Key Takeaways
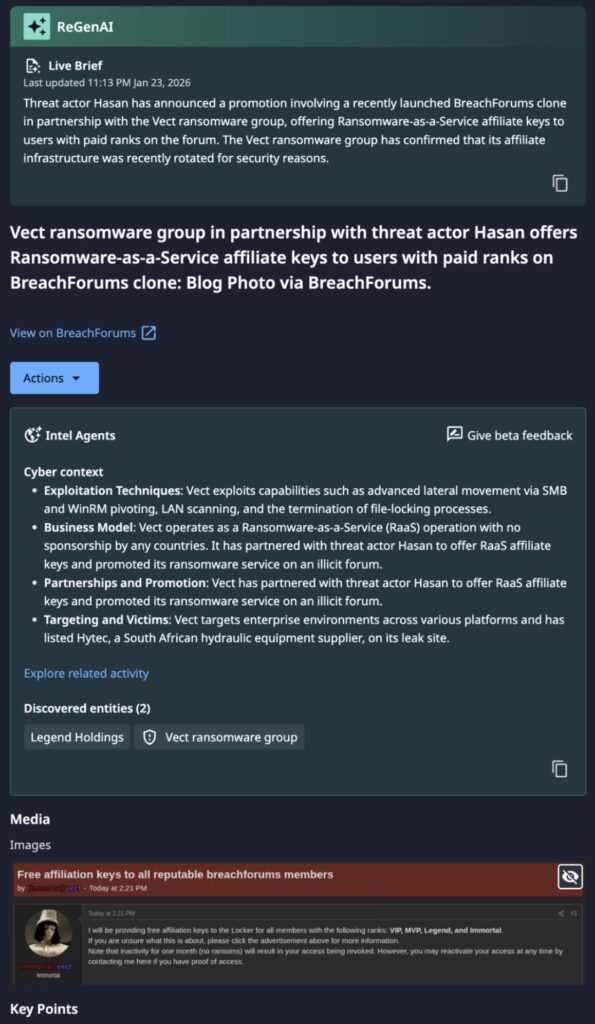
- The Vect ransomware group has formalized partnerships with the BreachForums cybercrime marketplace and TeamPCP hacking group. Between the two partnerships, Vect will lower the barrier to entry for ransomware actors, incentivize group members to carry out attacks, and exploit pre-existing breaches to broaden impact.
- The convergence of large-scale supply chain credential theft, a maturing RaaS operation, and mass dark web forum mobilization represents an unprecedented model of industrialized ransomware deployment.
- Organizations exposed to any phase of the recent TeamPCP campaign targeting the digital supply chain must treat credential rotation as an immediate operational priority.
- Named victims on Vect’s leak site include Guesty (property management technology, ~700 GB alleged exfiltration tied to the TeamPCP LiteLLM/Trivy campaign), USHA International Limited (Indian manufacturing, employee data and SAP databases), and S&P Global (alleged; unconfirmed by third parties at time of publication).
Incident & Threat Actor Overview
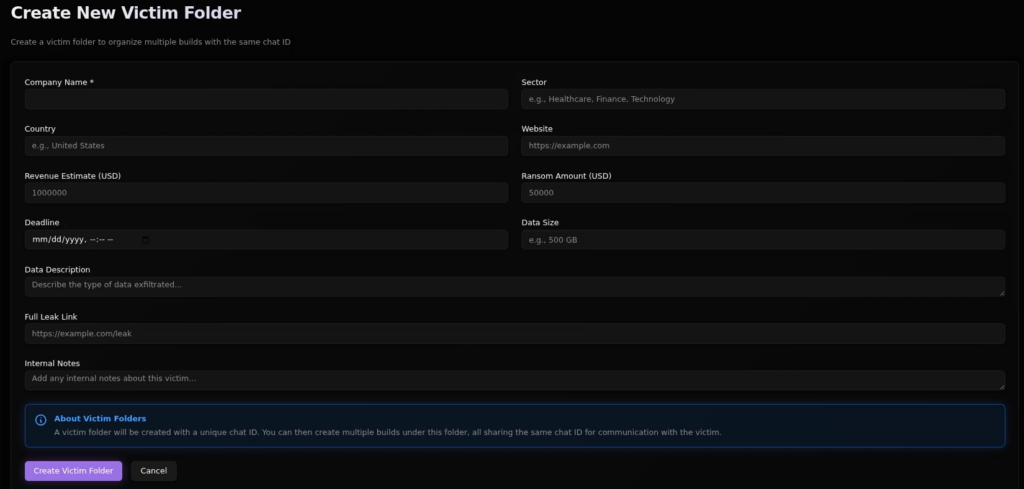
Vect is an emerging ransomware-as-a-service (RaaS) operation that first surfaced in late December 2025 through affiliate recruitment activity, with active victim targeting beginning in early January 2026. In February 2026, their next iteration launched with a more structured affiliate program and expanded infrastructure. The group operates a classic double-extortion model, exfiltrating data prior to encryption and publishing it on a TOR-based leak site when ransom demands go unmet.
