Always-On Vigilance. Zero Noise.
Attacks happen in minutes; manual intel takes hours. Dataminr Threat Intelligence delivers high-efficacy, real-time visibility across the global attack surface—empowering security teams to detect, defend, and disrupt fast-breaking cyberthreats and learn about zero-day attacks before ‘Day Zero.’

Turn Security Into Strategy Today

Core Features
Dataminr AI analyzes 43+ TB of daily public text, image, video, code, and sensor data to identify the earliest threat signals and expose patterns that single-source techniques miss.
Dataminr ingests and analyzes signals from 1M+ public, deep, and dark web sources—including hacker forums, code repositories, paste sites, social media, technical research, breach reports, and more.
With 12+ years of historic alert data, Dataminr’s Knowledge Graph enables complex, real-time correlation of adversary activity, infrastructure, CVEs, TTPs, and exploit signals.
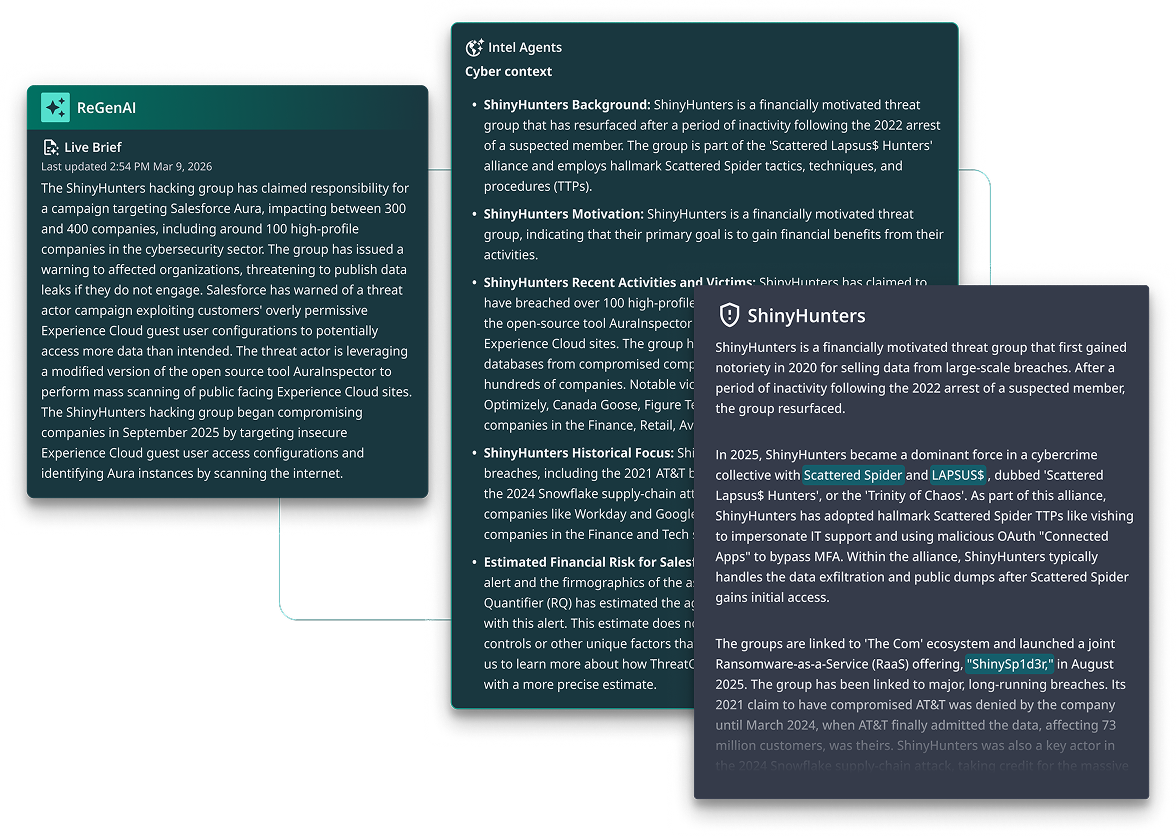
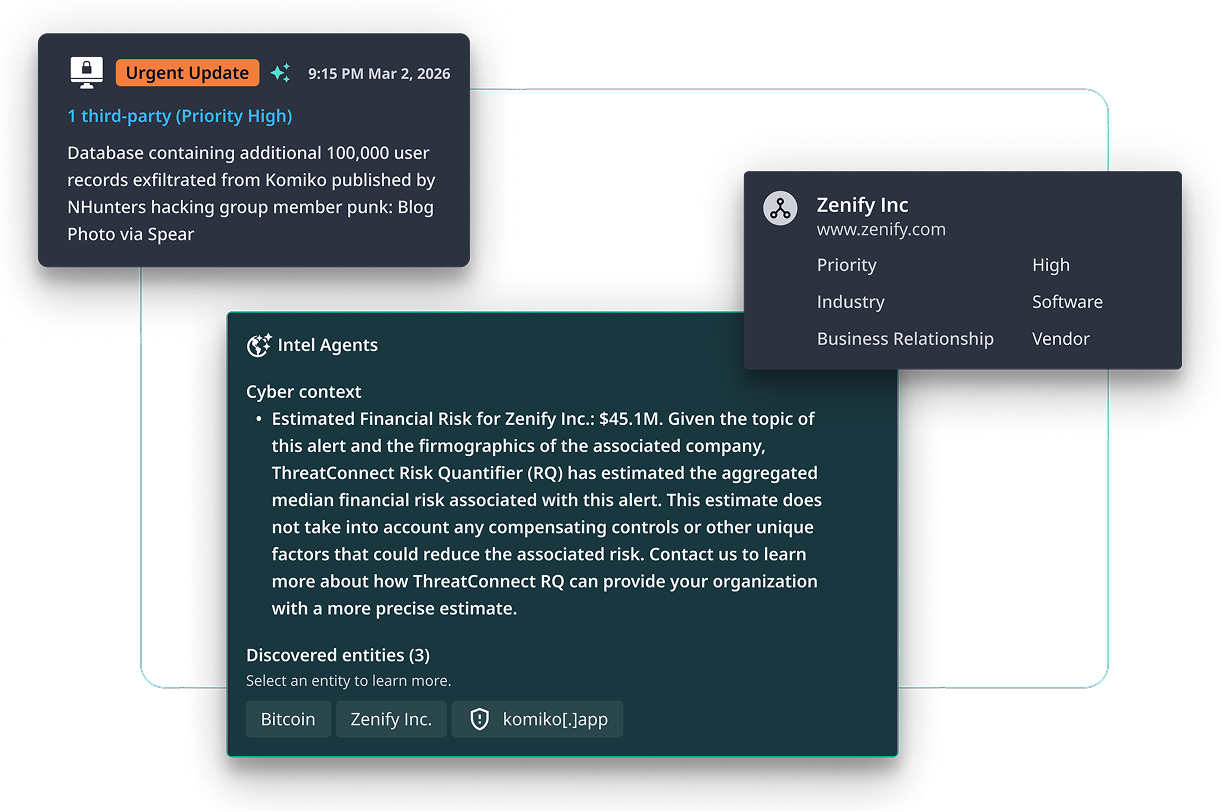
Dataminr Intel Agents augment and tailor inbound insights to your unique organization and attack surface, mapping threats to your assets, technologies, and vendors—so you see what matters most, first.
Based on vast datasets of historical cyber events, adversary TTPs, and attack trends, Dataminr anticipates adversaries’ likely next actions—helping teams prepare and preempt threats before impact.
Dataminr’s proprietary GenAI produces instant summaries of critical cyber events, collating all related alerts into one streamlined, always-current brief that updates in real-time as the event evolves.
Key Integrations & Ecosystem
We don’t ask you to change how you work. Native connectors for SIEM, SOAR, and TIP providers ensure Dataminr Threat Intelligence flows seamlessly and securely into your dashboards, playbooks, ticketing systems, and orchestration tools.
- Push pre-disclosure IOCs and adversary TTPs directly into correlation and detection rules — before threats reach commercial feeds.
- Enrich SIEM alerts in real time with threat context and financial risk scoring.
- Reduce false positives by filtering signals through client-tailored relevance, not just pattern matching.

