From Real-time Signal to Sightline
Legacy threat intel is noisy, generic, and late. Manual investigations saddle your team—wasting hours, per alert. Dataminr CTTI leverages proprietary Agentic and Multi-Modal Fusion AI to deliver the earliest threat signals – tailored to your environment – cutting investigations from hours to seconds.
Core Platform Capabilities
Dataminr CTTI combines two core capabilities that replace manual work traditionally spread across feeds, portals, and analyst research—closing a gap no security program can afford to leave open: “Does this matter to us?”
Turn Security Into Strategy Today

Core Features
Over 100 specialized AI models work in parallel—not through a single LLM. Multi-Modal Fusion AI processes text, images, video, and audio across 43+ TB of daily data from 1M+ public sources.
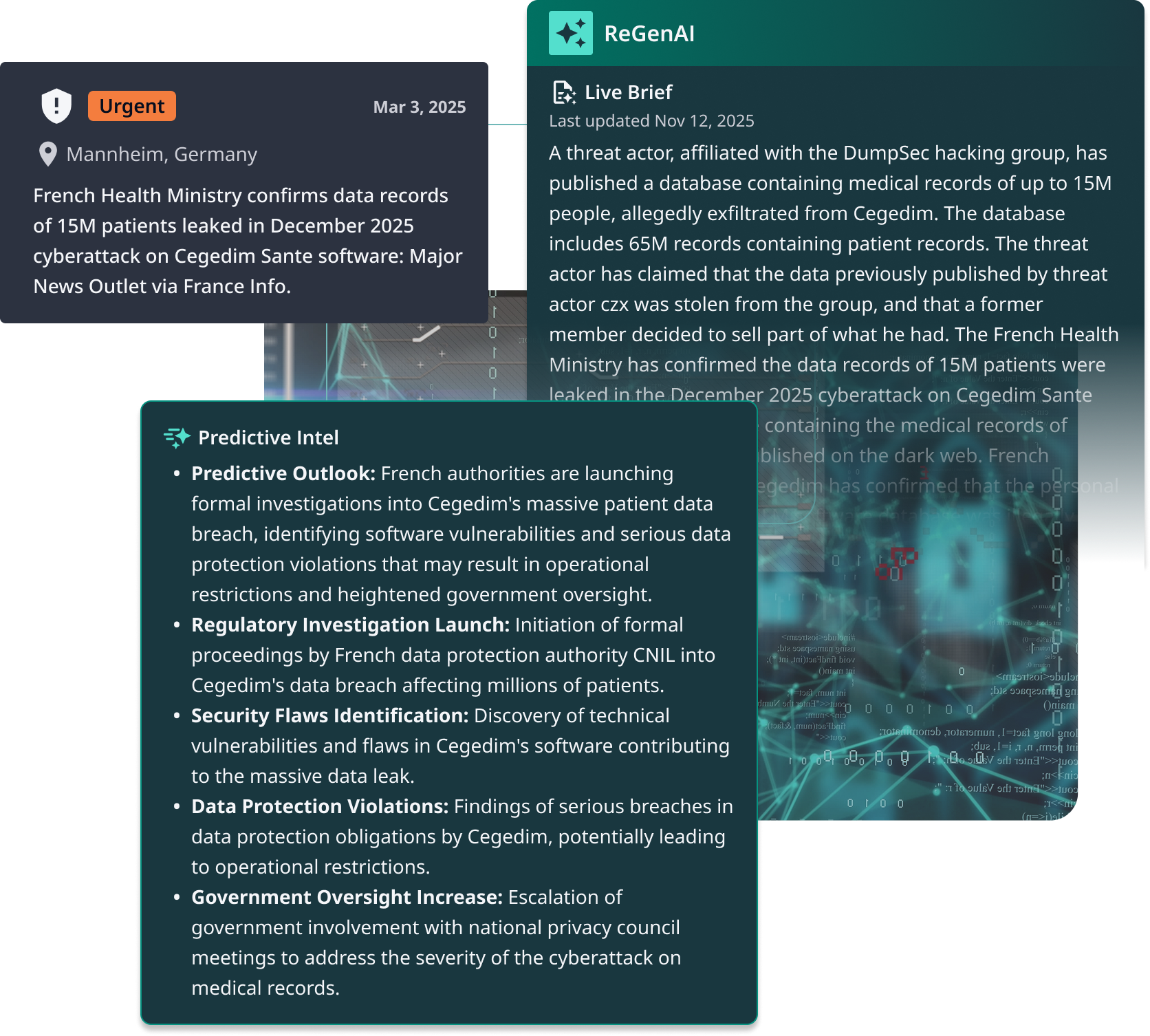
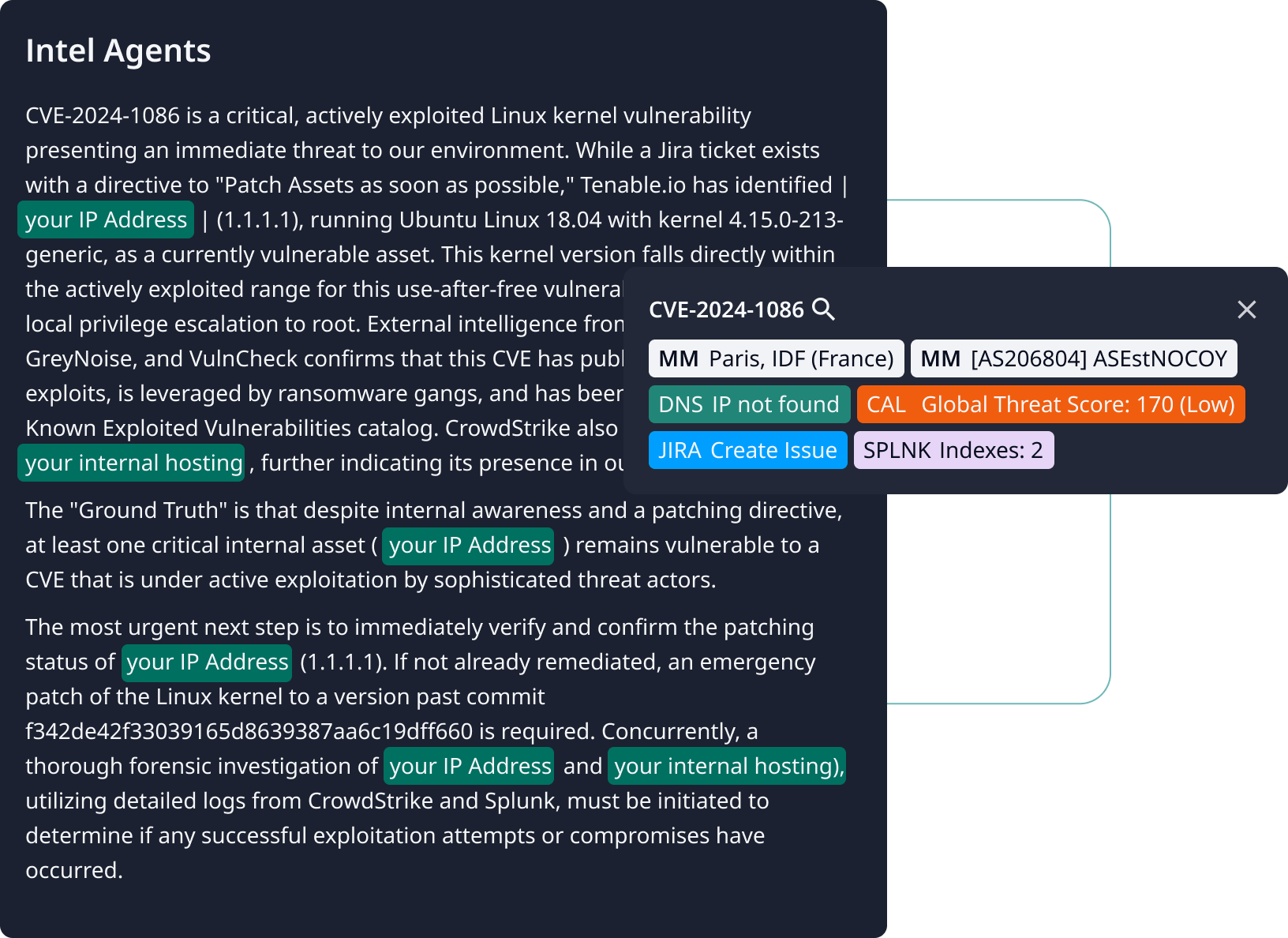
Dataminr Intel Agents autonomously assemble evolving intelligence—correlating actors, TTPs, infrastructure, and vulnerabilities as new signals emerge—without waiting for alerts or manual triage.
Signals contextualized against observed assets, alert activity, and internal environment. Predictive indicators—exploit sophistication, actor coordination—autonomously elevate urgency.
It’s like CTRL+F for your entire security stack. Investigation Insights’ dynamic search spans every connected security tool to confirm exposure, find prior sightings, and correlate activity—all without learning dozens of query languages.
We identify indicators, vulnerabilities, and entities in the analyst’s workflow to retrieve relevant context instantly. Intelligence adapts to the analyst’s workflow, on demand.
Get Started
Deploy in hours, not months. Client-Tailored Threat Intelligence delivers value from day one.
Connect your environment and start receiving client-tailored intelligence immediately. No rip-and-replace. No threat intelligence platform or SOAR, required. No new portals. Intelligence overlays what your team already uses.
Grow With Us
As your environment expands, Client-Tailored Threat Intelligence scales without re-architecting.
A Force Multiplier for Your Existing Security Stack
We don’t replace your tools—we connect them—closing the gaps between detection, prioritization, and response that manual workflows can no longer bridge.
- Push pre-disclosure IOCs and adversary TTPs directly into correlation and detection rules — before threats reach commercial feeds.
- Enrich SIEM alerts in real time with threat context and financial risk scoring.
- Reduce false positives by filtering signals through client-tailored relevance, not just pattern matching.

