting affiliated organizations, fraudulent contact attempts impersonating the AFC or member federations, and further data sales. Security teams should increase monitoring accordingly.

2026 World Cup Security Checklist
The 2026 World Cup demands intensive, cross-agency security planning. This checklist offers a strategic framework for security leaders, stadium operators, and public safety agencies to build and validate a comprehensive security plan—from risk assessment and tech integration to crowd control and emergency response.
Learn more