Key Takeaways
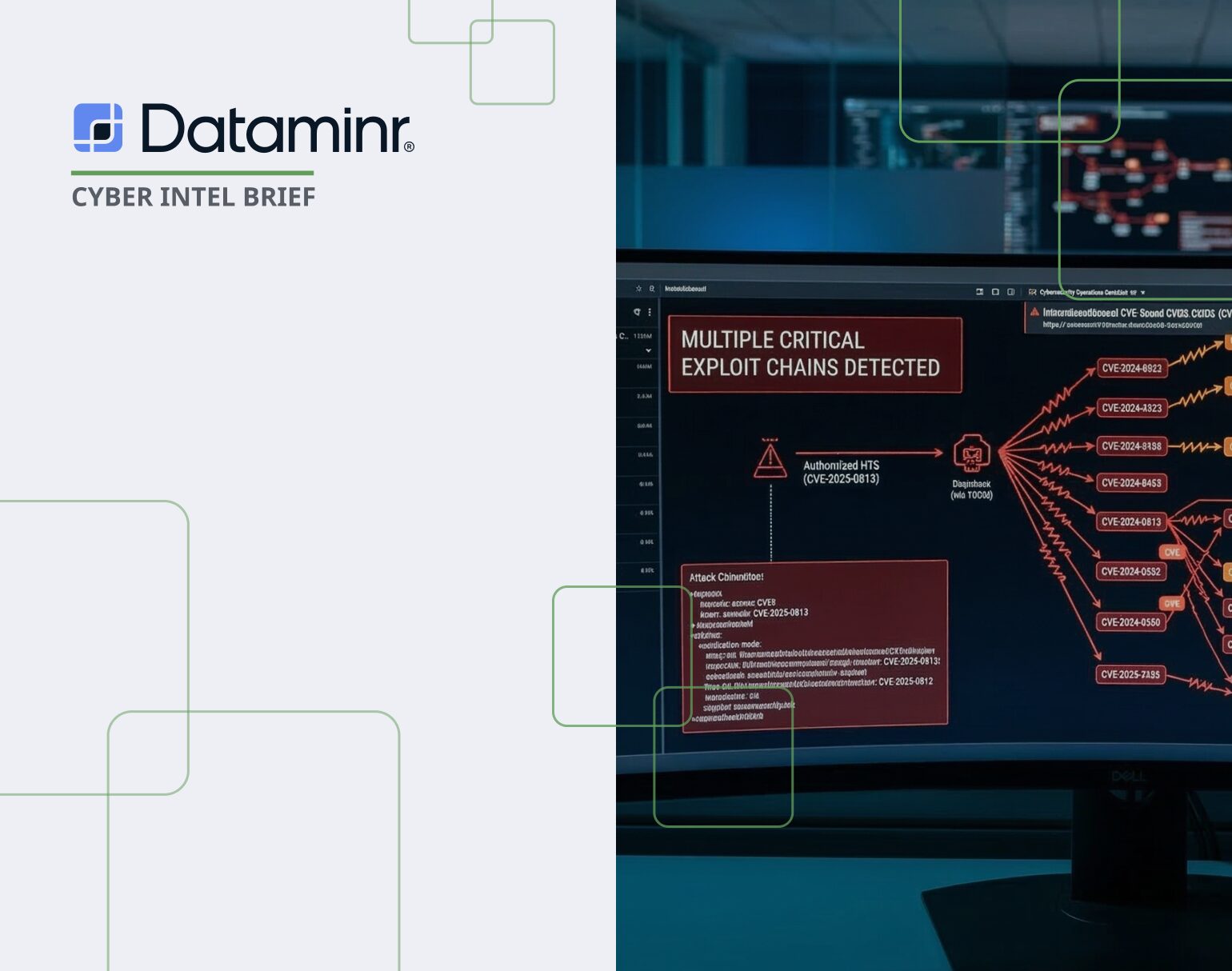
- Critical Vulnerability Chain: The “Ni8mare” threat involves the technical chaining of CVE-2026-21858 (unauthenticated file read) and CVE-2025-68613 (authenticated RCE).
