Key Takeaways
- Bitwarden’s CLI npm package was compromised on April 22, 2026, between 17:57 and 19:30 ET via a poisoned GitHub Actions workflow tied to the ongoing Checkmarx supply chain campaign—exposing approximately 250,000 monthly downloaders to a credential-stealing payload for a 90-minute window.
- The malicious payload, self-identified as “Shai-Hulud: The Third Coming,” is the third iteration of a self-propagating npm worm active since September 2025, now directly linked to financially motivated threat actor TeamPCP. End-user password vaults were not affected.
- This incident is not an isolated breach of a password manager—it represents targeted infiltration of developer infrastructure. Bitwarden did not have a vulnerability in its own codebase; attackers exploited the trust it placed in a compromised third-party GitHub Action. The trust chain became the attack surface.
- TeamPCP demonstrates a deliberate targeting preference for security tools—Trivy, Checkmarx KICS, and now Bitwarden—which are explicitly authorized to read secrets and access cloud APIs with elevated trust, providing a quality of initial access that perimeter exploitation rarely achieves.
- The self-propagating worm component and GitHub-based exfiltration channel mean the blast radius of this incident continues to expand after the initial package was removed. Stolen npm tokens can be used to publish infected versions of other packages maintained by victim developers, and exfiltrated data committed to public GitHub repositories under victim accounts cannot be recovered without the attacker’s private key.
- A confirmed operational relationship between TeamPCP and the Vect ransomware-as-a-service (RaaS) operation means this campaign should be treated as a ransomware precursor. The goal is not credential theft itself—it is downstream monetization via ransomware deployment. Organizations with confirmed exposure should initiate ransomware-level incident response protocols immediately.
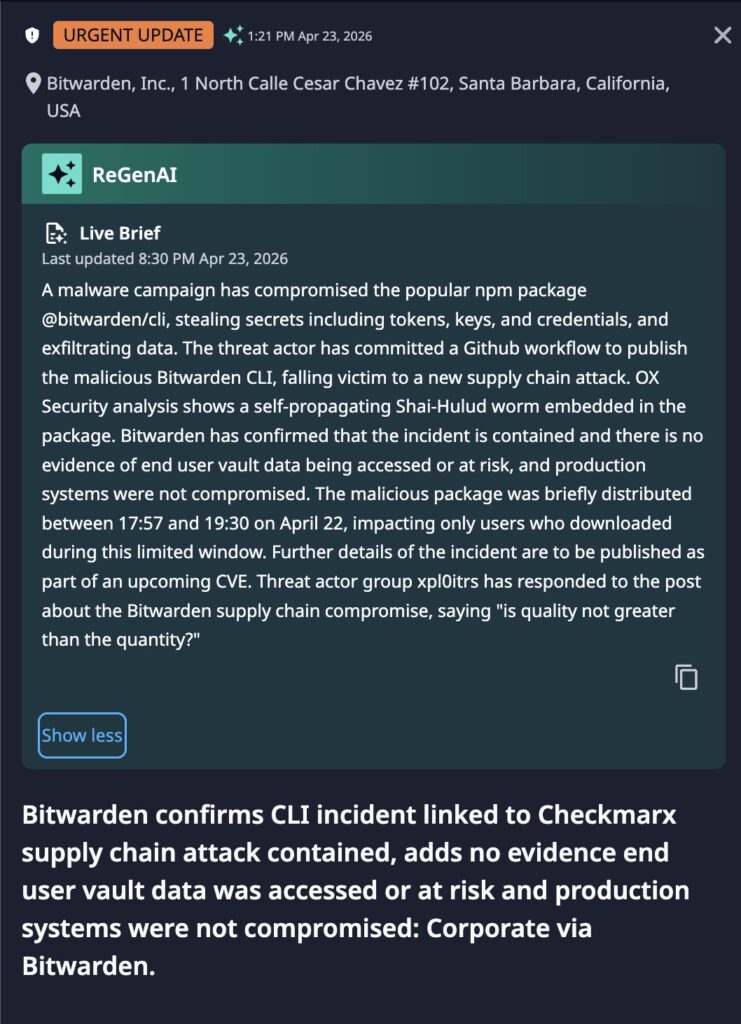
Incident Overview
On April 22, 2026, threat actors published a malicious version of the Bitwarden CLI—@bitwarden/[email protected]—to the npm registry. The package was available for approximately 90 minutes before being identified and deprecated. During that window, any developer or automated CI/CD system that installed the package without a pinned version hash was exposed to a credential-stealing worm carrying the internal signature “Shai-Hulud: The Third Coming.”
