From First Signal to Finished Intelligence — Automatically.
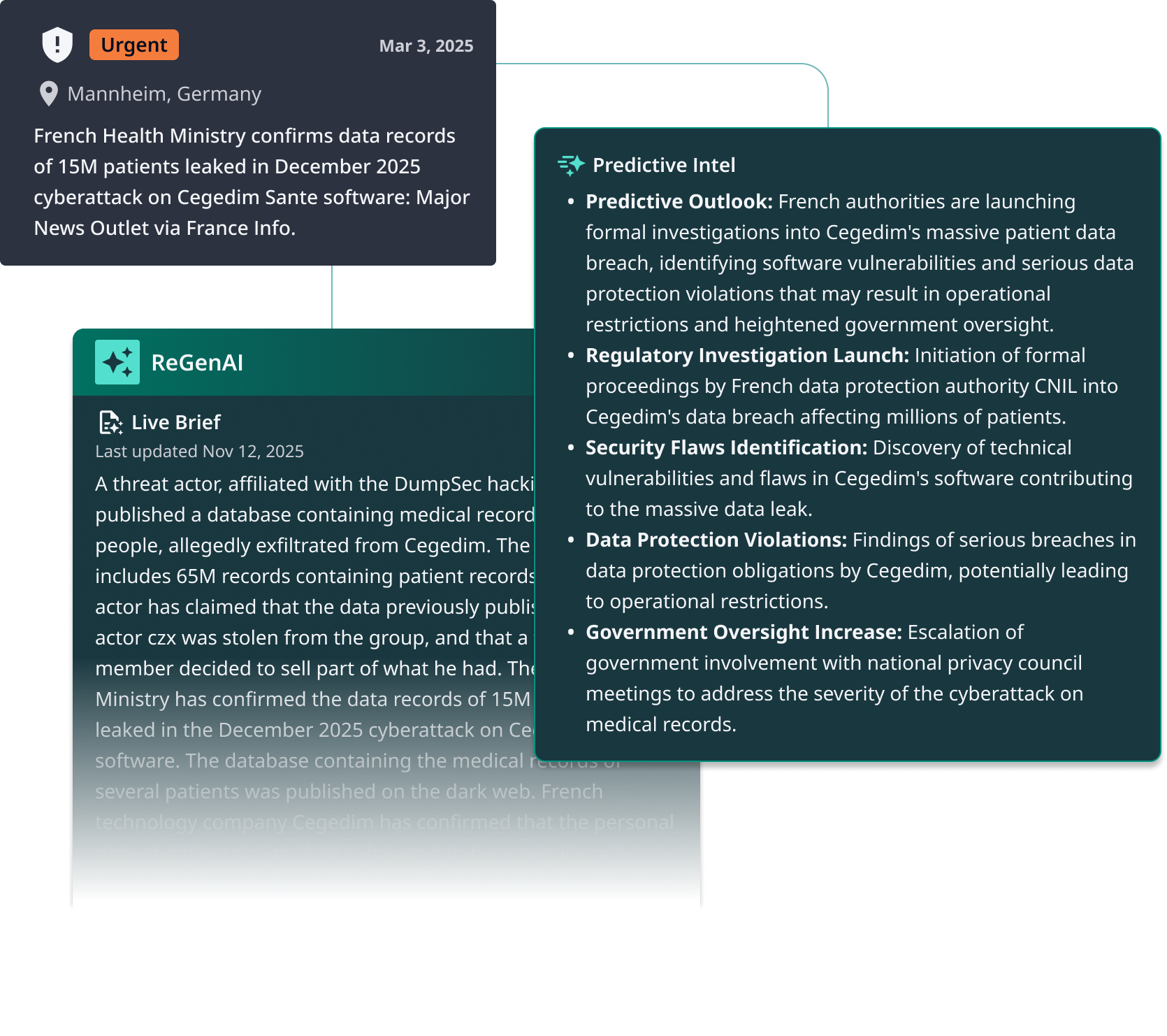
Legacy TIPs aggregate feeds. Analysts still do the rest. Agentic TI Ops changes that — Intel Agents detect early signals, assemble finished intelligence, and operationalize it downstream into detection, response, and hunting workflows. Analysts stay in control of judgment. Agents handle the labor.
Core Platform Capabilities
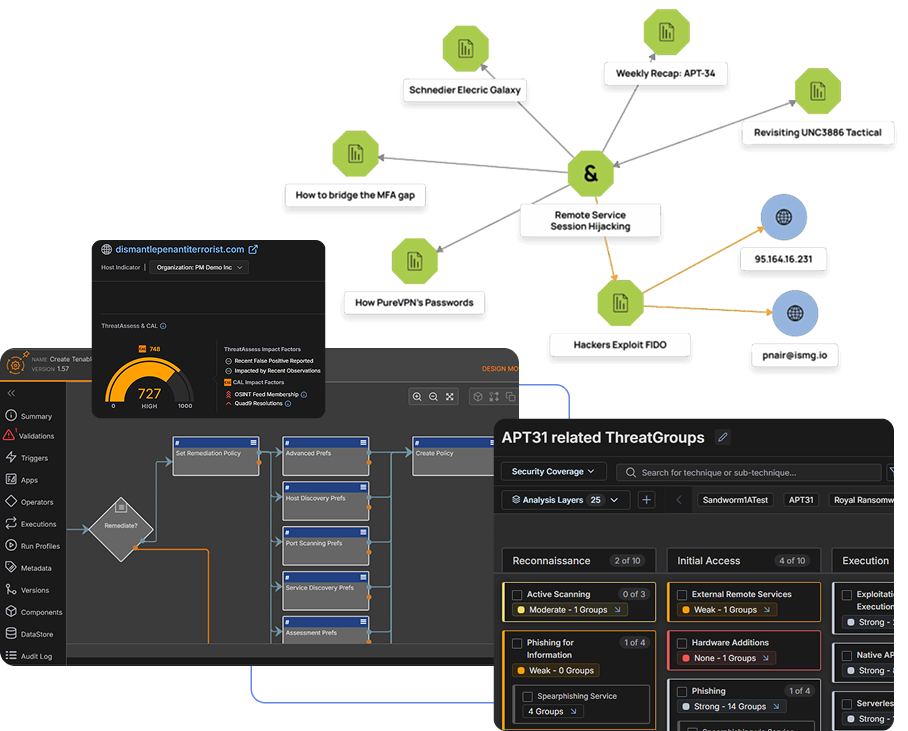
Agentic TI Ops builds on Client-Tailored Threat Intelligence, adding an operational layer where Intel Agents don’t just assemble intelligence — they structure it, apply it downstream, and get smarter about your environment over time. Three capabilities work together — the operational backbone that keeps intelligence moving, not sitting in a queue.
Turn Security Into Strategy Today

