Key Takeaways
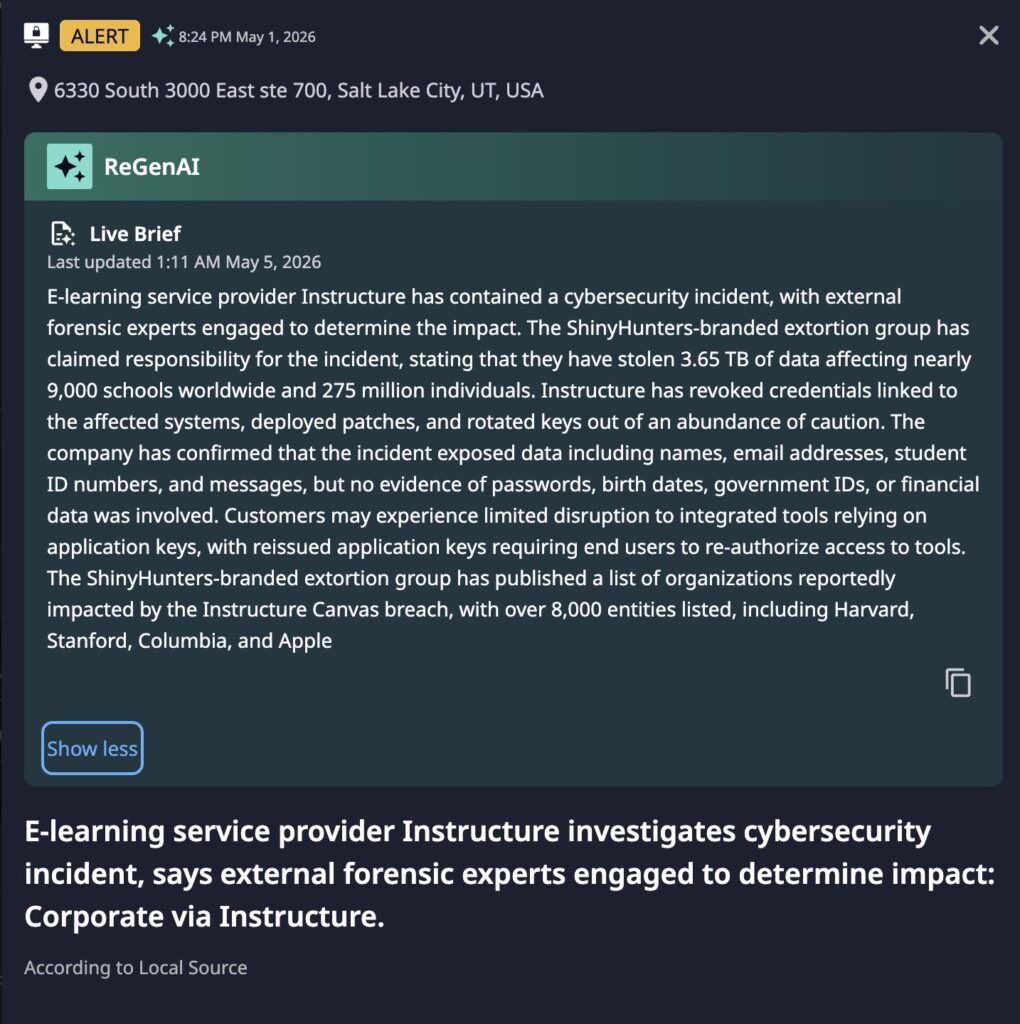
- Massive Scale: ShinyHunters claims to have exfiltrated 3.65 TB of data, with over 8,000 affected organizations listed publicly, including Harvard, Stanford, Columbia, and Apple.
- Sensitive PII Exposed: Confirmed exposed data includes names, email addresses, student ID numbers, and messages. Instructure states no passwords, government IDs, birth dates, or financial data were involved.