- Trigger response playbooks directly from intelligence signals — no manual handoff between detection and action
- Feed financial risk scores into incident workflows so responders prioritize by business impact, not alert volume
- Capture analyst decisions to continuously improve automation logic


- Correlate endpoint detections with active adversary TTPs from real-time intelligence
- Prioritize endpoint alerts based on probable financial impact, not severity score alone
- Block threats with higher confidence using intelligence that’s already been tailored to your environment


- Tie vulnerabilities to active adversary campaigns so remediation follows real threat activity, not CVSS rankings
- Surface the exposures with the highest probable financial loss — the ones that actually warrant emergency action
- Map controls and assets for enterprise-wide visibility into what’s protected, what’s drifted, and what’s exposed




- Associate users, devices, and assets to uncover risky access paths that threat actors are actively exploiting
- Quantify identity-driven exposure in dollars and prioritize remediation by business impact


- Ingest firewall, NDR, and data lake telemetry to model real-time exposure across on-prem and cloud
- Correlate network traffic patterns with adversary techniques tracked in our intelligence
- Extend Foresight, Focus, and Action across hybrid environments and multi-cloud workloads


- Monitors 300+ global third-party vendors in real-time
- 5+ hours of understanding First to alert on a vendor’s ransomware breach
- Insights routinely surface hours ahead of legacy intel
- Integrates internal telemetry via Splunk
FAQS
Dataminr’s advanced AI reduces noise through precision tuning, ensuring your team receives highly relevant alerts. You can select alerting based on your role, geographies of interest, topics, event types, and priorities, giving you granular control over the information you receive. Additionally, our ReGenAI Live Briefs distill a rapidly-unfolding event into concise, decision-ready information.
Dataminr uses a multi-layered approach to detect and validate breaking events, drawing on a vast array of public data sources and over 15 years of historical event data. When our platform discovers an initial signal, it automatically identifies corroborating patterns or clusters across additional sources and modalities such as text, images, video, and sensors. This AI-powered cross-source verification ensures the alerts we deliver are timely, relevant, and accurate.
Legacy systems are slow, subjective, and don’t scale, leading to delays and missed alerts. These providers can only cover large-scale incidents, missing the smaller, localized risks on the ground that often matter most. In contrast, Dataminr’s AI-powered platform scales globally while maintaining the granularity to pinpoint events at the facility or localized level. This provides early, actionable visibility into hyperlocal disruptions that other platforms miss.
Dataminr has created a revolutionary real-time AI platform for discovering events, threats, and risks in public data. Dataminr is known for pioneering Multi-Modal Fusion AI, which synthesizes text in 150+ languages, images, video, sound and machine-generated sensor data. The company’s world-leading AI platform—powered by more than 50 proprietary LLMs and multi-modal foundation models and trained on Dataminr’s 12+ year proprietary event archive—performs trillions of computations across billions of public data inputs from over 1M unique public data sources on a daily basis.