Bitwarden’s CLI is deeply embedded in enterprise development infrastructure: teams wire it into CI/CD pipelines to inject secrets at build and deploy time, pull API keys into automation frameworks, and integrate it with shared vaults. This is operational developer plumbing—compromising it provided adversaries with a foothold inside enterprise build environments rather than merely access to a consumer credential store. At enterprise scale, the dependency graph of trusted tools, actions, plugins, and packages that CI/CD pipelines consume is rarely fully known or continuously monitored. This incident demonstrates precisely how that gap is exploited: Bitwarden’s own code was clean, but a trusted third-party GitHub Action in its pipeline had already been compromised.
Bitwarden confirmed the incident stemmed from the compromise of checkmarx/ast-github-action, used in Bitwarden’s CI/CD pipeline. Attackers abused GitHub’s fork object store and OIDC-based trusted publishing to route a malicious tarball through Bitwarden’s release infrastructure without leaving a standard branch history trail. The consistent use of GitHub repositories as exfiltration destinations—a technique present across all three Shai-Hulud campaign iterations—reflects a deliberate evasion strategy: traffic to github.com is typically whitelisted by enterprise network controls, blends into legitimate developer API call volumes, and cannot be traced to an attacker-controlled domain. The shift to asymmetric encryption in this third iteration means that even if exfiltrated data in public repositories is discovered, only the attacker can decode it.
Dataminr Detection
Technical Details: Malware Behavior
The malicious package modified npm’s scripts.preinstall and the bin.bw entry point, redirecting both to a custom loader named bw_setup.js. No user interaction was required—executing npm install @bitwarden/cli triggered the malicious code path. The outer package metadata claimed version 2026.4.0 while internal application metadata still referenced 2026.3.0, a telltale sign of a repackaged legitimate release rather than a clean source build.
Stage 1
Preinstall Loader (bw_setup.js) Executes automatically upon package installation. Detects the host operating system, retrieves Bun JavaScript runtime v1.3.13 from GitHub releases if not already present, and passes execution to the second stage. Use of a legitimate runtime binary allows the payload to blend with ordinary developer tooling activity, reducing likelihood of behavioral detection. Presence of a Bun binary in unexpected filesystem locations is an indicator of compromise.
Stage 2
Credential Harvester (bw1.js) A heavily obfuscated Bun bundle performing a broad sweep of credentials and secrets across the compromised host via three cloud credential collection modules (list_AWS_secrets(), list_GCP_secrets(), list_Azure_secrets()), a GitHub API weaponization module, an npm self-propagation module, and an embedded Python memory-scraping script targeting GitHub Actions Runner.Worker processes. Targeted material includes SSH keys; GitHub PATs and npm publish tokens; cloud provider credentials for AWS, GCP, and Azure including those stored in secret managers; .env files; shell command history; CI/CD runner secrets; and AI tooling configuration files. The payload injects a loader reference into ~/.bashrc and ~/.zshrc to maintain persistence across sessions and uses a lock file at /tmp/tmp.987654321.lock to prevent redundant execution.
Stage 3
Exfiltration and Lateral Spread Stolen data is encrypted using AES-256-GCM and exfiltrated via two channels. The primary channel posts encrypted telemetry to audit.checkmarx[.]cx/v1/telemetry—the same C2 endpoint used in the Checkmarx mcpAddon.js payload, confirming shared infrastructure. The secondary channel creates public GitHub repositories under the victim’s own account and commits encrypted stolen data using Dune-themed repository names, routing malicious exfiltration over legitimate GitHub API traffic and rendering it nearly invisible to perimeter network controls. Recovery of exfiltrated data without the attacker’s private key is not possible.
If GitHub tokens are recovered, the malware automatically weaponizes them by injecting malicious GitHub Actions workflow files into victim-accessible repositories, enabling persistent extraction of CI/CD secrets from downstream pipelines long after the compromised package is removed. The self-propagation module uses stolen npm tokens to publish malicious updates to other packages maintained by the victim, extending reach across the npm ecosystem independent of further attacker interaction.
TeamPCP has progressively moved from opportunistic cryptomining and credential harvesting to a focused, high-tempo supply chain compromise model targeting developer tooling embedded in enterprise CI/CD pipelines. The group demonstrates a deliberate targeting preference for security tools which occupy privileged positions in developer environments and are explicitly authorized to read secrets and access cloud APIs. A confirmed operational partnership with the Vect RaaS operation means that credentials harvested from enterprise CI/CD environments are being converted into ransomware deployment events. Locale-aware payload suppression on Russian-locale hosts provides the primary basis for Russian-nexus attribution.
