The domain of intelligence is fundamentally one of decision support. Stakeholders and decision-makers face uncertainty across many instances, and intelligence as both discipline and product works to reduce—although not necessarily eliminate—such uncertainty to allow for better outcomes. This process can be viewed as one of refinement, from raw data collected for further processing eventually yielding a finalized, researched intelligence product, as displayed in the following diagram.
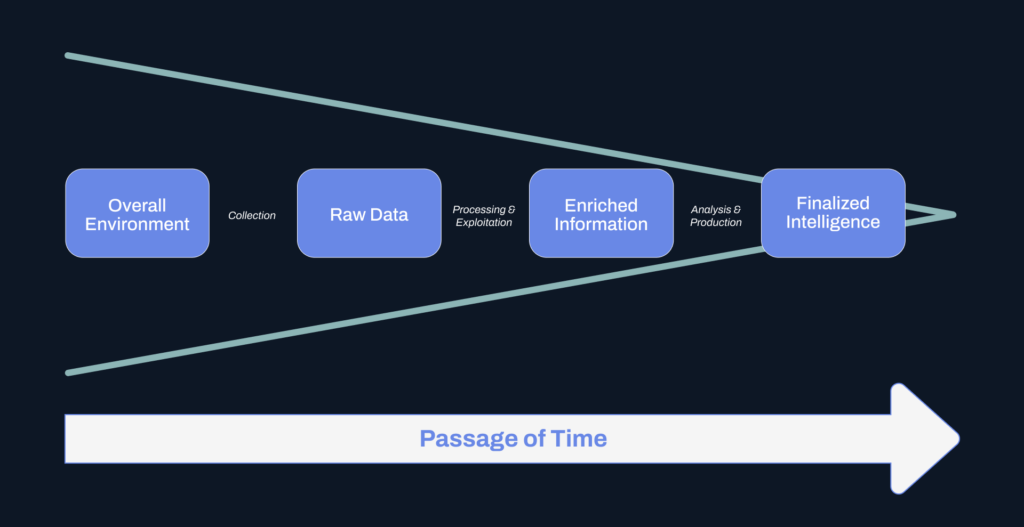
This process of continual refinement represents a “best case” scenario where analysts—”humans in the loop”—can work through collected data, enrich and enhance it, then orient that information with respect to the broader intelligence picture. The goal in this process is to enrich understanding and available data in a fashion that aligns with the needs and purposes of the audience, a decision-maker. Yet such a process comes with costs, not the least of which being whether a stakeholder actually requires this level of enrichment and enhancement, or if the stakeholder can wait for such a detailed process to play out over time.
Intelligence & Orienting to Applications
If intelligence, and by extension cyber threat intelligence (CTI), is a discipline linked to supporting decisions, then such research and analysis should be grounded on the decision-maker. Yet, much intelligence takes place within a vacuum compared to specific stakeholder support, and understanding of the precise decisions in play. This is especially the case in CTI, where stakeholders range from the CISO to the SOC analyst, and decisions range from long-term attack surface management to binary adjudication of newly-observed network infrastructure.
