Continuous Threat Exposure Management based on Cyber Risk Quantification
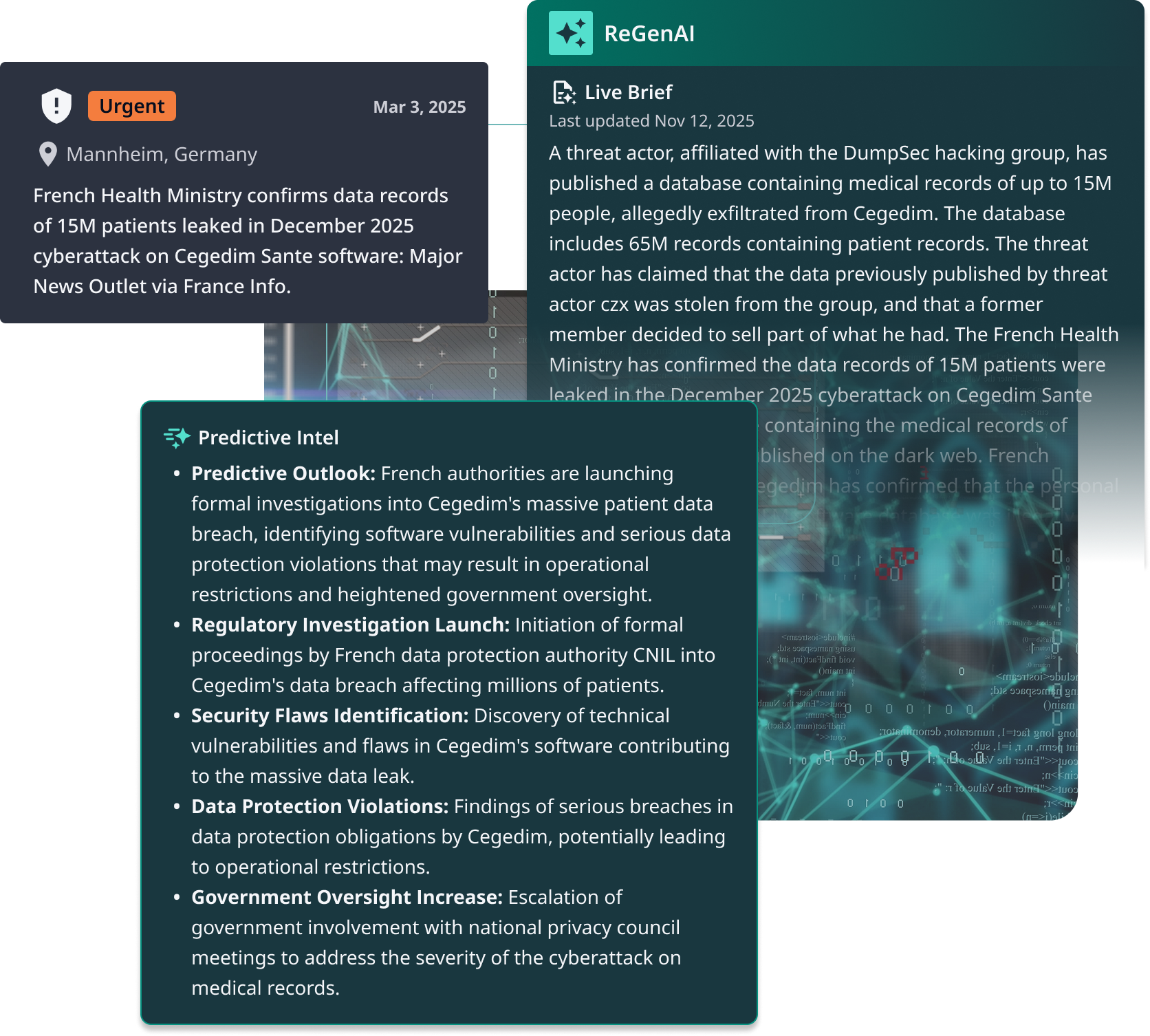
Most exposure tools look backwards—periodic scans, static scores, assumed controls. Dataminr PTEM looks ahead, dynamically identifying exposures by exploitability, validating compensating controls, and quantifying financial risk. Now teams fix what matters first, not patching yesterday’s posture.
Core Platform Capabilities
Two capabilities close the gap between attacker activity, defense performance, and business loss — the gap most security budgets exist to address.
Turn Security Into Strategy Today