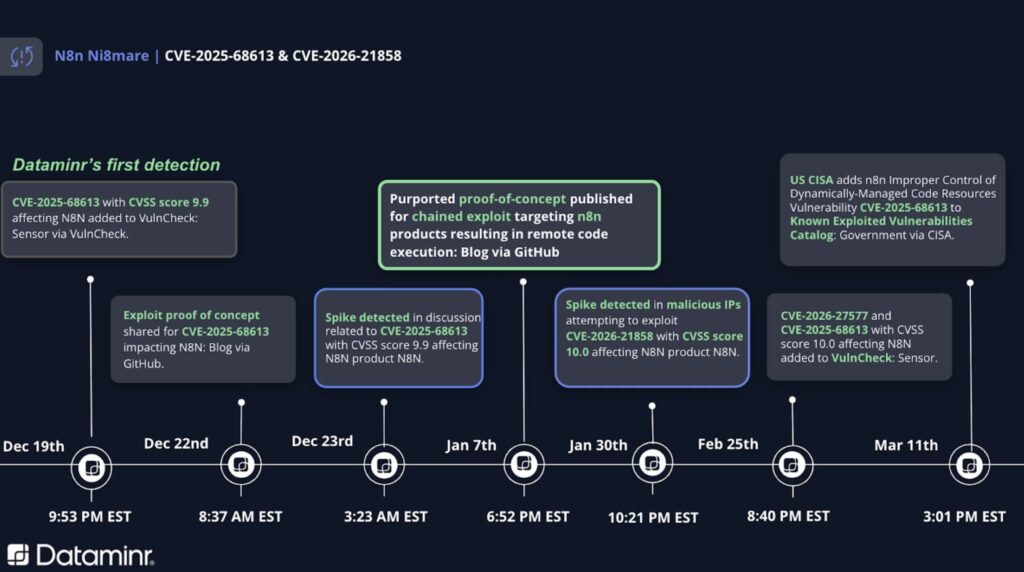
- Dataminr Early Detection: Dataminr provided a critical 82-day lead time on CVE-2025-68613 and alerted on the chained exploit POC on January 7, enabling proactive infrastructure hardening months before the official CISA KEV notification
- Total Compromise: By chaining these flaws, attackers bypass authentication barriers to achieve full Remote Code Execution (RCE) and system takeover.
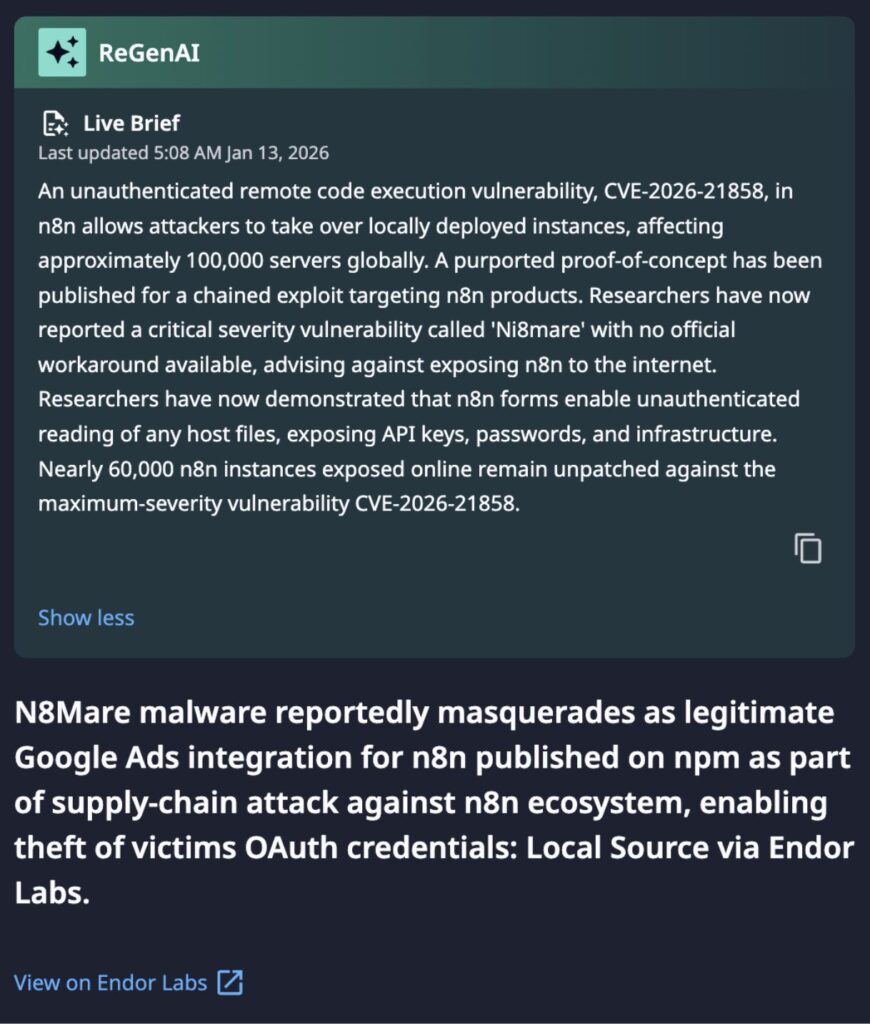
- Supply Chain Attack: Malicious npm packages (e.g., masquerading as “Google Ads” nodes) are actively targeting the n8n ecosystem to exfiltrate OAuth credentials and API keys.