- Trigger response playbooks directly from intelligence signals — no manual handoff between detection and action
- Feed financial risk scores into incident workflows so responders prioritize by business impact, not alert volume
- Capture analyst decisions to continuously improve automation logic


- Correlate endpoint detections with active adversary TTPs from real-time intelligence
- Prioritize endpoint alerts based on probable financial impact, not severity score alone
- Block threats with higher confidence using intelligence that’s already been tailored to your environment


Extend Your Cyber Defense with Dataminr
Threat Intelligence is the detection engine behind every Dataminr for Cyber Defense solution. Wherever intelligence starts in our system, it starts here.



FAQS
Legacy threat intel feeds rely on static IOC lists, known malware signatures, and CVEs from stale, curated sources. Updates are slow, reactive, and generic that deliver outdated insights with little context on relevance, timing, or impact.
Dataminr Threat Intelligence leverages multi-modal AI, 55+ proprietary LLMs, and a Knowledge Graph built on 12+ years of cyber alert data to analyze 43+ TB of daily signals across 1M+ sources. Dataminr Intel Agents autonomously assemble and correlate adversary activity, exploits, CVEs, and TTPs—tailoring insights to your assets, vendors, and exposures continuously in real-time.
Dataminr AI is trained on vast datasets of historical cyber events, adversary TTPs, and global attack trends to identify patterns that often precede emerging threats. By continuously analyzing activity across the global digital ecosystem—including hacker forums, code repositories, vulnerability disclosures, and technical research—Dataminr detects weak signals of exploit development, targeting activity, and coordinated attacks at their earliest stages.
Proprietary AI detection models and Intel Agents correlate these early signals with known adversary behaviors to anticipate how threats are likely to evolve. The result is predictive intelligence that helps security teams prioritize defenses, prepare countermeasures, and disrupt attacks before they escalate into incidents.
Security and CTI analysts alike spend significant portions of their daily work hours manually collecting, validating, and correlating threat data from multiple sources.
Dataminr reduces this operational burden with Intel Agents that automatically assemble threat context from disparate signals into structured, contextualized alerts and live intelligence briefs. They correlate IOCs, adversary infrastructure, CVEs, exploit signals, and MITRE ATT&CK techniques in seconds—enabling analysts to immediately understand what is happening, why it matters to their environment, and what action to take next.
The result is dramatically faster investigation cycles, reduced alert fatigue, and improved signal-to-decision speed for both SOC and CTI teams.
Traditional security programs focus on responding to incidents after threats are already active.
Dataminr Threat Intelligence enables a preemptive cyberdefense posture by delivering the earliest possible visibility into adversary behavior across the global digital ecosystem. Security teams gain advance awareness of exploit development, emerging vulnerabilities, ransomware targeting, and third-party risk events before attacks reach their environment.
By combining early external signals with historical adversary patterns and industry attack trends, Dataminr helps organizations anticipate likely attacker actions, prioritize defensive measures, and disrupt threats before they escalate into incidents.
Security leaders can demonstrate the ROI of Dataminr Threat Intelligence by measuring improvements in detection speed, analyst efficiency, and incident response outcomes. By delivering early, decision-ready intelligence, Dataminr helps teams investigate and respond faster—often reducing incident response time by up to 70%.
Analysts spend less time collecting and correlating signals and more time mitigating real threats. The result is measurable business value: fewer incidents, reduced operational disruption, and more efficient use of security resources.