From Chaos to Order: Decision-Grade Intelligence
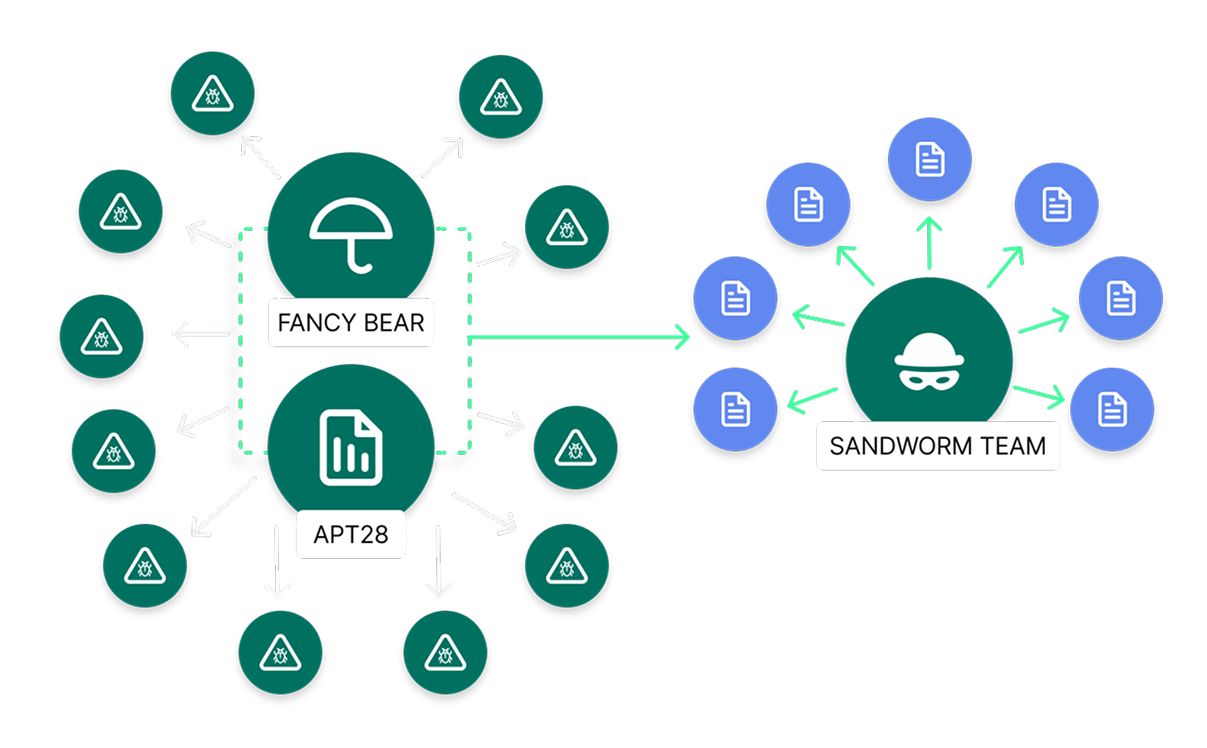
Your analysts produce valuable intelligence every day — then watch it die in a spreadsheet. Dataminr’s Agentic TIP turns every investigation into structured, reusable intelligence that scores, routes, and compounds across detection, response, hunting, and reporting.
Turn Security Into Strategy Today

