Key Takeaways
- Unconfirmed but Credible Claim: A threat actor is allegedly selling a fully operational exploit kit and structured exfiltration dataset on DarkForums targeting Polymarket. The claims have not been independently verified or confirmed by Polymarket at time of publication, but the level of technical detail warrants serious attention.
- Alleged Massive Data Exposure: The purported breach encompasses 300,000+ records including 10,000 de-anonymized user profiles with full PII, on-chain wallet addresses, and internal system metadata, allegedly extracted on April 27, 2026.
- Active Sale Elevates Risk Regardless of Verification: The for-sale nature of the listing means that even if claims are partially exaggerated, functional exploit tooling targeting Polymarket’s infrastructure may already be in circulation among multiple threat actors.
- No Prior Disclosure Claimed: The actor states Polymarket has no bug bounty program and received zero notification, meaning the described vulnerabilities are unconfirmed as patched at time of publication.
Incident Overview
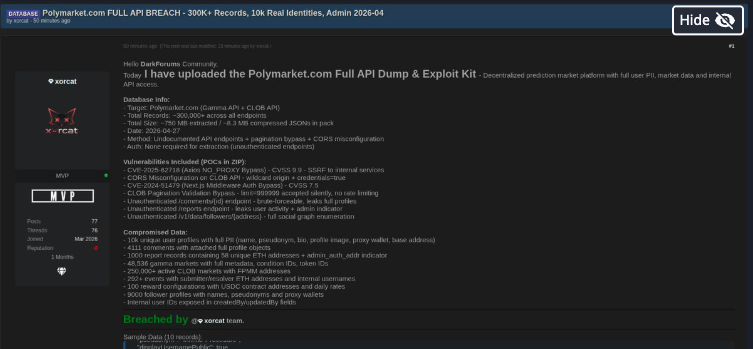
On April 27, 2026, a threat actor published what appears to be a for-sale listing on DarkForums advertising a “Polymarket Red Team Exploit Kit + Structured Exfil Dataset” targeting Polymarket.com, the decentralized prediction market platform. Polymarket has not publicly confirmed or denied the breach at time of writing, and the claims should be treated as unverified but plausible pending further investigation.
The actor claims data was extracted entirely via unauthenticated means — exploiting undocumented API endpoints, a pagination bypass, and a CORS misconfiguration across Polymarket’s Gamma and CLOB APIs — requiring no credential compromise. The explicit [SELL] designation indicates this is a commercial offering, meaning the toolkit may already be in the hands of multiple buyers if the listing is authentic.
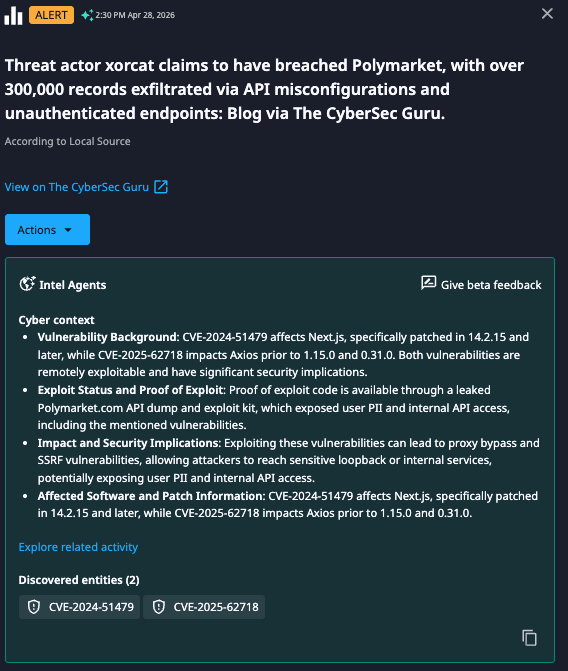
Dataminr Alert
Technical Details
The listing claims Polymarket’s full stack — Vercel serverless / Cloudflare / AWS backend, spanning production, preprod, affiliate, and CLOB API environments — was in scope. The following vulnerabilities are alleged and reportedly documented with working Python3 PoC scripts within the kit:
- CVE-2025-62718 — Axios NO_PROXY Bypass (CVSS 9.3, Critical): Allegedly enables SSRF to internal services, potentially exposing Polymarket’s AWS backend and internal service mesh.
- CORS Misconfiguration — Wildcard origin with credentials=true reportedly present on the CLOB API, enabling cross-origin credential harvesting from any domain.
- CVE-2024-51479 — Next.js Middleware Auth Bypass (CVSS 7.5): A known vulnerability that, if present and unpatched in Polymarket’s Vercel/Next.js deployment, would bypass middleware-level access controls.
- CLOB Pagination Bypass — The limit=999999 parameter is claimed to be accepted without server-side validation or rate limiting, enabling bulk data harvesting.
- Unauthenticated Endpoints — /comments/{id}, /reports, and /v1/data/followers/{address} are alleged to be accessible without authentication, exposing full user profiles, an admin_auth_addr indicator, and complete social graph data respectively.
Sample dataset filenames referenced in the listing include markets.json, rewards.json, gamma_series.json, reports_leak.json, and profiles.json. The kit is also said to include an auto-dump script for continuous data harvesting and a MITRE ATT&CK-mapped red team report. These contents have not been independently verified by Dataminr.
Immediate Actions & Recommendations
Given that these claims are unverified, organizations should treat the following as precautionary measures proportional to the credibility of the threat, rather than confirmed incident response steps.
For Polymarket and organizations running analogous Web3 / DeFi platforms:
- Conduct an Emergency API Audit: Enumerate all public-facing API endpoints across production, preprod, and affiliate environments and verify authentication is enforced, particularly on endpoints matching the patterns described (/comments/{id}, /reports, /v1/data/followers/{address}).
- Review CORS Policy: Audit all APIs accepting credentialed requests for wildcard origin configurations and enforce a strict server-side Origin allowlist.
- Assess CVE-2024-51479 Exposure: Determine whether the deployed Next.js version is vulnerable to the middleware authentication bypass and apply available patches if so.
- Assess CVE-2025-62718 Exposure: Review Axios configurations for NO_PROXY bypass risk and apply available mitigations to prevent potential SSRF against internal AWS services.
- Enforce API Rate Limiting and Pagination Controls: Impose server-side maximum page size limits and introduce rate limiting with anomaly alerting across all paginated endpoints.
- Treat admin_auth_addr as Potentially Compromised: As a precautionary measure, audit for unauthorized administrative access and consider rotating associated credentials pending investigation.
- Monitor On-Chain Activity: Implement alerting for anomalous transactions involving wallet addresses and USDC contract addresses that may be represented in the alleged leaked dataset.
- Prepare User Notification Contingency: Draft breach notifications per applicable regulatory requirements (GDPR, CCPA) in the event the breach is confirmed, and consider proactively alerting users to elevated phishing and social engineering risk.
- Establish a Bug Bounty Program: Regardless of whether this specific claim is verified, the absence of a disclosed vulnerability reporting channel creates conditions that incentivize commercial exploitation over responsible disclosure.
For peer organizations:
- Treat the potential availability of this exploit kit as an active threat signal. Proactively audit your own API surfaces for analogous unauthenticated endpoints, CORS misconfigurations, and unpatched Next.js middleware vulnerabilities, particularly if operating on similar Vercel/Cloudflare/AWS infrastructure stacks.

2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report