Key Takeaways
- Account Compromise: A threat actor is offering verified United States police department emails accounts for $1,000 USD per account as well as direct access to Kodex Global for $2000 USD.
- Kodex Global Integration: The listings explicitly include access to the Kodex Global portal, a critical tool used by law enforcement to submit subpoenas and Emergency Data Requests (EDRs) to major companies.
- High Risk of Fraud and Phishing: Unauthorized access enables threat actors to create communications that look legitimate and submit formal data requests, potentially bypassing standard security verification protocols.
Incident Overview
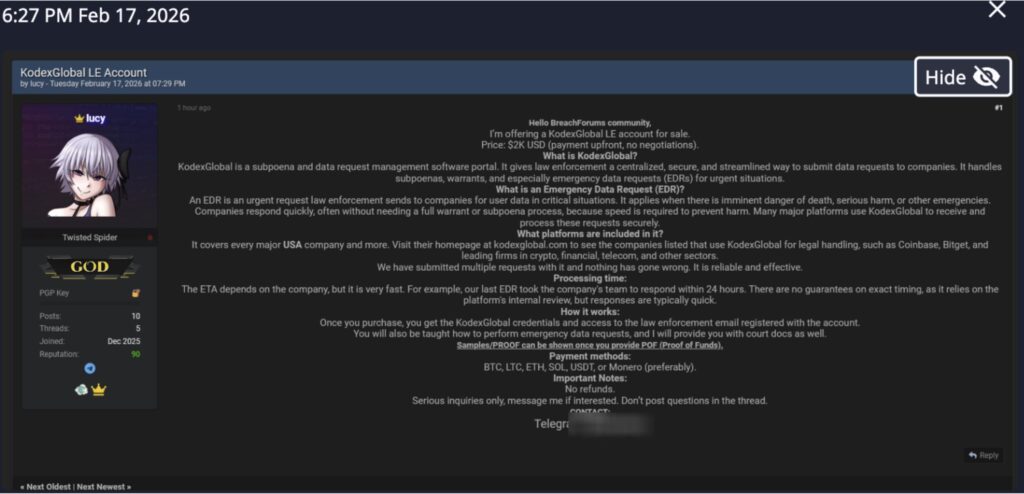
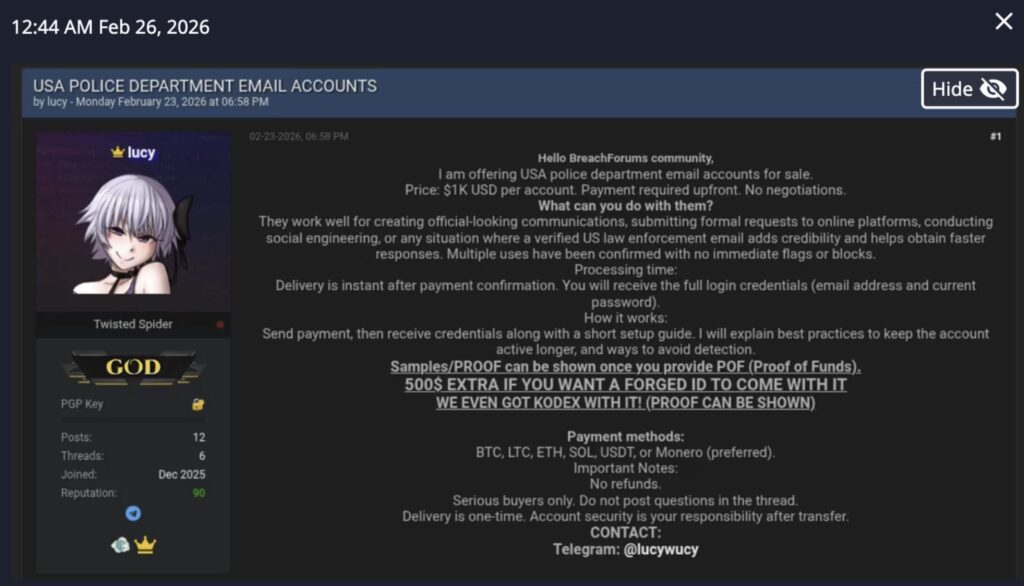
On February 17, 2026, Dataminr identified the initial public post regarding the sale of a standalone Kodex Global law enforcement account for $2,000. Nine days later, Dataminr detected an updated illicit forum advertisement by the same threat actor offering verified USA police department email accounts.
Kodex Global is a portal used by both law enforcement and corporations to manage subpoenas, warrants, and emergency data requests (EDRs). The platform possesses massive amounts of personal, transactional, and technical data about the subjects of its legal data requests.
The actor, “lucy,” claims these accounts are highly effective for conducting social engineering and obtaining fast responses from online platforms. Most concerningly, the sale can be bundled with forged law enforcement identification and access to the Kodex Global law enforcement portal for an additional fee.
Dataminr Detection
This incident, while specific to Kodex Global, exemplifies why real-time monitoring of illicit listings provides organizations critical warning to audit incoming requests and implement secondary verification for all legal data inquiries. While not tied to this incident, in 2021, both Apple and Meta responded to fake Emergency Data Requests (EDRs) and supplied basic subscriber details such as address, phone number, email address and IP address. In 2024, the FBI issued a Private Industry Notification (PIN) noting an uptick in this activity, which has continued to be an issue since then. Normally a subpoena or search warrant signed by a judge is required to obtain this information but since EDRs are for emergency situations that might not be able to wait for a judge’s sign-off, they do not require a court order.
Threat Actor Details
The seller, “lucy,” who holds a “GOD” rank and “Twisted Spider” (not related to the threat group Twisted Spider) designation on the forum, provides the following details:
- Deliverables: Full login credentials including email address and current password, delivered instantly upon payment confirmation.
- Additional Services: Forged law enforcement identification can be provided for an additional $500.
- Operational Guidance: The seller includes a setup guide with best practices to maintain account longevity and avoid detection by the targeted platforms.
- Payment Methods: BTC, LTC, ETH, SOL, USDT, or Monero (preferred).
The actor’s primary motivation is financial gain, utilizing established forum reputation to broker high-value access. By providing the means to impersonate law enforcement, they facilitate downstream crimes such as unauthorized data exfiltration and targeted harassment via fraudulent Emergency Data Requests.
Dataminr’s Recommendations
Organizations receiving legal requests via Kodex Global or law enforcement emails should implement the following:
- Enhanced Emergency Data Request (EDR) Verification: Establish a mandatory out-of-band (OOB) verification process for all EDRs. Confirm the requester’s identity by calling the official, publicly listed telephone number for the relevant police department.
- Scrutinize Documentation: Train compliance teams to identify markers of forged law enforcement identification or templated legal documents.
- Audit Active Portal Access: Coordinate with Kodex Global to review active agency accounts for anomalous behavior, such as logins from unexpected IP ranges or unusual volumes of requests.
- Monitor for IAB Activity: Continue to monitor illicit forums for advertisements targeting specific law enforcement domains or agency infrastructure.
For extended information and mitigation suggestions, review the FBI’s notification regarding fraudulent emergency data requests here.

Stay Ahead of Emerging Threats
Learn more about how Dataminr helps cybersecurity customers get ahead of emerging threats.
Learn More