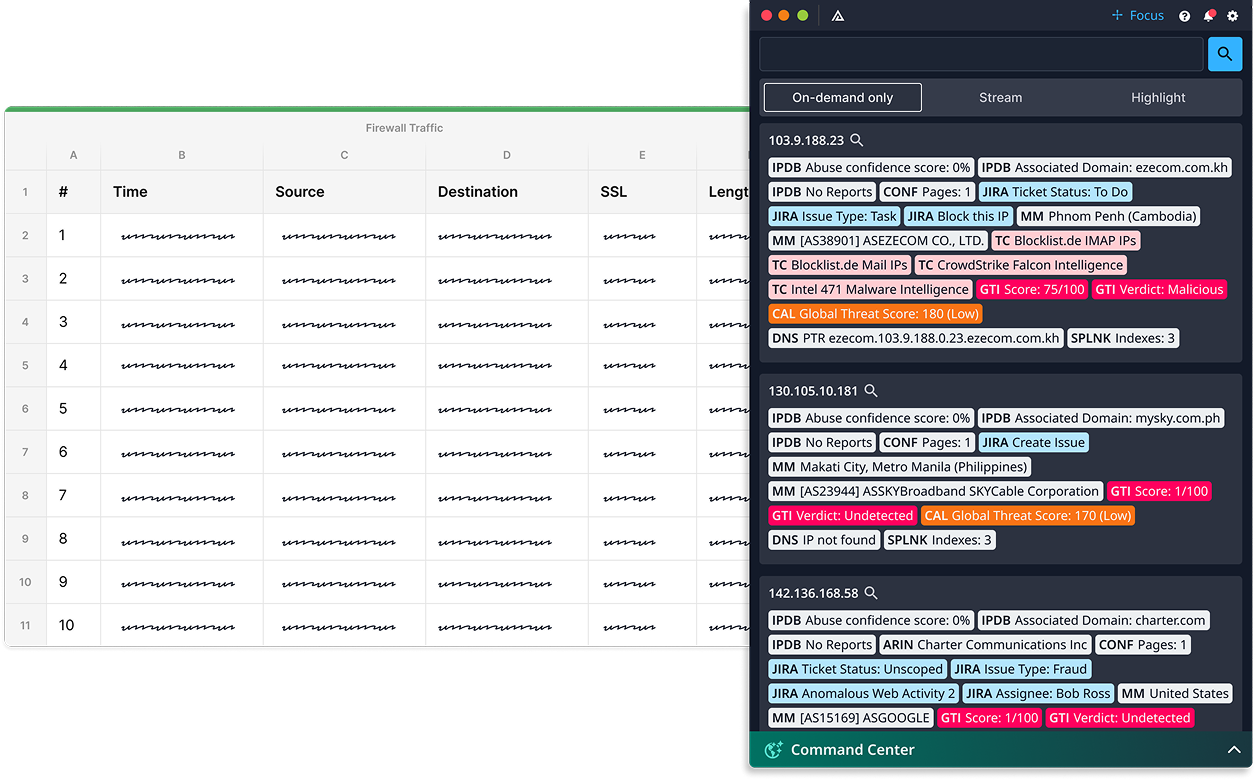
Investigations Measured in Seconds, Not Minutes
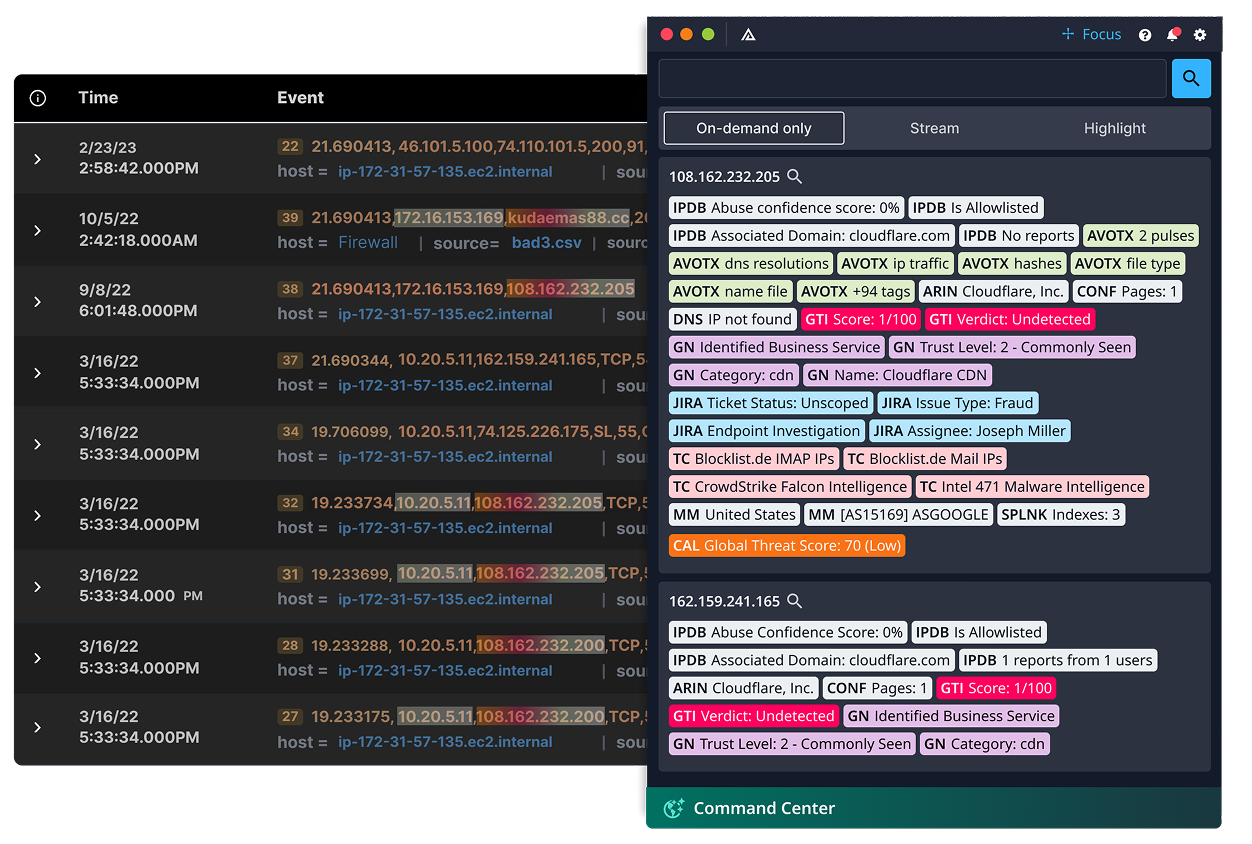
Every alert triggers the same grind: copy, tab, paste, search, repeat across ten tools. It’s the manual tax on every investigation. Investigation Insights assists analysts by quickly searching 200+ connected system connected systems before you finish reaching for the keyboard.
Turn Security Into Strategy Today