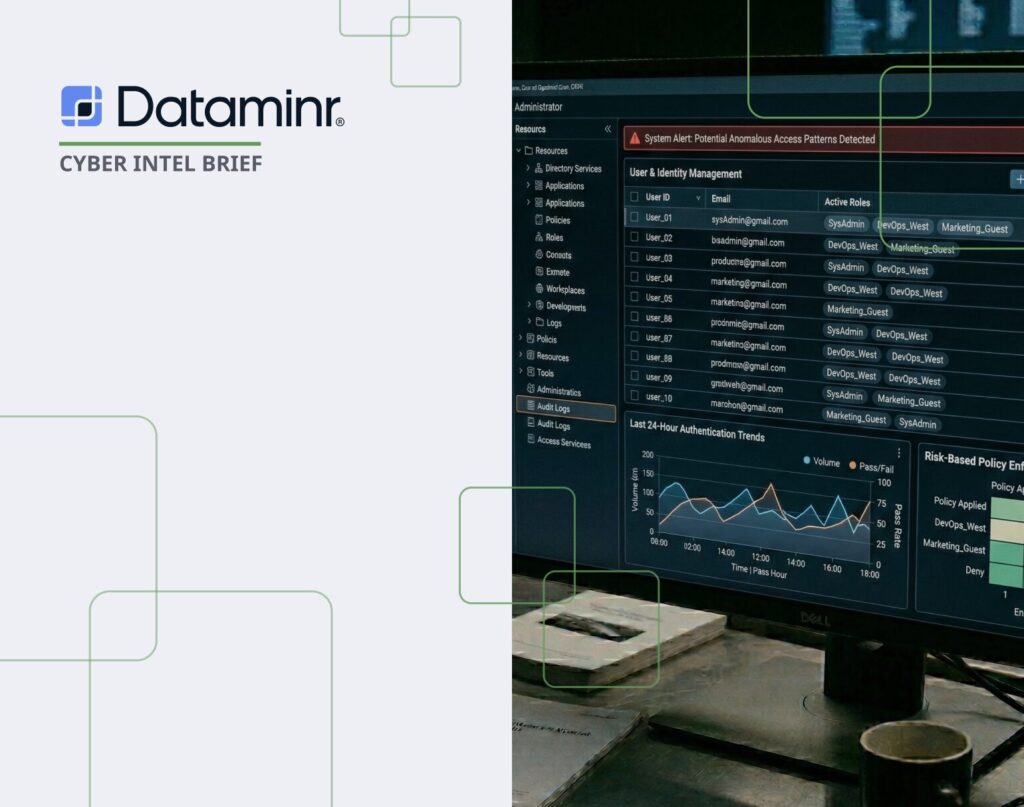
- Centralized Risk: Because n8n acts as a “credential vault” for connected SaaS platforms (Salesforce, Stripe, etc.), a single compromise grants access to an organization’s entire digital ecosystem.
- Mandatory Action: US CISA added CVE-2025-68613 to the Known Exploited Vulnerabilities (KEV) catalog on March 11, 2026. Immediate patching to v1.121.0 or later is required for US Federal Government organizations.