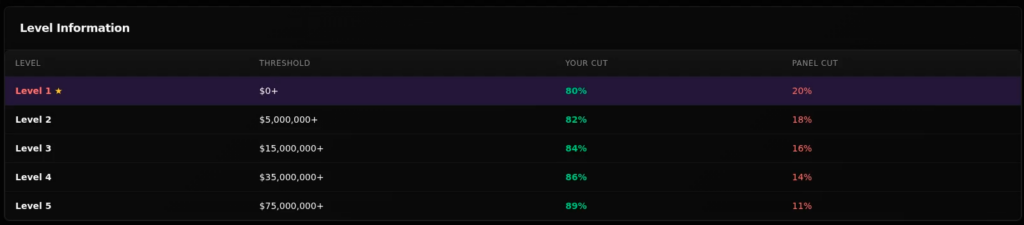
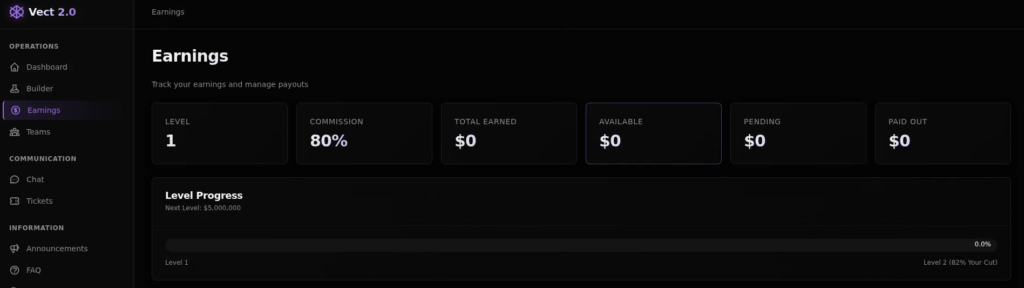
Vect’s operational maturity — purpose-built tooling, TOR-only infrastructure, Monero payment processing, TOX-based affiliate communications, and a structured multi-tier affiliate program — indicates it is run by experienced ransomware operators, possibly representing a rebrand or spinoff of an established group. The CIS affiliate fee waiver is consistent with a Russian-speaking operational base, a pattern common across major RaaS ecosystems.
On April 16, 2026, Dataminr detected affiliate key distribution as part of a formal operational partnership between BreachForums and Vect, which had been announced and infrastructurally established earlier. This was coupled with a previously announced alignment between Vect and TeamPCP, a threat actor that had aggressively targeted open-source security tooling throughout March 2026. At least one confirmed Vect ransomware deployment using TeamPCP-sourced credentials has been reported, signaling a concrete shift from credential harvesting to active monetization.