- Containment Underway: Instructure has revoked affected credentials, rotated application keys, and deployed patches, though end users of integrated tools may experience re-authorization disruptions.
- High-Profile Extortion Pattern: This attack is consistent with ShinyHunters’ established model of large-scale data theft followed by public victim listing as leverage for extortion.
Incident Overview
On May 1, 2026, Dataminr detected an alert indicating that Instructure was investigating a cybersecurity incident. External forensic experts have been engaged to assess the full scope of the breach.
ShinyHunters group subsequently claimed responsibility, asserting that 3.65 TB of data was exfiltrated, impacting approximately 275 million individuals across roughly 9,000 educational and corporate institutions globally. Instructure has confirmed unauthorized access occurred and that exposed data includes names, email addresses, student ID numbers, and messages, while stating there is no current evidence that passwords, birth dates, government IDs, or financial records were compromised.
Technical Details
Instructure has confirmed the following containment actions have been taken:
- Credentials linked to affected systems have been revoked.
- Application keys have been rotated, which may require end users to re-authorize access to integrated third-party tools.
- Patches have been deployed to remediate the identified vulnerability or misconfiguration.
The method by which ShinyHunters exfiltrated 3.65 TB without detection, and the duration of access, remain under investigation.
About Instructure & Canvas Primary Clients
Instructure is an educational technology company founded in 2008 and headquartered in Salt Lake City, Utah. It develops and publishes Canvas, the world’s most widely deployed learning management system (LMS), now operating across more than 100 countries following a $4.8 billion acquisition by KKR and Dragoneer in 2024.
Higher education (primary)
~50% of US/Canadian higher ed enrollment; used by thousands of universities globally including Harvard, Stanford, Columbia, MIT, and the entire Ivy League except Princeton
Highest density of affected users; adult students and faculty PII
K–12 schools (fast-growing)
2,000+ US districts; dominant in large districts; K–12 market leader by enrollment share
Includes minors — triggers COPPA (updated April 22, 2026) alongside FERPA; parental notification obligations
Corporate & workforce learning
Large enterprises incl. Apple; manufacturing, healthcare, financial services
Employee and partner PII; corporate training credentials exposed
Government & public sector
State agencies (e.g. State of Wyoming), public health (e.g. LACDPH)
Government employee data; potential security-clearance adjacency
Healthcare & professional certification
Health systems (e.g. Atrium Health), professional bodies (e.g. PGA)
Healthcare worker credentialing data; HIPAA adjacency possible
Victim Description & Potential Impact by Segment
Higher education — students, faculty, and staff
This is Canvas’s largest and most concentrated user base. Affected individuals are likely to include undergraduate and graduate students, faculty, academic staff, and administrators at universities globally. Confirmed exposed data — names, institutional email addresses, student ID numbers, and direct messages — is sufficient to enable highly targeted spear-phishing, account takeover attempts, and identity fraud. ShinyHunters’ public listing of Harvard, Stanford, Columbia, and other elite institutions on its leak site appears designed to maximize reputational pressure and accelerate extortion; those listings have not been independently confirmed as verified breach victims.
K–12 students — elevated risk due to minor status
This segment carries the highest regulatory and reputational risk. Canvas serves elementary through high school students, meaning that if the attacker’s claimed scale is confirmed, a material portion of affected individuals would be minors, including children under 13. Even at a fraction of the alleged scale, COPPA exposure is significant: the FTC’s updated COPPA rule (effective April 22, 2026) tightens consent and breach notification requirements for under-13 data and carries penalties up to $51,744 per affected child. State-level laws — including New York Education Law 2-d, California’s SOPIPA, and approximately 130 analogous statutes — impose additional vendor-specific notification and security obligations independent of FERPA. The PowerSchool breach of January 2025 (62 million student records; $17.25 million settlement; class actions in 11 states) provides the closest comparable precedent.