Core Features
Over 100 specialized AI models work in parallel—not through a single LLM. Multi-Modal Fusion AI processes text, images, video, and audio across 43+ TB of daily data from 1M+ public sources.
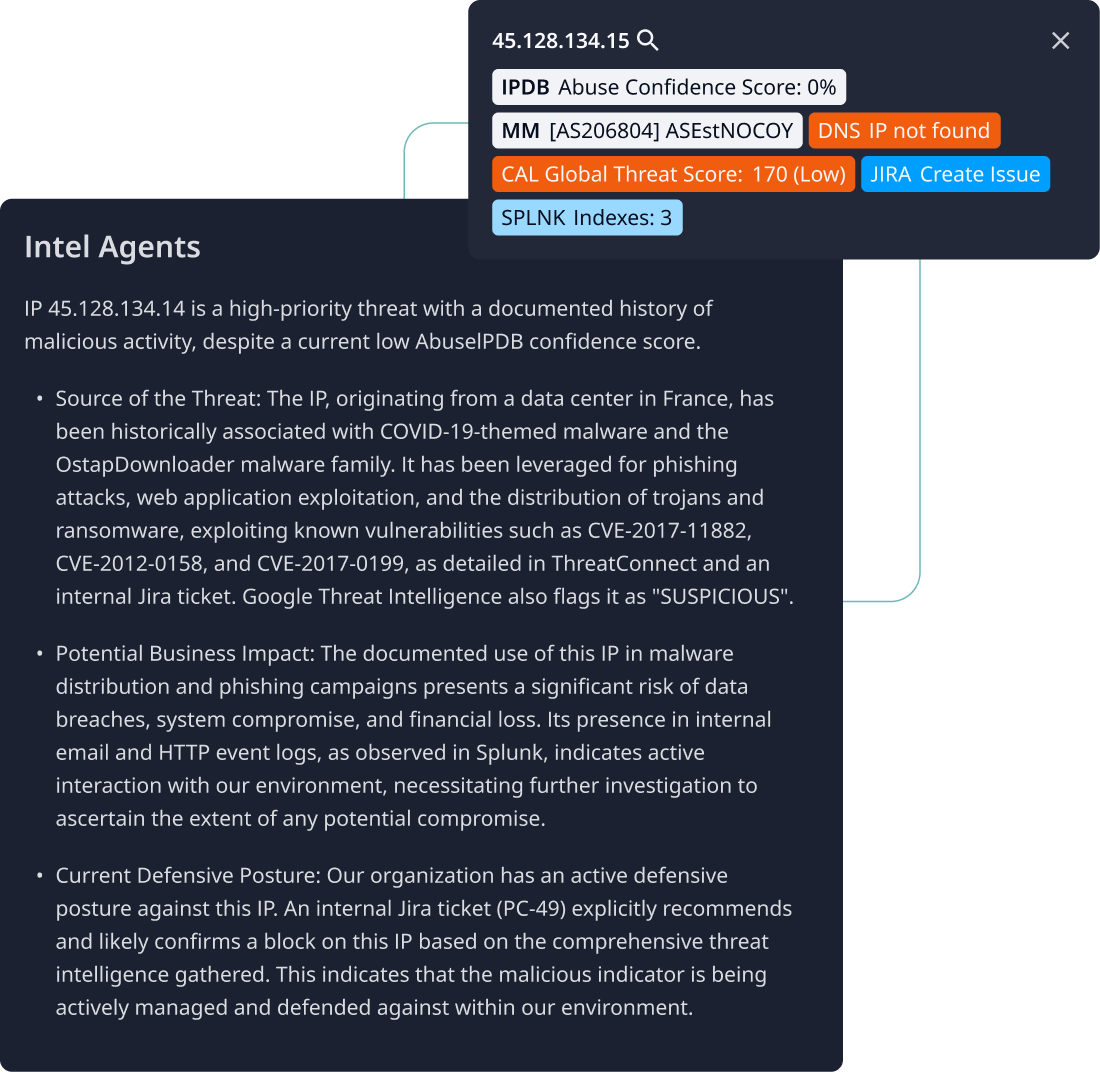
Intel Agents assemble evolving intelligence and operationalize it — correlating actors, TTPs, and infrastructure, then routing finished intel downstream into detection and response. Build custom agents trained on your stack so automation becomes an expert on your environment.
Intelligence is produced once, structured in a unified threat library, and reused across detection, response, and reporting. 60+ automations saved one customer $1.3M per year.
All threat intelligence—including third-party feeds—is delivered directly into analyst workflows. Eliminate disconnected portals and data silos with a single, unified view.
External intelligence overlaid with internal context from connected SIEM, EDR, ticketing, and hunt consoles. Conduct federated searches across 150+ systems without learning complex query languages.
Get Started
Your team can be operational within days, not months. Intel Agents start assembling intelligence the moment data flows in — no rearchitecting required.
Grow With Us
As intelligence operations mature, Agentic TI Ops compounds value — better models, faster results.
A Force Multiplier for Your Existing Security Stack
We don’t replace your tools — we connect them — closing gaps between detection, prioritization, and response that manual effort and additional feeds can’t bridge.
- Push pre-disclosure IOCs and adversary TTPs directly into correlation and detection rules — before threats reach commercial feeds.
- Enrich SIEM alerts in real time with threat context and financial risk scoring.
- Reduce false positives by filtering signals through client-tailored relevance, not just pattern matching.