Core Features
Key Integrations & Ecosystem
Investigation Insights connects to 200+ tools without writing a single line of code. And it lets you search across them from anywhere.
- Triage alerts faster by instantly surfacing threat context next to matching IOCs
- Correlate logs to known threats using real-time overlays from intelligence sources
- Reduce alert fatigue by filtering low-priority events using enrichment scoring

- Trigger automated playbooks directly from the overlay – no console hopping
- View enrichment and confidence scores on indicators before deciding to escalate
- Capture analyst decisions to improve future automation logic


- Correlate endpoint alerts with threat actor TTPs from TI Ops
- See whether a process, domain, or hash has been previously analyzed or suppressed
- Investigate faster by overlaying intelligence from previous incidents


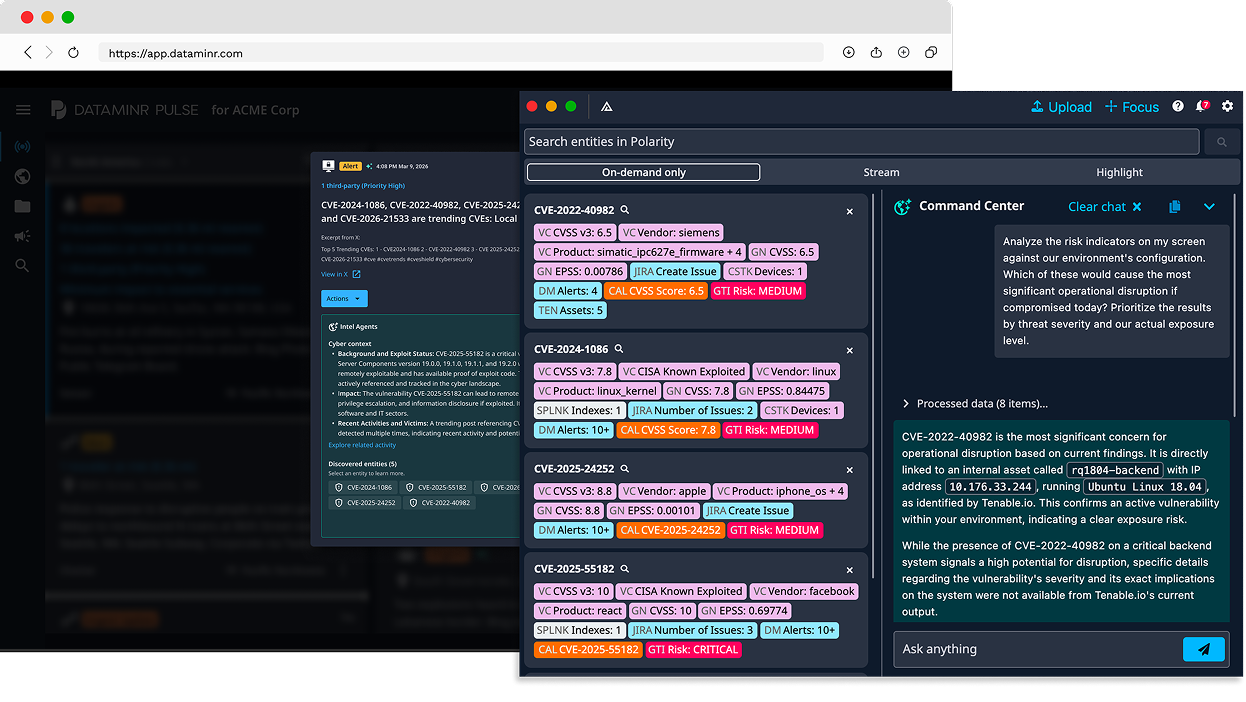
- Prioritize CVEs based on active threat campaigns and financial risk (via RQ)
- See CAL enrichment showing whether a vuln is being exploited in the wild
- Reduce ticket noise by filtering out low-priority findings


- Auto-enrich tickets with threat intel and business risk scores
- Submit RFIs or annotate key insights from the overlay
- Route tickets based on criticality, intel confidence, or team feedback

- Federated search across all sources – no query language required
- AI summaries explain the relevance of any domain, IP, file, or email
- Push new intel or annotations directly into TI Ops from any screen


Extend Your Cyber Defense with Dataminr
Investigation Insights is how intelligence reaches analysts — not in a portal, but on top of the tools they already use. It powers in-workflow delivery across two solutions.


FAQS
SIEM and SOAR enrichment runs inside those tools — you still have to be in the right console, looking at the right alert, with the right query. Investigation Insights works on top of every tool, every screen. It watches what your analyst is looking at and pulls context from 200+ connected systems automatically — including your SIEM. It doesn’t replace enrichment. It makes enrichment universal — not confined to the tools where you’ve built integrations.
No. Investigation Insights queries your tools where they already live — no data replication, no centralized ingestion, no new infrastructure. Federated search spans 200+ systems in real time. Your data stays in your tools. The overlay just makes it accessible from one screen.
Hours, not months. Cloud or on-prem. No data migration. The overlay installs on analyst machines and connects to your existing tools immediately. A Fortune 500 retailer was running in production and cutting per-indicator lookups from minutes to seconds within days.
No — that’s the point. The overlay sits on top of whatever they already use. There’s no portal to log into, no query language to memorize, no new workflow to adopt. If your analyst can see a screen, Investigation Insights can enrich what’s on it.