Corporate and enterprise users
Employees of organizations using Canvas for workforce training — including large enterprises such as Apple and healthcare systems such as Atrium Health — may have PII exposed. For these users, the risk profile differs from the student population: exposed corporate email addresses and employee IDs may enable business email compromise (BEC) attacks, credential stuffing against enterprise systems, and targeted social engineering of high-value employees.
Government and public sector users
State agencies and public health bodies using Canvas for training and compliance programs may have government employee records in scope. Depending on the roles and clearance levels of affected users, exposure of institutional email addresses and user IDs may have national security adjacency that warrants coordination with relevant authorities.
Healthcare-adjacent users
Health systems and professional certification bodies using Canvas for credentialing, continuing education, or compliance training may have data in scope. Where Canvas is integrated with HIPAA-covered systems or stores data about healthcare workers’ credentials, institutions should assess whether the breach triggers obligations under HIPAA’s breach notification rule in addition to FERPA.
Prior Incident Context — Pattern of Targeting
This is Instructure’s second confirmed ShinyHunters breach in eight months. In September 2025, Instructure disclosed a separate incident in which a social engineering attack gave threat actors access to its Salesforce instance. According to reporting at the time, Instructure indicated that no Canvas product data was accessed in that incident, though this characterization has not been confirmed in primary Instructure statements available as of this writing. ShinyHunters claimed responsibility for the September 2025 incident before Instructure had completed its investigation — a pattern consistent with their established extortion playbook.
Two confirmed breaches in eight months, attributed to the same threat actor, raises material questions about the adequacy of remediation steps taken after the first incident — particularly given that both breaches appear to involve Salesforce infrastructure and/or credential-based access rather than direct network intrusion, though Instructure has not confirmed the access path for the May 2026 incident. Institutions should request documentation from Instructure addressing what specifically changed after the September 2025 breach and why those controls did not prevent the May 2026 incident.
Canvas joins PowerSchool and Infinite Campus in a documented pattern of ShinyHunters — operating under the Scattered LAPSUS$ Hunters (SLH) banner, which Trustwave SpiderLabs assesses as a situational alliance rather than a formal merger — targeting edtech platforms through Salesforce environments and credential compromise. The structural vulnerability is consistent: a single SaaS provider holding records on tens of millions of students across thousands of institutions is compromised through a single account or integration, and every dependent institution inherits the breach simultaneously.
Threat Actor & Motivation
ShinyHunters is a well-documented financially motivated extortion group and a prominent member of “The Com” cybercrime ecosystem, now operating within the Scattered LAPSUS$ Hunters (SLH) alliance alongside LAPSUS$ and Scattered Spider. Their primary motivation is financial gain through large-scale data theft followed by public shaming, victim listing on dark web leak sites, and extortion demands.
The group has a demonstrated history of targeting large platforms with broad user bases — including prior incidents involving Salesforce customer data and Snowflake environments — as these provide maximum extortion leverage due to the downstream impact on thousands of dependent organizations. The public listing of 8,000+ victim entities, including high-profile names such as Harvard, Stanford, and Apple, is consistent with their established pressure tactics.
Third-Party & Supply Chain Risk
1. Integrated tool credential compromise
All API keys, OAuth tokens, and service accounts connected to Canvas prior to Instructure’s key rotation must be treated as potentially compromised. LTI apps, SSO integrations, analytics platforms, SIS connectors, and any tool that authenticated into Canvas inherits this exposure. Given Canvas’s 1,000+ integration ecosystem, the blast radius extends well beyond Instructure’s own infrastructure.
2. Re-authorization as a social engineering vector
Instructure’s forced key rotation will prompt end users to re-authorize connected tools. Threat actors can exploit this window by sending spoofed re-auth emails that are indistinguishable from legitimate prompts. This window is exceptionally high-risk for credential harvesting across the entire Canvas ecosystem.