- Trigger response playbooks directly from intelligence signals — no manual handoff between detection and action
- Feed financial risk scores into incident workflows so responders prioritize by business impact, not alert volume
- Capture analyst decisions to continuously improve automation logic


- Correlate endpoint detections with active adversary TTPs from real-time intelligence
- Prioritize endpoint alerts based on probable financial impact, not severity score alone
- Block threats with higher confidence using intelligence that’s already been tailored to your environment


- Tie vulnerabilities to active adversary campaigns so remediation follows real threat activity, not CVSS rankings
- Surface the exposures with the highest probable financial loss — the ones that actually warrant emergency action
- Map controls and assets for enterprise-wide visibility into what’s protected, what’s drifted, and what’s exposed




- Associate users, devices, and assets to uncover risky access paths that threat actors are actively exploiting
- Quantify identity-driven exposure in dollars and prioritize remediation by business impact


- Ingest firewall, NDR, and data lake telemetry to model real-time exposure across on-prem and cloud
- Correlate network traffic patterns with adversary techniques tracked in our intelligence
- Extend Foresight, Focus, and Action across hybrid environments and multi-cloud workloads


FAQS
A TIP is a system of record — it manages intelligence after analysts produce it. Agentic TI Ops includes a full TIP, but adds real-time detection from 1M+ sources, Intel Agents that produce finished intelligence automatically, and in-workflow delivery so analysts work from one screen.
Most AI security products apply AI at the surface — summarizing alerts after the fact. Intel Agents operate autonomously using 100+ specialized models in parallel: multi-modal fusion, entity extraction, client-tailoring, and correlation — compressing hours of analyst work into seconds while threats are still forming.
Teams can be operational within days. Intel Agents start assembling intelligence the moment data flows in, and Investigation Insights overlays context inside existing tools without replacing them. No rearchitecting, no new portals. A Forbes 2000 healthcare system cut incident response from 7 hours to 37 minutes.
Customers report measurable outcomes: 200M SIEM events narrowed to 12 actionable incidents monthly, incident response cut from 7 hours to 37 minutes, $1.3M per year saved through workflow automation, and 74% of surveyed customers reported 25%+ false positive reduction. Results compound as intelligence matures.