Risk You Can Measure. Decisions You Can Defend.
Security leaders know they have risk but can’t prove how much — or which actions reduce it. CCM w/ RQ replaces assumptions with live telemetry, translates control gaps into probable financial loss, and shows where remediation matters most.
Turn Security Into Strategy Today

What Makes Us Different
Continuous validation that controls perform at the level required. Drift, failures, and misconfigs surfaced live.
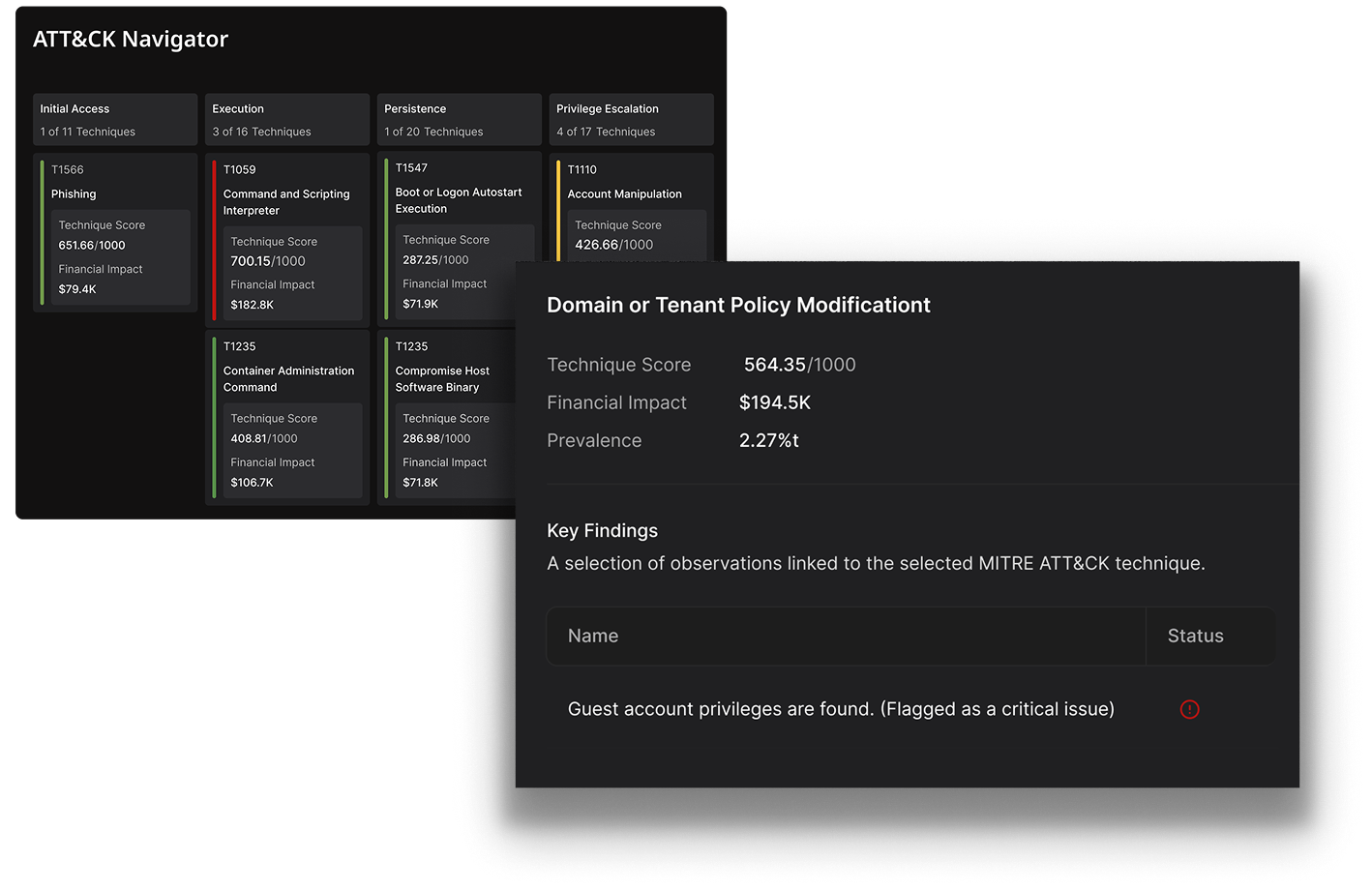
Risk is scored per attacker technique and mapped to financial impact — prioritizing based on real adversary behavior.
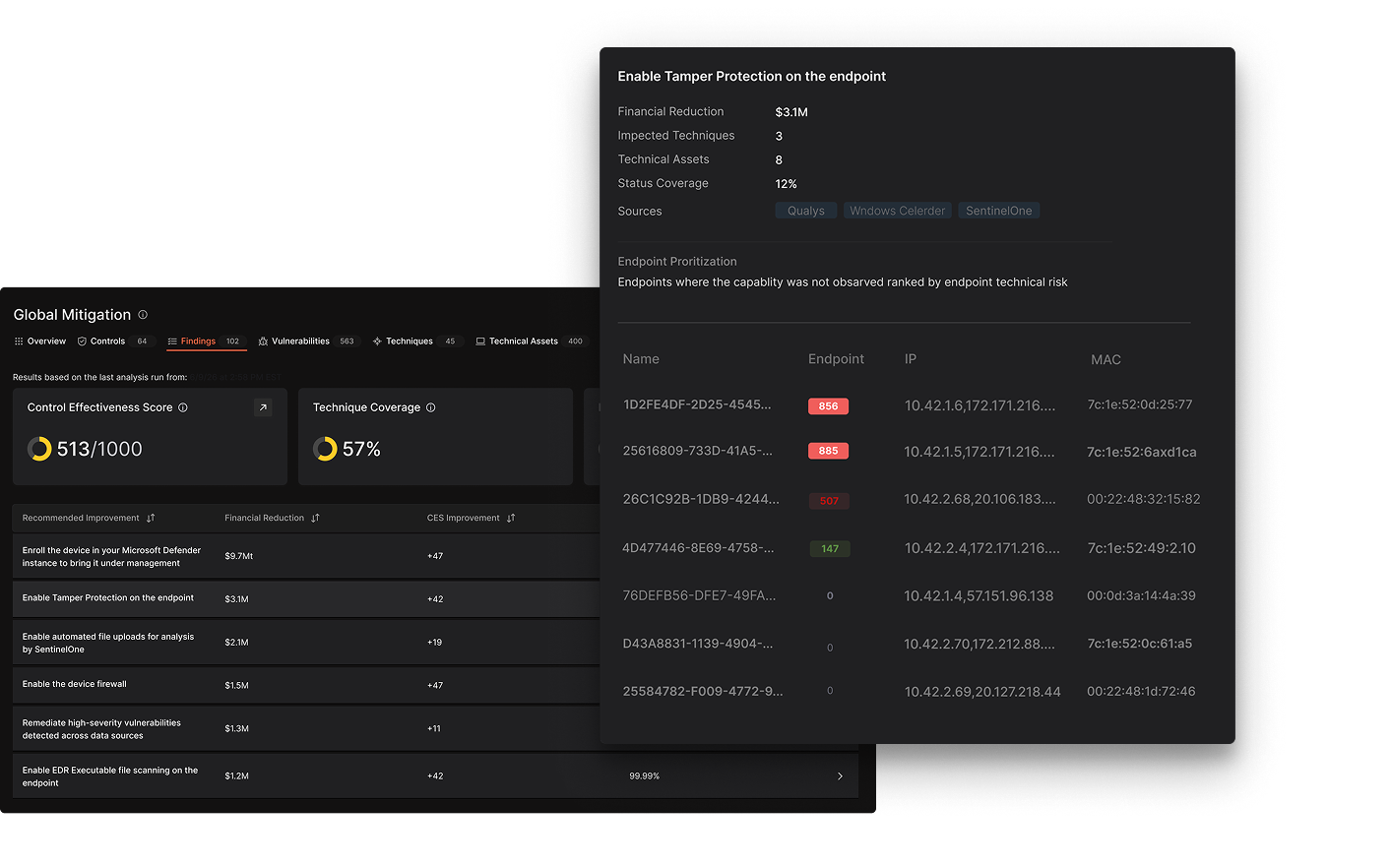
CVEs ranked by dollars at risk — factoring in exploitability and compensating controls, not just CVSS severity.
Real-time risk views designed for CISOs, CFOs, and board reporting — translating technical exposure into financial language.