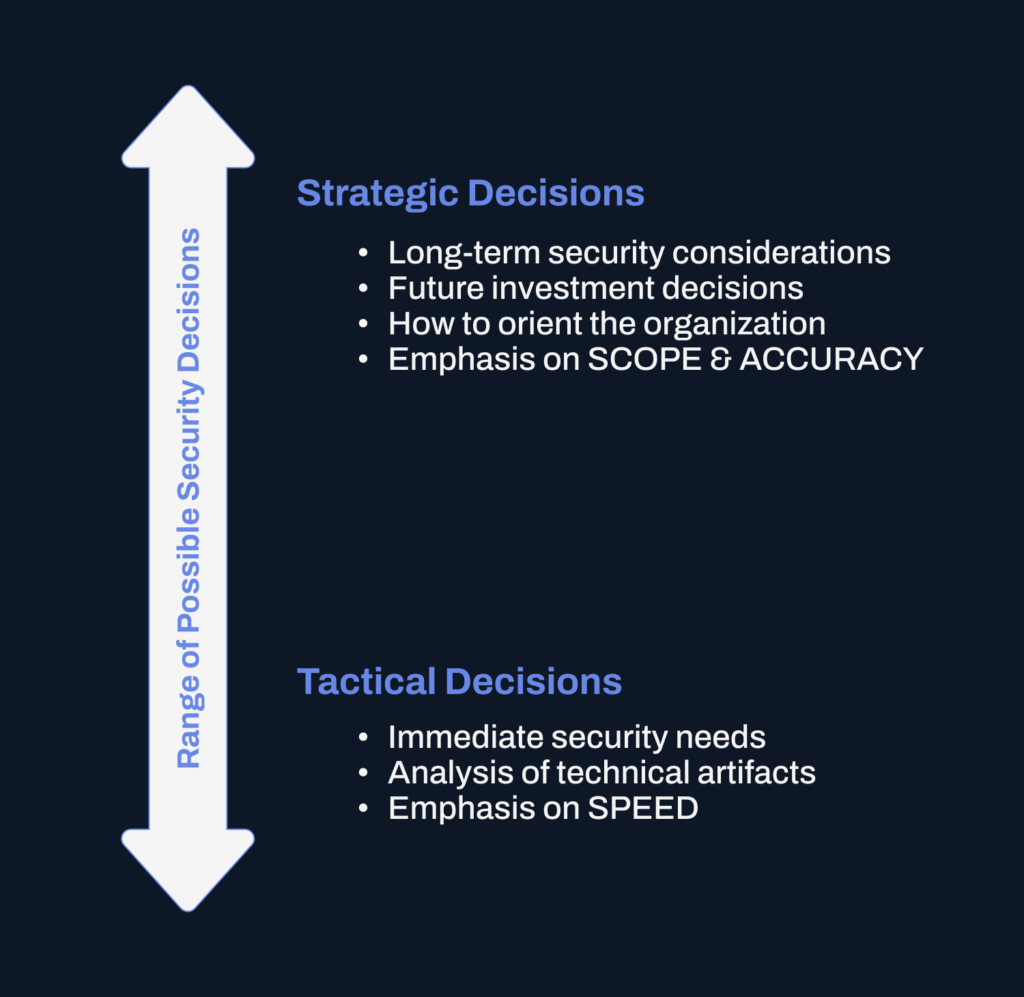
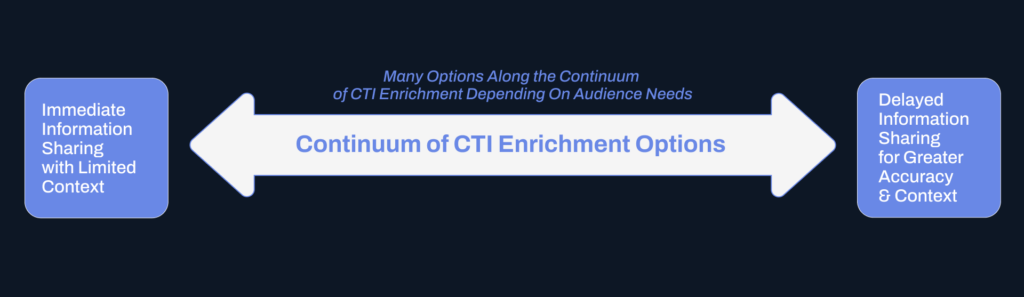
Despite the myriad circumstances within network defense, CTI often takes the guise of a “one size fits most” arrangement of delivering a long-form writeup accompanied by technical indicators, or a feed of “indicators of compromise” for more (perceived) rapid action in a machine-to-machine setup. These products certainly yield value, but do so along certain extremes: formal, written intelligence products are (ideally) detailed and contain significant context, yet at the cost of significant investment in time for their production. On the other hand, indicator sharing takes place in rapid fashion but often lacks context for proper use and application.
These two considerations—time and context—are vital in delivering CTI (or any intelligence) that is actionable. By actionable, we mean intelligence that:
- Allows for a recipient to take a definite action from the information provided.
- Contains enough context so that a decision-maker is relatively aware of the overall environment in which the decision or action is taken.
- Arrives in time for the decision to matter with respect to the given threat, actor, or situation at hand.