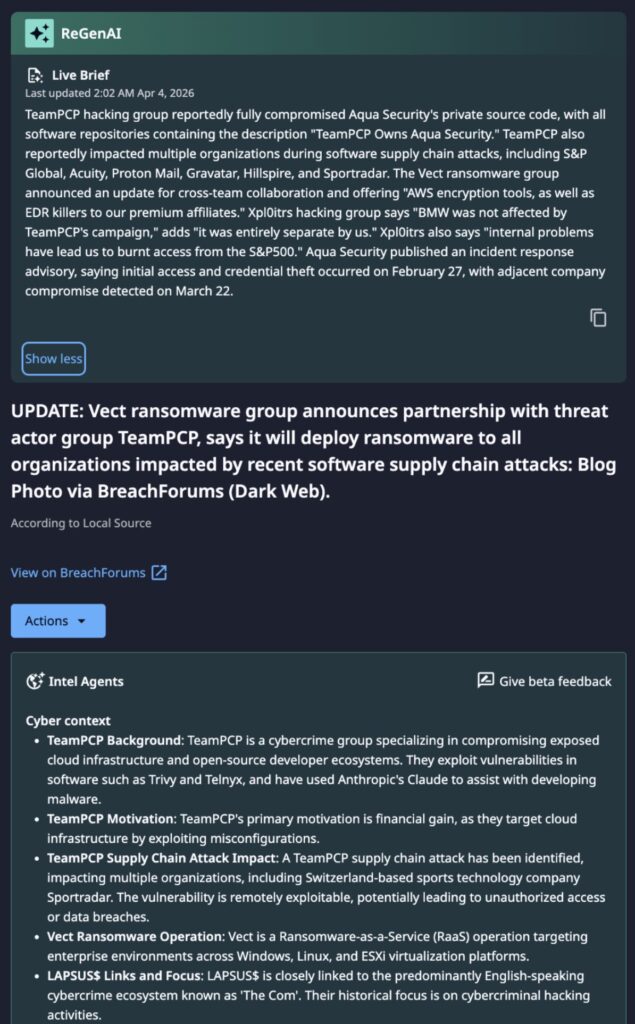
TeamPCP is a financially-motivated group that has operated under multiple confirmed aliases including PCPcat, DeadCatx3, and Persy_PCP. TeamPCP have previously created and promoted ransomware brands such as Black Witch and CipherForce. TeamPCP’s advertised CipherForce ransomware-branded tooling was designed to encrypt all major enterprise database and cloud storage solutions. Their ShellForce was an additional persona put into operation to leak and sell exfiltrated data.
TeamPCP has also operated in cooperation with other threat actor groups such as xpl0itrs, DarkRomance by extension, and the ShinyHunters-branded extortion group linked to Scattered Lapsus$ Hunters. Notably, SLH also previously amplified content from a Black Witch ransomware-associated user. More recently as of April 2026, the group has repeatedly claimed their desire is to focus on providing initial access to other threat actor groups. TeamPCP transitioned from cryptomining and opportunistic access operations in 2024-2025 to a focused, high-tempo supply chain compromise model in early 2026.
BreachForums is one of the most active English-language cybercrime marketplaces, functioning as a centralized hub for the buying and selling of stolen data, credentials, and hacking tools. It emerged as the successor to RaidForums following that platform’s law enforcement seizure in 2022, and has since grown to approximately 300,000 registered users. The forum serves as a primary distribution and monetization channel across the broader cybercrime ecosystem, facilitating coordination between threat actors, initial access brokers, and ransomware operators. The most recent iteration operated by threat actor Hasan serves as a breakaway from the administration and codebase of previous BreachForums iterations, with historical user databases from previous iterations imported to facilitate migration to this splinter forum.
Technical Details
As part of this expanded partnership model and expanded infrastructure, Vect has both enabled BreachForums members to deploy ransomware more easily and will use the victims of TeamPCP’s supply chain attacks to attack organizations that are in a vulnerable state. The following should be noted about Vect’s purpose-built ransomware
- Malware Construction: Vect’s ransomware is purpose-built in C++, not derived from leaked source code from prior groups such as LockBit or Conti. This distinguishes it from the majority of current RaaS offerings.
- Encryption: The malware uses the ChaCha20-Poly1305 AEAD algorithm with intermittent file-level encryption, scrambling only portions of each file to prioritize speed and operational disruption.
- Multi-Platform Targeting: Vect explicitly targets Windows, Linux, and VMware ESXi environments.
- Defense Evasion: The malware manipulates Windows Safe Mode boot settings to suppress security tooling and terminates security, backup, and database processes immediately prior to payload execution.
- Lateral Movement: Propagation occurs via SMB and WinRM pivoting. Built-in LAN scanning enables automated network reconnaissance following initial access.
With BreachForums, Vect will be giving its roughly 300,000 registered members set to receive personal affiliate keys, a Monero-only multi-signature escrow system that is nearly ready for deployment, and a tiered incentive structure offering elite affiliates increased ransom revenue splits and cloud locker access.