Every Observation includes ranked remediation options with projected risk reduction — teams know where to start.
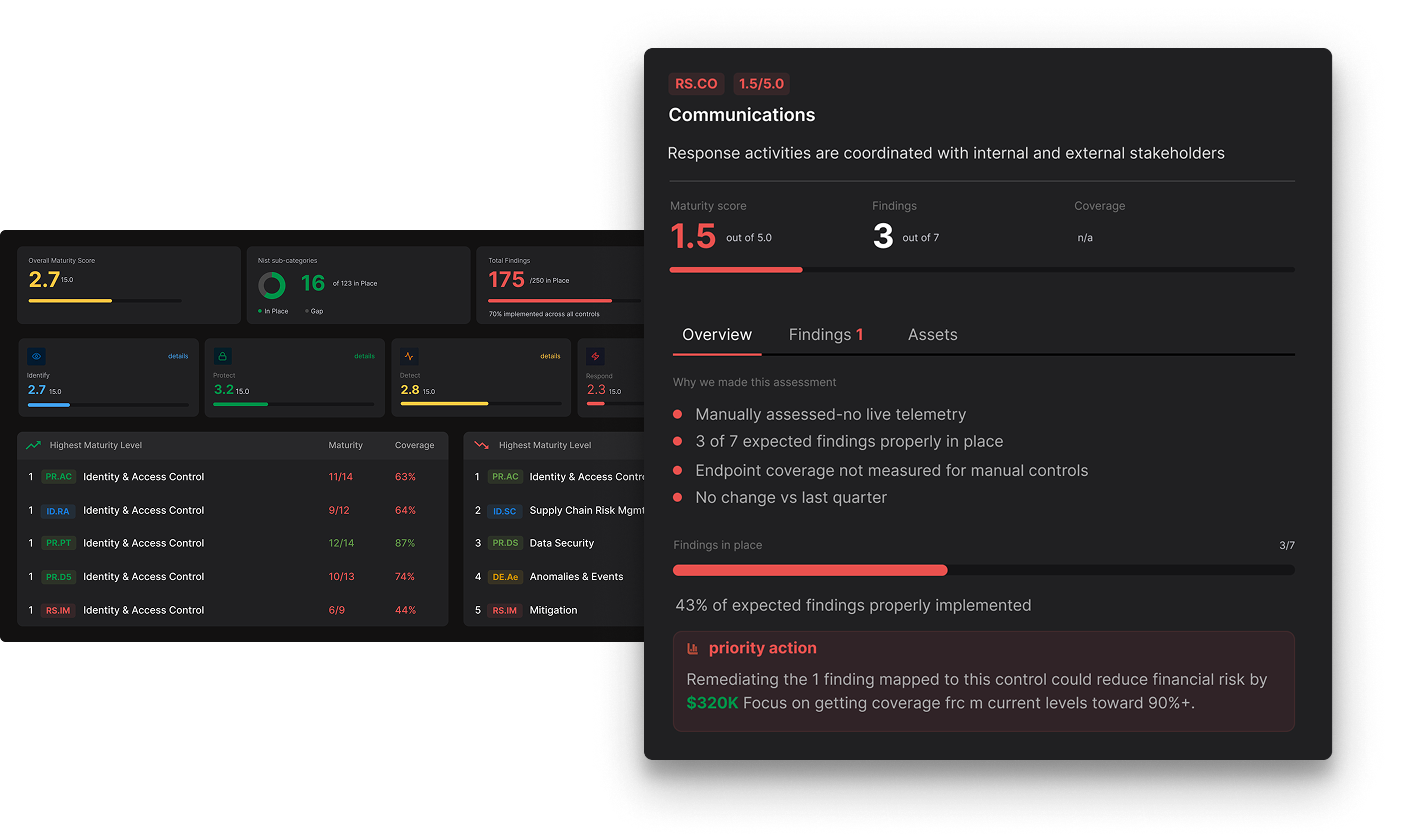
Telemetry-driven maturity scoring that measures how well controls actually perform — linking control effectiveness to measurable risk reduction.
Key Integrations & Ecosystem
More than 100 integrations across your entire security stack. RQ integrates with the tools you already use to assess control effectiveness, identify coverage gaps, and quantify risk based on real adversary behavior-mapped to MITRE ATT&CK. RQ supports a broad ecosystem across the following key categories.
- Pull identity data from platforms like Okta and Entra to associate users, devices, and assets.
- Uncover access-related risk paths and quantify user-centric threats.


