Instantly Correlate External Threats With Your Internal Context, Delivered In Any-Workflow.
Most threat intel tells you what’s happening on the outside. CTTI maps fast-breaking threats to your assets and exposure automatically.
57% of compromises in 2024 were detected late by external sources — not the organization’s own tools. The intelligence exists. The tools exist. The chain between them doesn’t.
Source: Mandiant 2025 M-Trends Report
The average security team runs 83 tools from 29 vendors—yet still learns about more than half of all breaches from outside the organization.¹ The problem is disconnection.
Sources: ¹ IBM Institute for Business Value, 2025 / Mandiant 2025 M-Trends Report
Most threat intel tells you what’s happening on the outside. CTTI maps fast-breaking threats to your assets and exposure automatically.

Everything in CTTI, plus automated intel ops. Fragmented signals become structured and AI-operationalized into detection and response.
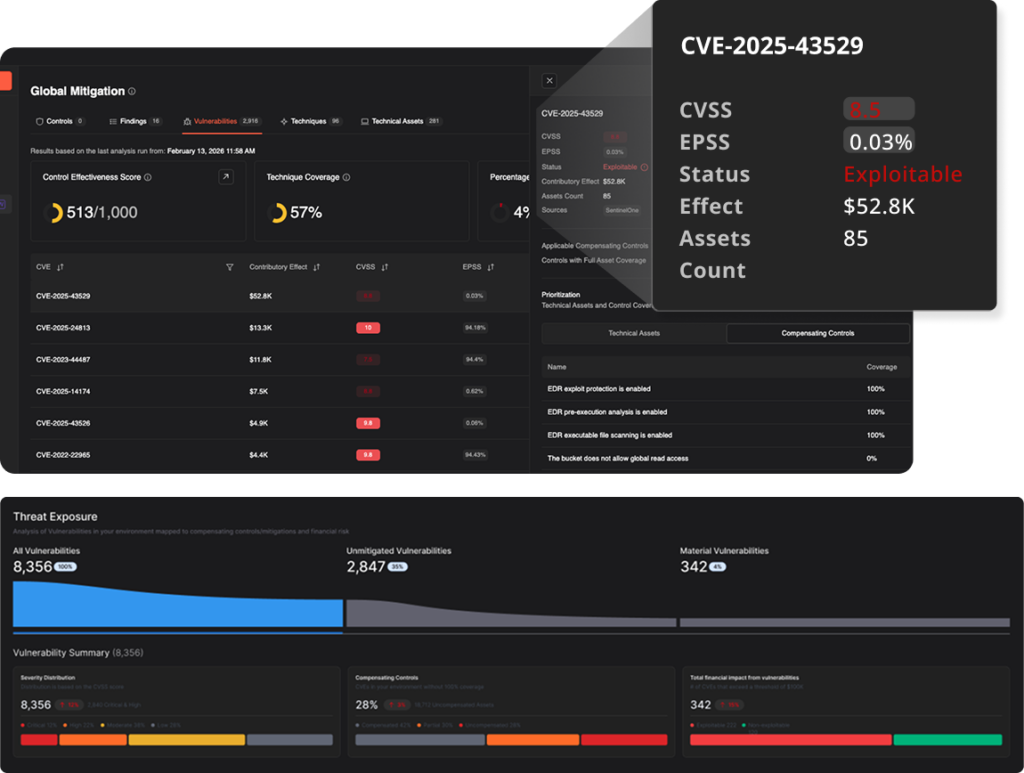
Continuous, threat-informed correlation of exploitability, control performance, and quantified risk across your attack surface.