From Indicators to Decisions: Operationalizing Intelligence
What Makes Us Different
AI-enhanced intelligence requirements ensure a relentless focus on business-relevant threats
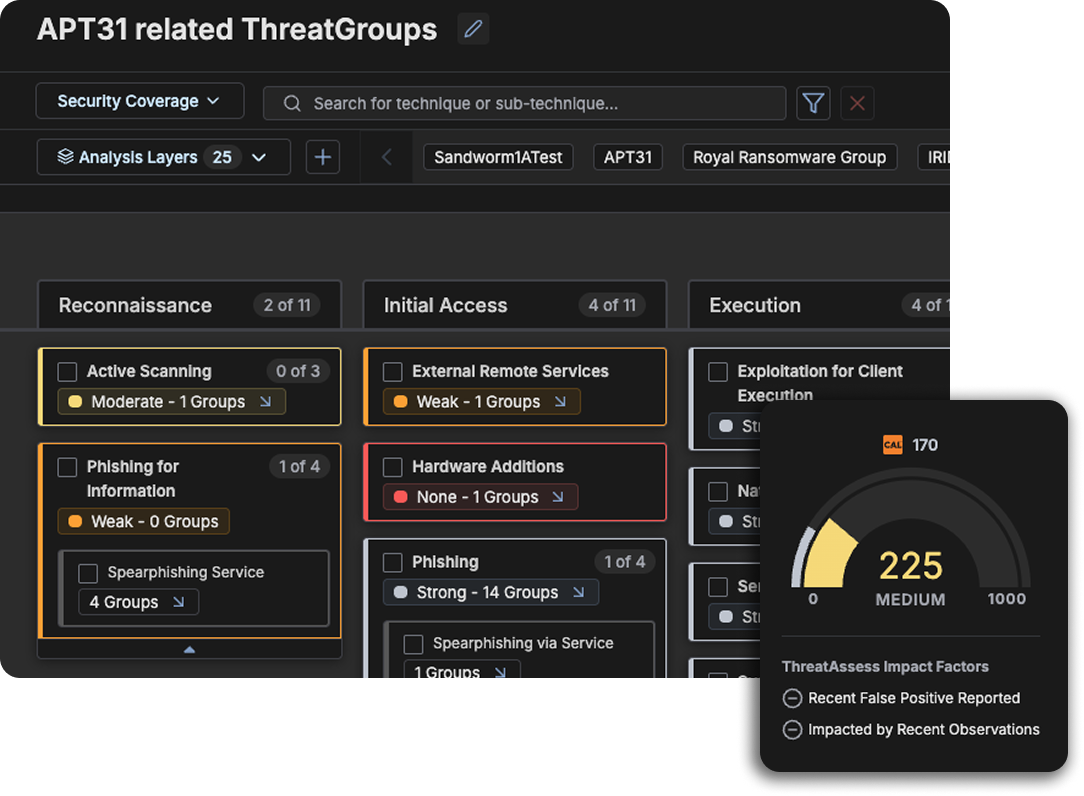
ATT&CK threat modeling tied directly to financial risk and critical business services
CAL delivers real-world enrichment from a global network of real analysts in the field.
Real-time feedback loops tie detection engineering back to intel.
Seamlessly run tens of thousands of automations per day without performance degradation
98% of customers report the Threat Intelligence Platform is critical to their operations

97% report improvements in the effectiveness of operational tools like SIEMs, SOARs, and EDRs

90% report time savings > 50%

67% report > 50% reduction in MTTR

63% say that Dataminr reduced their false positive rates

79% report that Dataminr improves collaboration between teams
Extend Your Cyber Defense with Dataminr
The Agentic TIP is what turns intelligence from something analysts consume into something the organization operates on — the operational core of Agentic TI Ops.

Key Integrations & Ecosystem
More than 100 integrations across your entire security stack. RQ integrates with the tools you already use to assess control effectiveness, identify coverage gaps, and quantify risk based on real adversary behavior-mapped to MITRE ATT&CK. RQ supports a broad ecosystem across the following key categories.
- Push pre-disclosure IOCs and adversary TTPs directly into correlation and detection rules — before threats reach commercial feeds.
- Enrich SIEM alerts in real time with threat context and financial risk scoring.
- Reduce false positives by filtering signals through client-tailored relevance, not just pattern matching.

- Trigger response playbooks directly from intelligence signals — no manual handoff between detection and action
- Feed financial risk scores into incident workflows so responders prioritize by business impact, not alert volume
- Capture analyst decisions to continuously improve automation logic


- Correlate endpoint detections with active adversary TTPs from real-time intelligence
- Prioritize endpoint alerts based on probable financial impact, not severity score alone
- Block threats with higher confidence using intelligence that’s already been tailored to your environment


- Tie vulnerabilities to active adversary campaigns so remediation follows real threat activity, not CVSS rankings
- Surface the exposures with the highest probable financial loss — the ones that actually warrant emergency action
- Map controls and assets for enterprise-wide visibility into what’s protected, what’s drifted, and what’s exposed




- Associate users, devices, and assets to uncover risky access paths that threat actors are actively exploiting
- Quantify identity-driven exposure in dollars and prioritize remediation by business impact


- Ingest firewall, NDR, and data lake telemetry to model real-time exposure across on-prem and cloud
- Correlate network traffic patterns with adversary techniques tracked in our intelligence
- Extend Foresight, Focus, and Action across hybrid environments and multi-cloud workloads


