Key Takeaways
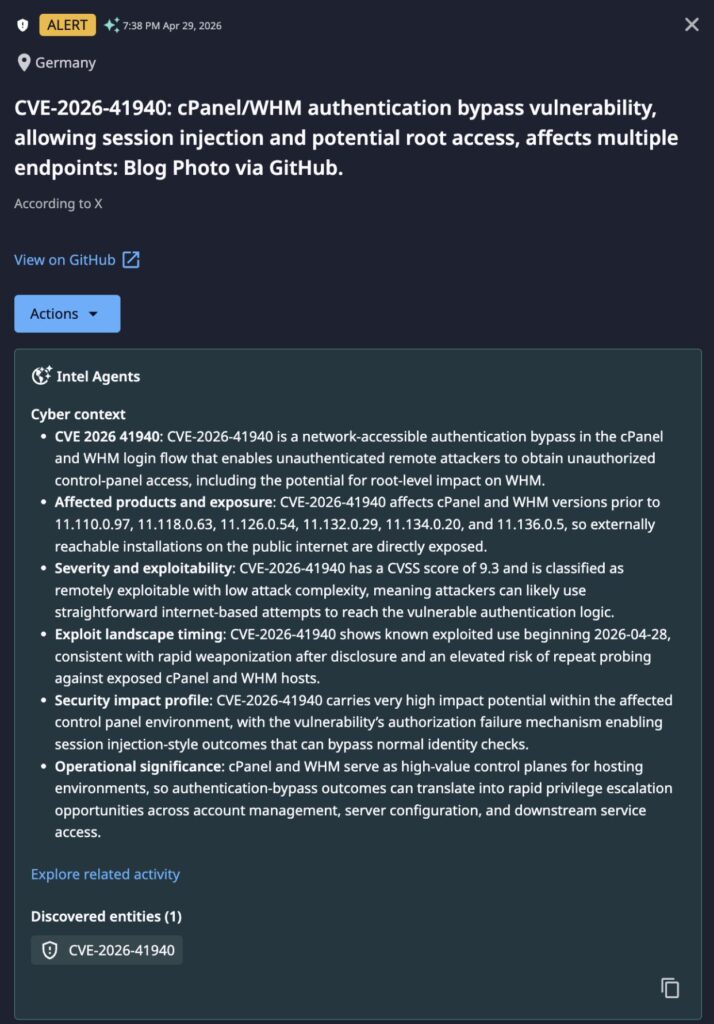
- CVE-2026-41940 is a critical (CVSS 9.8) authentication bypass zero-day in cPanel/WHM, actively exploited in the wild since at least February 23, 2026 — two months before a patch was available.
- WebPros International released a patch on April 28, 2026; watchTowr published a working PoC just one day later on April 29, 2026, creating an extremely narrow remediation window for unpatched organizations.
- Dataminr detected and alerted on the PoC the same day it was published, providing customers with immediate warning ahead of anticipated mass exploitation campaigns.
- CISA has added CVE-2026-41940 to its Known Exploited Vulnerabilities (KEV) catalog, mandating federal remediation by May 3, 2026.
Incident Overview
On April 28, 2026, WebPros International published a security advisory and released patches for CVE-2026-41940, a missing authentication vulnerability in cPanel and WHM. Evidence indicates the vulnerability was actively exploited in the wild as early as February 23, 2026, representing a window of over two months during which attackers operated without a vendor patch. Only one day after the patch release, watchTowr published a full technical write-up and working PoC on April 29, 2026.
Dataminr detected and alerted customers to the PoC the same day it was released, enabling security teams to immediately reassess exposure and accelerate remediation before mass scanning campaigns could fully operationalize the exploit. With approximately 1.5 million cPanel instances internet-exposed, the combination of a public PoC, prior active exploitation, and a one-day patch-to-exploit turnaround makes this a critical priority for any organization running cPanel or WHM infrastructure.
Dataminr Detection
Technical Details
The vulnerability is rooted in a CRLF (Carriage Return Line Feed) injection flaw within cPanel/WHM’s login and session-loading process. By sending a specially crafted unauthenticated request, an attacker can bypass the authentication mechanism entirely and gain unauthorized administrative access to the host system.
- Affected Versions: All cPanel/WHM versions after v11.40; WP Squared v136.1.7
- Attack Vector: Remote, unauthenticated, network-based
- Impact: Full system compromise — including hosted websites, databases, configurations, and email accounts
- Patch Released: April 28, 2026 (WebPros International)
- PoC Released: April 29, 2026 (watchTowr) — one day post-patch; Dataminr alert delivered same day
Immediate Actions & Remediations
- Patch Immediately: Apply the security update released by WebPros International on April 28, 2026. All cPanel/WHM versions after v11.40 and WP Squared v136.1.7 are affected. The one-day patch-to-PoC timeline makes this an emergency remediation priority.
- Audit for Compromise: Given exploitation dates back to at least February 23, assume any unpatched internet-facing cPanel instance may already be compromised. Conduct forensic review of authentication logs, new account creation, scheduled tasks (cron jobs), and file integrity.
- Restrict External Access: If immediate patching is not feasible, restrict access to the cPanel/WHM administrative interface (typically ports 2082, 2083, 2086, 2087) to trusted IP ranges only via firewall rules.
- Review Hosted Environments: Assess all websites, databases, and email accounts hosted on affected cPanel instances for signs of unauthorized modification, webshell deployment, or data exfiltration.
- Monitor for Mass Scanning: Block known scanning infrastructure and monitor for unusual inbound traffic to cPanel management ports consistent with automated exploit attempts following the public PoC release.

2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report