Incident Overview
The Ni8mare incident represents a multi-vector attack against the n8n automation platform. It encompasses both a critical software vulnerability chain and a coordinated supply chain campaign via the npm registry. Initially detected in late 2025, it targets n8n’s role as a centralized hub for enterprise integrations.
n8n is a self-hostable, low-code automation platform that allows organizations to orchestrate APIs, transform data, and manage AI agents across a wide range of enterprise applications. It is preferred by security-conscious organizations and large technical teams—including telecommunications, banking and various government entities—due to its ability to maintain data sovereignty on private infrastructure.
Dataminr Vulnerability Risk Assessment
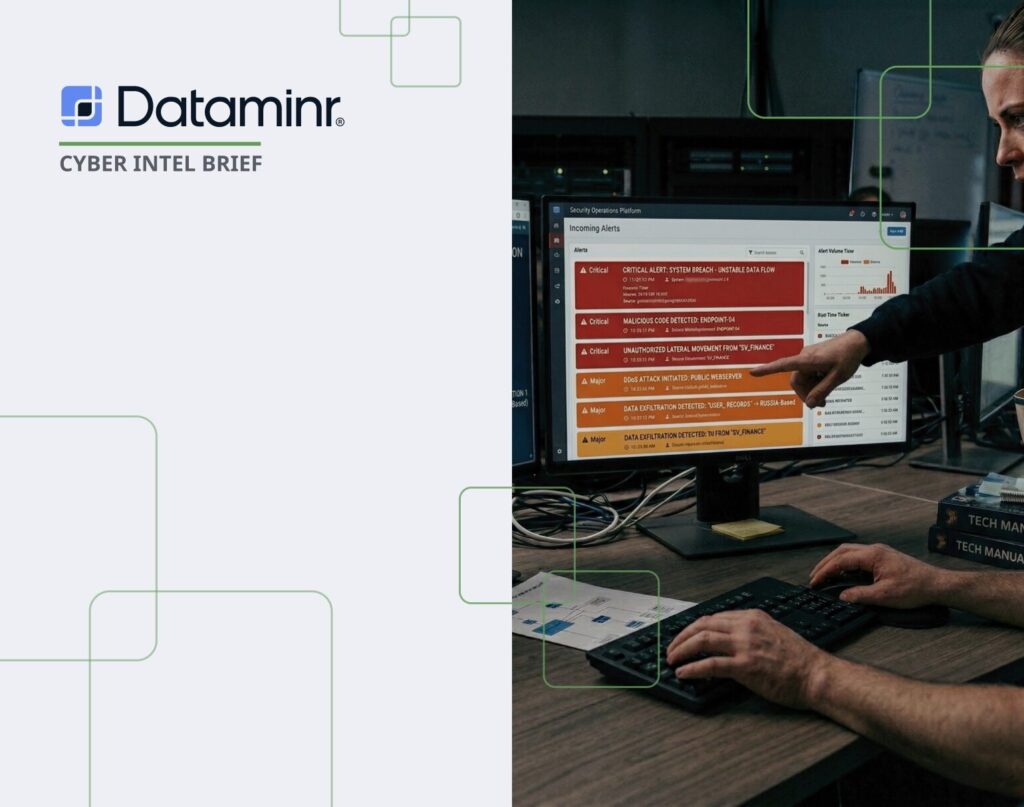
Early alerts for CVE-2025-68613 in n8n appeared in December 2025, with a public proof-of-concept exploit published in early January—well before the vulnerability was later added to the CISA KEV catalog. Because n8n automation servers often access critical systems, orchestrate automation workflows, and store sensitive data and credentials, these early signals should have prompted preemptive risk analysis and mitigation, rather than waiting for KEV confirmation.
Organizations that segmented or restricted n8n infrastructure during this early warning window could have materially reduced the likelihood of exploitation and the potential financial impact— which in severe compromise scenarios could exceed $100M once attackers operationalized the exploit according to Dataminr Risk Quantifier.
The availability of a public exploit chain significantly increases both the likelihood of successful exploitation and the potential financial impact. According to Risk Quantifier, this increase could be up to 3x compared to evaluating the vulnerabilities independently.
Dataminr Detection
Dataminr’s early-warning capabilities provided a decisive strategic advantage during the Ni8mare campaign, offering a critical 82-day lead time for CVE-2025-68613. While CISA did not officially mandate federal action via the KEV catalog until March 11, 2026, Dataminr clients received initial alerts as early as December 19, 2025. This window allowed organizations to conduct preemptive risk analysis and infrastructure segmentation nearly three months before government confirmation.