FAQS
Legacy TIPs are systems of record — they manage intelligence after analysts produce it. Dataminr’s Agentic TIP includes full TIP capabilities, but adds autonomous intelligence assembly via Intel Agents, pre-built and custom no-code agentic playbooks, and a unified threat library where intelligence is scored, routed, and applied across the full lifecycle. Intelligence compounds. It doesn’t sit idle.
In October 2025, our AI detected an actively exploited Fortinet zero-day 38 days before CISA added it to the KEV catalog. We monitor 1M+ sources across text, image, video, and audio simultaneously — so we see signals where traditional feeds aren’t looking yet.
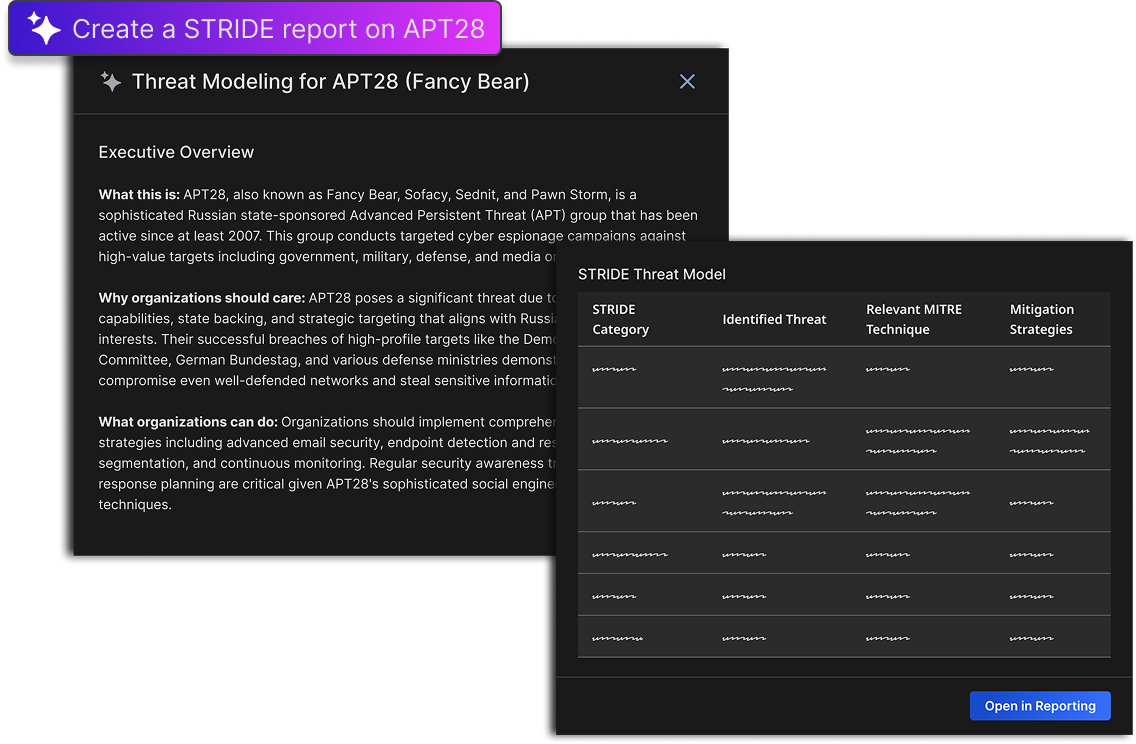
Most cybersecurity AI summarizes what you already have. We built 100+ specialized AI models, each trained for a specific task — detecting exploit chatter, reading malware screenshots, correlating dark web signals with your asset inventory. Our Intel Agents autonomously collect, correlate, map to MITRE ATT&CK, produce finished intelligence, and route it into your tools. Your analysts review the output instead of building it from scratch.
No. Three solutions build on each other — start where your biggest pain is. Close visibility gaps with Client-Tailored TI. Automate manual processes with Agentic TI Ops. Translate risk into financial language with Predictive Threat Exposure Management. Each delivers standalone value. They compound when connected.
- CISO / Security Leadership: Translate technical exposure into financial risk the board can act on. Defend budget with dollars, not heatmaps.
- SOC / Incident Response: Intelligence arrives already assembled, tailored to your assets, and delivered in-workflow — no manual enrichment, no portal pivots. One customer cut total IR time from 7 hours to 37 minutes.
- CTI Teams: Stop spending 80% of your time on collection. Intel Agents handle the lifecycle — you focus on analysis and advising the business.
- Vulnerability Management / GRC: Prioritize by probable financial loss, not CVSS. Continuously validate controls and report risk reduction in leadership’s language.