Immediate Actions & Recommendations
- Identify exposure immediately. Audit all systems, CI/CD pipelines, and Dockerfiles for any installation of @bitwarden/[email protected]. Check npm lock files, Docker layer history, and CI run logs for the window between 17:57 and 19:30 ET on April 22, 2026. Even brief or failed installations may have triggered the malicious preinstall hook.
- Rotate all potentially exposed credentials. Treat any exposed system as a confirmed compromise. Rotate GitHub PATs, npm publish tokens, AWS access keys and IAM credentials, GCP service account keys, Azure secrets, SSH keys, and all CI/CD environment secrets available to affected build environments—including secrets present as environment variables, in .env files, in .npmrc files, and in shell history.
- Audit GitHub repositories for malicious artifacts. Search GitHub organizations for unauthorized public repositories with Dune-themed names per the IOC table. Review all repository webhook configurations, GitHub Apps, and OAuth applications for unauthorized additions. Scan .github/workflows/ directories for unexpected or modified workflow files added after April 22, 2026.
- Remove malicious files and runtime artifacts. On affected systems, remove bw1.js, bw_setup.js, and any Bun runtime binaries from npm package installation directories. Clear the npm cache. Upgrade to @bitwarden/[email protected] or later. Confirm absence of /tmp/tmp.987654321.lock and remove if present.
- Pin and hash-validate all CI/CD dependencies. Implement dependency pinning with cryptographic hash validation for all npm packages, GitHub Actions, and Docker images used in CI/CD pipelines. Do not rely on version ranges or unpinned latest tags in build environments.
- Review all third-party GitHub Actions in use. Any workflow using checkmarx/ast-github-action, checkmarx/kics-github-action, or any Checkmarx-published action should be treated as potentially compromised and reviewed against Checkmarx’s April 22 advisory. Pin all third-party actions to specific commit SHAs.
- Monitor for downstream package propagation. If any npm tokens were exposed, monitor the npm registry for unauthorized package versions published under affected maintainer accounts and notify downstream consumers accordingly.
- Treat this as a ransomware precursor. Given the documented TeamPCP–Vect RaaS relationship, organizations with confirmed exposure should initiate ransomware-level incident response protocols in parallel with credential rotation—including network segmentation, backup integrity review, and engagement with legal and insurance stakeholders.
- Block C2 infrastructure. Implement firewall rules blocking outbound connections to audit.checkmarx[.]cx and review historical egress logs for prior connections. Note that GitHub-based exfiltration cannot be blocked via domain and must be addressed through GitHub API audit logging and token scope restriction.
- Enforce phishing-resistant MFA on developer accounts. Mandate WebAuthn/FIDO2 MFA on all GitHub and npm accounts with package publishing permissions. TOTP-based MFA is insufficient—session token harvesting within the payload can bypass TOTP. Require MFA for all write and publishing actions at the organization and package level.
MITRE ATT&CK Mapping
Technique ID – Description
T1195.001 – Compromise software supply chain
T1059.007 – JavaScript execution
T1552.001 – Credentials in files
T1552.004 – Private key theft
T1567.001 – Exfiltration to code repository
T1546 – Shell profile persistence
T1534 – Token-based lateral movement
T1078 – Valid accounts – OIDC abuse
Indicators of Compromise
Type – Indicator – Notes
Package – @bitwarden/[email protected] – Sole affected npm release; deprecated
File – bw1.js – Primary payload; obfuscated Bun bundle
File – bw_setup.js – Loader stage; bootstraps Bun runtime
C2 Domain – audit.checkmarx[.]cx/v1/telemetry – Primary exfil endpoint; shared with Checkmarx mcpAddon.js payload
IP – 94.154.172[.]43 – Attacker-controlled infrastructure
Lock File – /tmp/tmp.987654321.lock – Presence confirms active or prior infection
Persistence – ~/.bashrc, ~/.zshrc – Inspect for injected loader references
Runtime – Bun v1.3.13 – Downloaded from GitHub releases; presence in unexpected locations
String – Shai-Hulud: The Third Coming – Embedded campaign identifier
String – LongLiveTheResistanceAgainstMachines – Embedded ideological manifesto string
String – beautifulcastle – Additional identifier confirmed by JFrog analysis
Obfuscation – __decodeScrambled, seed 0x03039 – Shared routine confirming link to Checkmarx campaign infrastructure
GitHub Repos – Dune-themed names – atreides cogitor fedaykin fremen futar gesserit ghola harkonnen heighliner kanly kralizec melange sandworm sardaukar sietch stillsuit
Workflow – 47c6f59083 → 03df1ecd86 – Malicious publish-cli.yml commit chain in fork network

2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report