3. Downstream notification obligations for sub-tenants
Organizations acting as Instructure resellers, managed service providers, or sub-tenant Canvas operators may carry independent notification obligations to their own end users under FERPA, COPPA, GDPR, or contractual data processing agreements. Review DPAs immediately.
4. Lateral SSO exposure
If your Canvas environment shares federated identity with other enterprise platforms, assess whether the same credential scope creates lateral risk across those systems. Prior SLH targeting patterns show coordinated multi-platform exfiltration following initial access.
5. Integration exposure by category
SSO / Identity provider
Federated credential scope across platforms
Critical
LTI / EdTech apps
Direct API access to student data
High
SIS / ERP connectors
Student record and enrollment data
High
Analytics / BI tools
Data export and reporting credentials
Medium
Storage / content tools
File access tokens
Medium
Regulatory Framework — Obligations by Segment
FERPA (US)
All US educational institutions
Notify affected families of unauthorized PII disclosure; assess whether breach constitutes reportable event
COPPA (updated Apr 22, 2026)
K–12 institutions with users under 13
Tightened breach notice; penalties up to $51,744 per affected child; parental notification obligations
State student privacy laws
~130 state statutes (NY Ed Law 2-d, CA SOPIPA, etc.)
Vendor-specific notification and security duties; independent of FERPA; state AG enforcement
GDPR (EU/EEA)
EU institutions and users
Notify supervisory authority within 72 hours; assess data subject rights obligations
HIPAA (US)
Healthcare-adjacent Canvas users
Assess whether Canvas integration with covered systems triggers breach notification rule
GDPR / equiv. (100+ countries)
International institutions
Local data protection authority notification; data subject rights; cross-border transfer assessment
Immediate Actions & Recommendations
- Verify Your Organization’s Exposure: If your organization uses Canvas or any Instructure product, immediately confirm with your IT or vendor management team whether your institution appears on the published victim list and assess what data may have been involved.
- Rotate all integration credentials. Treat every API key, OAuth token, and service account present before Instructure’s rotation as compromised. Audit and reissue across all connected tools — prioritizing SSO, LTI apps, and SIS connectors.
- Check for lateral SSO exposure. If Canvas shares SSO with other enterprise platforms, assess whether the same credential scope creates risk across those systems immediately.
- Monitor for Phishing: With names, email addresses, and student/user IDs exposed, expect a surge in highly targeted phishing campaigns directed at your faculty, students, and staff. Issue an immediate user awareness advisory.
- Issue phishing advisory — segment by audience. Higher education, K–12 parent/guardian, and corporate user populations each require tailored messaging. Provide verified re-auth channels and explicitly warn against unsolicited re-authorization links, which threat actors will use to exploit the expected disruption window.
- Reassess Instructure’s vendor risk tier. A breach of this confirmed scope — and alleged scale — following a prior breach by the same actor, warrants re-tiering in your vendor registry. Consider pausing new data-sharing agreements pending forensic findings. Request updated SOC 2 status and breach attestation documentation.
- Engage Instructure Directly: Request a formal breach notification and scope assessment from Instructure to understand the precise data elements exposed for your user population, which will inform your regulatory notification obligations (e.g., FERPA, GDPR).
- Assess Regulatory Obligations: Given the exposure of student PII, institutions subject to FERPA (US), GDPR (EU), or equivalent frameworks should immediately engage legal and compliance teams to assess notification timelines and requirements.
- Assess COPPA obligations if you serve K–12. The FTC’s updated COPPA rule (effective April 22, 2026) applies to under-13 user data and carries per-child penalties. Engage legal counsel immediately to assess notification timelines and parental notification obligations under federal and applicable state student privacy laws.
- Engage legal and compliance for FERPA / GDPR / applicable frameworks. Map your affected user populations to the regulatory frameworks in the table above. Document response steps now — regulators will ask for them. If you operate sub-tenants or serve as a data processor for other institutions, review your DPAs for independent obligations.

2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report