Core Features
Measures whether controls are working using live telemetry — no manual inputs. Turns CTEM from a periodic exercise into continuous, evidence-backed infrastructure.
Produces Findings: control gaps tied to specific assets, mapped to attacker behavior, and prioritized by financial impact — with ‘next best fix’ guidance attached.
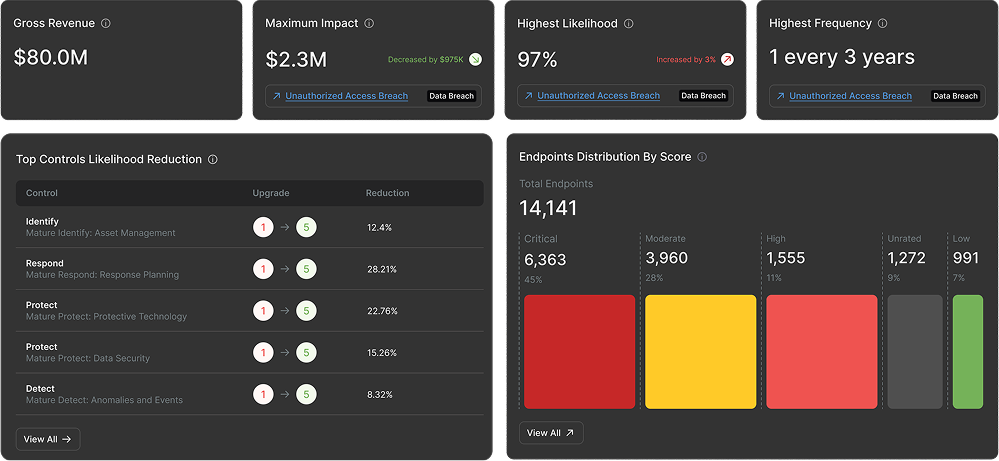
Ground cyber risk decisions in defensible financial data. Models calibrated on 20+ years of historical cyber loss data and validated by some of the world’s largest organizations — accurate, explainable, and audit-ready.
Quantifies risk at the technique level, mapping ATT&CK behaviors to financial value — so teams prioritize based on real-world attacker behavior and business impact.
Links vulnerabilities to affected assets and ranks them by dollars at risk, factoring in exploitability and compensating controls. Not CVSS — actual financial exposure.
Real-time visibility into what’s protected, what’s exposed, and what it costs — giving CI.
Get Started
Activate continuous control monitoring in weeks, not months — PTEM delivers evidence-backed risk visibility and financial clarity from day one.
Grow With Us
As your CTEM program matures, PTEM compounds value — sharper models, deeper alignment.
A Force Multiplier for Your Existing Security Stack
We don’t replace your tools—we connect them—closing the gaps between detection, prioritization, and response that manual workflows can no longer bridge.
- Validate endpoint control enforcement across critical assets
- Surface endpoint protection gaps tied to financial impact


- Monitor network segmentation and access control effectiveness
- Correlate firewall policy drift with real-world exploit activity

- Prioritize CVEs by dollars at risk, not CVSS alone
- Factor in compensating controls and exploitability


- Validate identity control enforcement against credential-based attack patterns
- Surface access policy gaps driving financial exposure



- Route financially prioritized remediation actions into operational workflows
- Trigger “next best fix” guidance from quantified risk assessments


FAQS
Most CTEM tools rely on periodic scans or manual attestations. PTEM continuously measures whether controls are enforced and functioning using live telemetry. When controls drift or fail, the system surfaces impacted assets and prioritizes fixes by financial impact — turning CTEM from a quarterly exercise into a continuous program.
Prediction without quantification creates awareness, not action. PTEM evaluates forecasted threats in financial terms so organizations proactively mitigate the exposures most likely to cause material loss — shifting from reactive defense to economically driven risk prevention. Leaders get evidence to justify budget, not just dashboards to explain posture.
CVSS ranks severity by technical characteristics — ignoring compensating controls, real exposure, and business context. PTEM ranks by dollars at risk, factoring in exploitability, control effectiveness, and asset criticality. In our 2026 report, a CVSS 7.0 CVE ranked “High” while a CVSS 9.0 ranked “Moderate” — financial impact told a different story.
A vulnerability is only an exposure if that CVE exists on your endpoints and isn’t covered by a compensating control. PTEM closes that gap.
Yes. PTEM measures how remediation actions change expected loss over time — not just posture metrics. As controls are strengthened, risk recalculates automatically, showing measurable reduction in expected financial loss. This turns security from activity reporting into outcome accountability, giving leaders defensible evidence to justify priorities and tradeoffs.