Key Takeaways
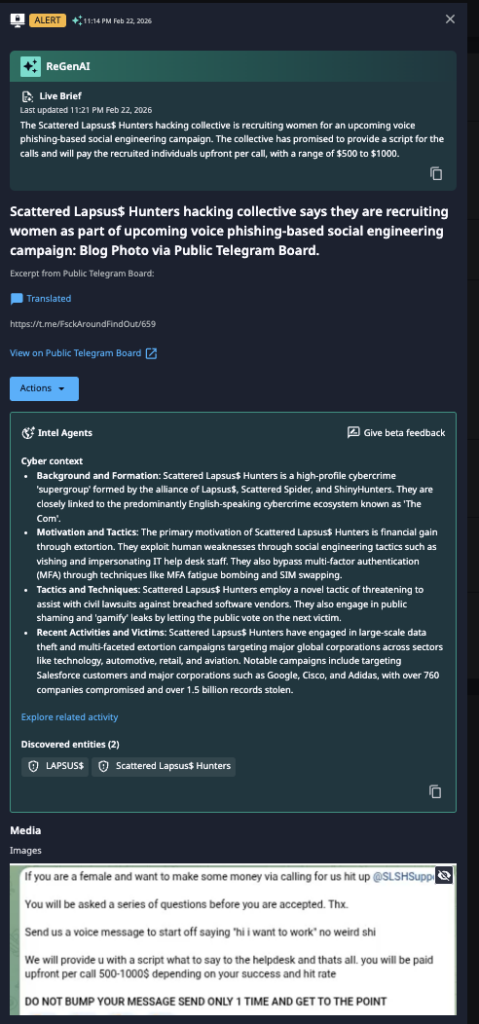
- Tactical Evolution: SLH is diversifying its social engineering pool by specifically recruiting women to conduct vishing attacks, likely to increase the success rate of help desk impersonation.
- High Incentives: The group is offering significant financial incentives ($500–$1,000 upfront per call) and providing pre-written scripts to recruits.
- High-Profile Risk: SLH is a “supergroup” alliance of Lapsus$, Scattered Spider, and ShinyHunters, known for compromising major global corporations and stealing over 1.5 billion records.
Overview of the Discovery
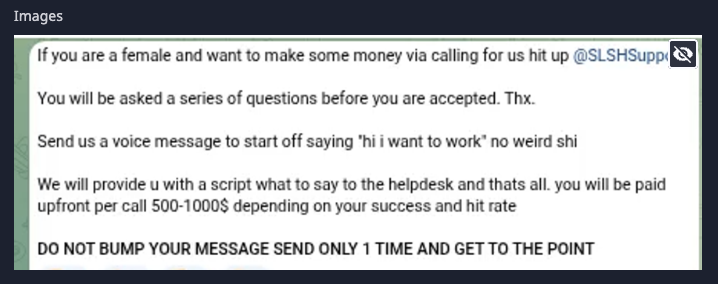
On February 22, 2026, Dataminr detected activity on a public Telegram board indicating that the Scattered Lapsus$ Hunters (SLH) hacking collective is recruiting women for an upcoming vishing-based social engineering campaign. The group is offering to pay recruited individuals $500 to $1,000 upfront per call and promises to provide the necessary scripts for the operation.
This recruitment drive represents a calculated evolution in SLH’s tactics. By specifically seeking female voices, the group likely aims to bypass the “traditional” profiles of attackers that IT help desk staff may be trained to identify, thereby increasing the effectiveness of their impersonation efforts.
SLH was recently highlighted in our 2026 Cyber Threat Landscape Report as one of the most active cybercrime groups last year. Beyond continuing to compromise organizations in 2026, this evolution in tactics indicates that the group has no intention of slowing down.
Dataminr Detection
Dataminr’s Recommendations
SLH is a high-profile cybercrime “supergroup” formed by an alliance between Lapsus$, Scattered Spider, and ShinyHunters. Their primary motivation is financial gain through extortion. They are notorious for bypassing multi-factor authentication (MFA) through techniques like MFA fatigue bombing and SIM swapping, and they frequently target help desk staff to gain initial access. Past victims include major corporations such as Google, Cisco, Adidas, and Salesforce customers.
Organizations should adopt a heightened defensive posture against social engineering:
- Help Desk Training: Immediately brief IT help desk and support personnel on this specific recruitment trend. Emphasize that attackers may use pre-written scripts and polished voice impersonation.
- Strict Identity Verification: Enforce out-of-band identity verification (e.g., video calls or secondary internal verification) for all password resets or MFA credential changes requested via phone.
- Harden MFA Policies: Move away from SMS or push-based MFA, which are vulnerable to SLH’s known TTPs like SIM swapping and fatigue bombing. Implement FIDO2-compliant hardware security keys where possible.
- Monitor Anomalous Access: Audit logs for new user creation or administrative privilege escalation immediately following help desk interactions.

Stay Ahead of Emerging Threat Actor Activity
Learn more about how Dataminr helps cybersecurity customers get ahead of emerging threats.
Learn More