With TeamPCP — the threat actor responsible for a string of cross-ecosystem supply chain compromises targeting Trivy, Checkmarx KICS, LiteLLM, and the Telnyx Python SDK — the two groups intend to with stated intent to deploy ransomware across every organization impacted by those campaigns. The partnership will likely work in the following way:
- TeamPCP Supply Chain Access: TeamPCP’s payloads, injected into GitHub Actions workflows and PyPI packages, were able to harvest cloud credentials, API keys, SSH keys, and CI/CD tokens at scale. A secondary persistence mechanism abused victims’ own GitHub tokens to create concealed repositories within their organizations.
- Parallel Ransomware Tracks: TeamPCP is simultaneously operating its own proprietary ransomware program, CipherForce, alongside the mass Vect affiliate deployment, indicating dual monetization channels from a single pool of compromised credentials.
What is Novel About This Partnership?
The Vect/TeamPCP/BreachForums arrangement sits on a continuum of cybercrime industrialization that has been building since at least 2020. The underlying concept of an access broker feeding a ransomware operator is well-established. What is new is the combination of supply chain sourced access, mass public affiliate mobilization, and forum-integrated operational infrastructure, applied simultaneously and at a scale that has no direct precedent in the documented history of ransomware partnerships. Three things distinguish this arrangement from its predecessors and make the assessment of it as “unprecedented” credible:
Scale of affiliate mobilization. Prior IAB-to-RaaS arrangements were private, bilateral, and operated through quiet forum transactions or encrypted channels. The Vect/BreachForums partnership is the opposite — a public, mass-enrollment model explicitly designed to convert all 300,000 registered BreachForums members into active affiliates simultaneously. No prior ransomware operation has attempted to mobilize a cybercrime forum’s entire user base as a distribution network in a single announcement. The closest analogue is the Conti affiliate program, which was large but still operated through selective recruitment rather than blanket enrollment.
Supply chain as the access vector. Prior IAB partnerships sourced access through conventional means — phishing, exposed RDP, credential stuffing, VPN exploitation. TeamPCP’s access was generated through the poisoning of trusted open-source security tools embedded in enterprise CI/CD pipelines at scale. This means the access being handed to Vect affiliates was harvested from the inside of enterprise build environments, not from perimeter compromise — a fundamentally different quality and quantity of access than the IAB market has historically traded in.
Forum as operational infrastructure. BreachForums is not just a distribution channel here — it is being positioned as operational infrastructure for ransomware deployment, with escrow, affiliate support, and key distribution built into the forum itself. Prior forum involvement in ransomware operations was primarily reputational (posting victim claims, advertising affiliate programs). The Vect model integrates the forum into the operational pipeline in a way that has not been previously documented at this scale.
Immediate Actions & Recommendations
- Rotate All Credentials Immediately: Any organization that incorporated Trivy GitHub Actions, Checkmarx KICS, LiteLLM v1.82.7/1.82.8, or Telnyx SDK v4.87.1/4.87.2 into CI/CD pipelines during March 2026 should treat all secrets in those environments as compromised — cloud provider credentials (AWS, GCP, Azure), API keys, SSH keys, GitHub PATs, and Kubernetes tokens.
- Audit CI/CD Pipeline Dependencies: Review pipeline configurations and dependency files for the affected package versions above. Pin all dependencies to verified, hash-validated versions and implement an SBOM process.
- Harden SMB and WinRM: Disable WinRM on any host where it is not operationally required. Enforce SMB signing and implement segmentation rules blocking east-west SMB and WinRM traffic.
- Implement Safe Mode and Boot Configuration Monitoring: Configure SIEM alerting on bcdedit command execution and modifications to SafeBoot registry keys. These are known precursors to Vect ransomware execution.
- Harden ESXi and Hypervisor Management Planes: Segment ESXi management networks from general enterprise traffic. Restrict hypervisor administrative access to dedicated jump hosts with phishing-resistant MFA. Vect explicitly targets VMware infrastructure.
- Tune EDR for Ransomware Precursor Behavior: Alert on rapid intermittent file encryption, mass file renaming, abnormal termination of security and backup services, and unauthorized Safe Mode boot modifications. Enable tamper protection and enforce application allowlisting where feasible.
- Block TOR Egress Traffic: Implement perimeter controls blocking outbound connections to TOR entry nodes and onion DNS resolution. Vect’s entire C2 and negotiation infrastructure operates exclusively over TOR.
- Monitor Vect Leak Site for Organizational Exposure: Establish monitoring for new victim disclosures on Vect’s data archive. Early identification of a listing provides a critical window to initiate incident response before full data publication.
Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report