Four integrated capabilities power the system. Each answers a different question. Each is essential on its own. Together, they provide continuous foresight, focus, and action.
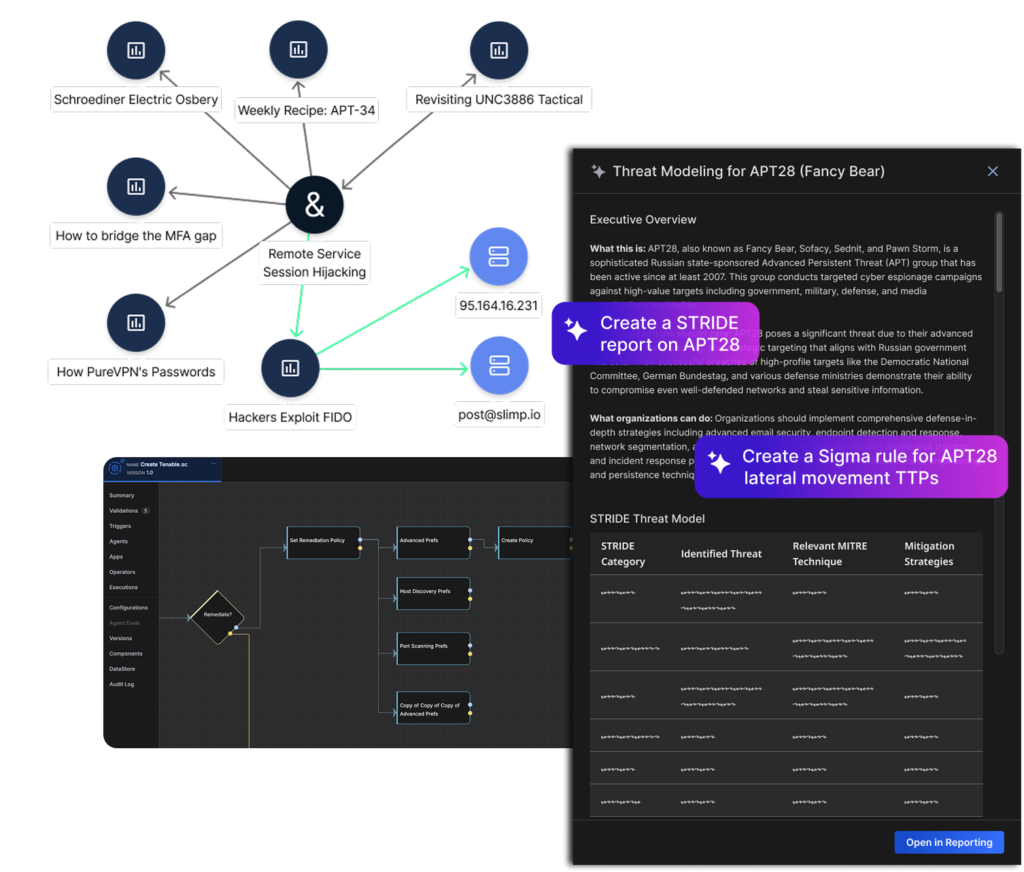
Earliest-stage threat detection across 1M+ public, deep, and dark web sources. Dataminr Intel Agents autonomously assemble rich adversary context—correlating IOCs, TTPs, CVEs, ATT&CK mappings, exploitability, and more.
Earliest-stage threat detection across 1M+ public, deep, and dark web sources. Dataminr Intel Agents autonomously assemble rich adversary context—correlating IOCs, TTPs, CVEs, ATT&CK mappings, exploitability, and more.
The scalable workflow engine to produce, manage, and operationalize intelligence—300+ sources normalized into a single threat library.
Continuously validates control effectiveness with live telemetry and translates threat exposure into probable financial loss.
We don’t replace your tools—we connect them—closing the gaps between detection, prioritization, and response that manual workflows can no longer bridge.














In 2025, Dataminr acquired ThreatConnect — one of the most widely deployed threat intelligence platforms in the market — and combined it with Dataminr’s real-time, multi-modal AI detection engine. The result: a unified system that detects threats earlier, quantifies what they cost your business, and automates response across your existing stack.
In October 2025, our AI detected an actively exploited Fortinet zero-day 38 days before CISA added it to the KEV catalog. We monitor 1M+ sources across text, image, video, and audio simultaneously — so we see signals where traditional feeds aren’t looking yet.
Most cybersecurity AI summarizes what you already have. We built 100+ specialized AI models, each trained for a specific task — detecting exploit chatter, reading malware screenshots, correlating dark web signals with your asset inventory. Our Intel Agents autonomously collect, correlate, map to MITRE ATT&CK, produce finished intelligence, and route it into your tools. Your analysts review the output instead of building it from scratch.
No. Three solutions build on each other — start where your biggest pain is. Close visibility gaps with Client-Tailored TI. Automate manual processes with Agentic TI Ops. Translate risk into financial language with Predictive Threat Exposure Management. Each delivers standalone value. They compound when connected.