These criteria immediately establish a dilemma: satisfying these items requires work, and work takes place through the investment of effort over time. In the process of making intelligence outputs more actionable, we thus sacrifice or limit its efficacy in terms of timeliness. We thus see an implicit choice: does an intelligence audience favor timeliness of alerting and reporting, or context and depth?
These criteria are obviously different depending on the audience: a SOC analyst likely prefers timely information on emerging threats to more quickly respond to them, while a CISO demands greater context and more information to allow for more accurate, longer-term impacting decision-making. Yet the impact of time—or its passage—on CTI reporting remains a critical issue in evaluating the use and efficacy of alerting.
Navigating Trade-Offs in Intelligence Delivery
Security decision-makers, as well as CTI analysts, must therefore understand the nature and inherent conflicts within analysis and reporting. Identifying organizational needs and the purpose for which CTI is produced or ingested is vital to appropriately organizing workflows, procedures, and expectations. As such, tradeoffs are not only present but they remain inevitable. An organization prioritizing enrichment and accuracy of information will by necessity give up a degree of information timeliness, while entities requiring immediate security alerting will do so by sacrificing some degree of accuracy or contextuality.
Determining where the organization resides along this continuum is a necessary step in developing and aligning a CTI-enhanced security program with needs and capabilities. Critically, expecting a single solution to satisfy all of these needs simultaneously is likely impossible in most instances if for no other reason than the progress of time. As such, sacrifices are demanded, and clarity in purpose and outcome necessary, in building an intelligence-driven decision-making process.
For tactical decision-making within the information security space, time becomes of particular importance. Real-time alerting and response to threats demands that information, even if imperfect, arrive in time for it to be effective in immediate decision-making. Accelerating the movement from raw data collection to an actionable product suitable for security actions is not merely desirable, but necessary in improving outcomes in a contested information environment. Human-driven processes remain the gold standard for much of long-form CTI reporting and analysis, but the work factor in production and the concurrent cost in time means analysis may arrive too late. Understanding how or why a breach took place is certainly useful and informative, but remains a distant second to preventing that breach (if not in its entirety, then at least in its ability to achieve actions of objective).
Determining mechanisms to arrive at “good enough” information sooner, rather than “perfect” information later, thus becomes an acute need for modern security operations. Understanding the applications of this information and what processes are guided by such actions is crucial in aligning inputs with outcomes, and ensuring that the right audiences receive the support necessary to reduce uncertainty in dispositioning items of security concern.
Future Opportunities & Applications of Technology
The above observations appear to set hard limits on the actionability and timeliness of intelligence. Yet, technological progress and advancement open up opportunities to both have our cake—and eat it too. Particularly, rapid advancements in artificial intelligence (AI) open up possibilities for significant machine augmentation of what were traditionally human-dependent processes of enrichment and analysis. AI can accelerate enrichment of technical indicators and rapidly deliver assessments of intrusions—given appropriate guidance, prompt development, and workflows. Essentially, AI supplements CTI workflows to significantly increase the amount of information and detail that can be provided in operational timescales.
Leveraging technology is not a new element within intelligence analysis, as manual processes moved to computer-assisted analysis and correlation over time. Yet, the application of AI to human-driven workflows may enable increases in speed that are orders of magnitude greater than past applications. Through rigorous development of enrichment and analysis workflows, analysts may be able to develop a process through which autonomous agents then perform enrichment, correlation, and preliminary assessment to deliver contextualized results in minutes—or even seconds—of event recognition.
Concerns around accuracy, completeness, and potential AI-driven hallucinations are still valid and argue for continued human checks and, where necessary, intervention. Yet, to build rapid workflows that allow frontline decision-makers to quickly act on intelligence perspectives, some degree of error acceptance is necessary to obtain the benefit of greater speed.
Precisely which tradeoffs are necessary and where an organization resides along a continuum of possible options will be dependent upon the timeliness of the workflow, the criticality of decisions, and the implications of a potential error. The time is rapidly approaching where integration of AI and related technologies into intelligence workflows is not simply a new or novel technological effort, but rather a necessary step in building a minimally-effective intelligence program capable of supporting operational timelines.

2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. Read our report to gain the context and foresight needed to anticipate and prioritize threats, protect critical assets, and act decisively in high-stakes moments
Download Report