The value of this speed was exponentially magnified by the detection of a public exploit chain proof-of-concept (POC) on January 7, 2026. By alerting on the technical chaining of the unauthenticated file read (CVE-2026-21858) and the gated RCE (CVE-2025-68613), Dataminr provided the necessary context for users to recognize a “chain multiplier” threat. This shift—from a limited file read to a zero-click, unauthenticated system takeover—informed security teams of the potential for a total compromise of their centralized credential vaults.
Dataminr detected a spike in malicious IP scanning for CVE-2026-21858 in real-time on January 30, 2026. This preceded the official peak of the campaign, enabling proactive blocking of high-threat actors before lateral movement could be operationalized.
Technical Details & Chained Exploitation Timeline
The Ni8mare exploit path demonstrates how two vulnerabilities, which carry specific prerequisites when viewed in isolation, become exponentially more dangerous when combined.
Individually, CVE-2025-68613 is “gated” by authentication, and CVE-2026-21858 is “limited” to data theft. Chained together, the Ni8mare exploit collapses these trust boundaries. It transforms a post-authentication flaw into a zero-click, unauthenticated RCE, effectively removing the primary defensive layer (authentication) that organizations rely on for internal automation tools.
In addition to direct exploitation, the campaign utilizes malicious npm packages to target the n8n supply chain.
- The Connection: While the CVEs exploit the n8n platform, the malware targets the users and community nodes. Analysis by Endor Labs identifies that threat actors are publishing packages like n8n-nodes-hfgjf-irtuinvcm-lasdqewriit that masquerade as legitimate integrations (e.g., Google Ads).
- Execution Flow: Once a user installs the malicious node, it presents a legitimate-looking credential form. Because n8n lacks sandboxing between community nodes and the runtime, the malware intercepts decrypted OAuth tokens and API keys during workflow execution and exfiltrates them to an attacker-controlled server.
- Centralized Impact: This malware specifically weaponizes n8n’s role as a “centralized credential vault,” where a single malicious integration can compromise access to every third-party service connected to the instance.
While there is no current attribution to a threat actor(s) behind this,the primary motivation behind Ni8mare is credential harvesting and infrastructure access. By compromising n8n, attackers gain a persistent foothold in high-value environments and the ability to move laterally into connected SaaS platforms.
Immediate Actions & Recommendations
- Patch to v1.121.0 or Higher: This version addresses the root causes of the “Ni8mare” chain. (Note: Specific versions like 1.120.4 or 1.121.1 may be required depending on the environment).
- Audit npm Packages: Review package.json files and the ~/.n8n/nodes directory for suspicious community nodes or “Google Ads” integrations with random-string suffixes.
- Rotate All Credentials: If an instance was unpatched or a malicious node was identified, rotate all OAuth tokens, API keys, and service account passwords stored in n8n.
- Restrict Network Access: Ensure n8n is not exposed to the public internet. Implement a “Shields Up” posture by restricting access to verified VPN or ZTNA segments.
- Block Malicious IPs: The following IPs are also highlighted by a high CAL score, which provides a globally informed, baseline reputation score for indicators by analyzing aggregated and anonymized intelligence from across the broader security community.
185.177.72[.]52
- 22
- 123
- 4244
- 10250
- 960/1000 Critical
- Active
- Observations.High
YUFLY TELECOM SL
AS198697
185.177.72[.]30
- 22
- 123
- 10250
- 840/1000 Critical
- Active
- Observations.High
YUFLY TELECOM SL
AS198697
185.177.72[.]13
- 22
- 123
- 10256
- 840/1000 Critical
- Active
- Observations.Med
- Trending.Impressions
YUFLY TELECOM SL
AS198697
185.177.72[.]51
- 22
- 123
- 10250
- 620/1000 High
- Active
- Observations.Med
- Usage.DedicatedServer.Suspected
YUFLY TELECOM SL
AS198697
*More on CAL Global Threat Score: https://knowledge.threatconnect.com/docs/cal-global-threat-score
**More on CAL Indicator Status: https://knowledge.threatconnect.com/docs/indicator-status
***More on CAL Classifiers: https://knowledge.threatconnect.com/docs/cal-classifiers#cal-classifiers-glossary

Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Read Report