- Connect to EDR and vulnerability tools like CrowdStrike, SentinelOne, and Qualys.
- Surface asset health, known exploits, and control gaps in one view.




- Ingest firewall and NDR data from Palo Alto, AWS, GCP, and others.
- Model exposure based on known traffic patterns and threat behavior.

- Pull from tools like ServiceNow CMDB/IRM and SureCloud.
- Assess how controls apply across services, apps, and operational workflows.


- Power CRQ with telemetry from across your stack.
- Ingest from ThreatConnect TIP, Zscaler, Snowflake, and other data lakes.
- Feed modeling logic with enriched intel, telemetry, and asset metadata.


Extend Your Cyber Defense with Dataminr
CCM w/ RQ connects threat intelligence to business impact — the financial decision engine every CTEM program requires at its center.


FAQS
GRC platforms track compliance and policy adherence. CCM w/ RQ validates real-world control performance using live telemetry — proving whether controls are actually enforced, not just documented. Compliance artifacts don’t equal protection. This does.
No. CCM w/ RQ ingests data from your existing vulnerability scanners, endpoint tools, and cloud platforms. It adds a financial risk layer on top — re-ranking what you’ve already found by probable business impact instead of CVSS alone.
AI-driven loss models trained on 20+ years of cyber loss data estimate probable financial impact using live inputs including control effectiveness telemetry, asset criticality, attacker behavior mapped to MITRE ATT&CK TTPs, and exploitability data. Risk is expressed in dollars at the asset, business unit, and portfolio level.
Yes. The real-time risk ticker provides a continuously updated, audit-ready view of enterprise cyber risk — expressed in financial terms that executives and boards can act on. No translation layer needed between SecOps and the boardroom.
Control effectiveness is measured from live telemetry — not periodic scans or annual questionnaires. When a control drifts, fails, or isn’t enforced, risk is recalculated automatically. You see the impact in near real time, not next quarter.
Empirical Control Maturity Scoring complements NIST assessments by continuously measuring control performance using live security telemetry. Instead of relying solely on periodic questionnaires or manual reviews, maturity is derived from observed evidence of how controls actually operate, providing a real-time validation of your NIST control posture.
Yes. It delivers independent value for control validation and financial risk quantification. It becomes dramatically more powerful when paired with Dataminr Threat Intelligence — feeding real attacker behavior into risk models so exposure reflects what adversaries are actually doing, not theoretical scenarios.


