Key Takeaways
- The LexisNexis breach by FulcrumSec exploited the React2Shell vulnerability in an unpatched, over-privileged AWS app, leading to the alleged theft of critical data: government PII, internal security reports, customer plaintext passwords, and 98 supply chain credentials (hashes and AWS secrets).
- This data theft could pose significant supply chain and regulatory risk given LexisNexis’s foundational role for government and major firms. The exposure of government PII elevates the incident to a potential national security concern, maximizing regulatory exposure (GDPR/CCPA).
- Dataminr provided an early warning on the React2Shell vulnerability (46 hours before CISA’s KEV addition), emphasizing the value of real-time threat intelligence.
- Immediate remediation is critical for dependent organizations, requiring rotation of all integrated secrets/API keys, forced password resets, and enhanced identity verification.
- FulcrumSec is employing high-pressure extortion tactics, using financial liability projections potentially AI generated and prioritizing government data for maximum impact.
Incident Overview
Dataminr has identified a breach of LexisNexis’ cloud infrastructure by the hacking group FulcrumSec that allegedly took place on February 24, 2025. As a foundational data provider for 85% of the Fortune 500 and over 7,500 government agencies, LexisNexis holds a critical position in the global supply chain for legal research, identity verification, and financial compliance. LexisNexis has confirmed the intrusion, stating the compromised servers contained mostly legacy data (pre-2020).
In a statement to BleepingComputer on March 3, 2026, LexisNexis N&P confirmed the threat actor had gained access to the company’s AWS infrastructure by exploiting the React2Shell vulnerability in an unpatched React frontend app.
“These servers contained mostly legacy, deprecated data from prior to 2020, including information such as customer names, user IDs, business contact information, products used, customer surveys with respondent IP addresses, and support tickets,” a spokesperson said.
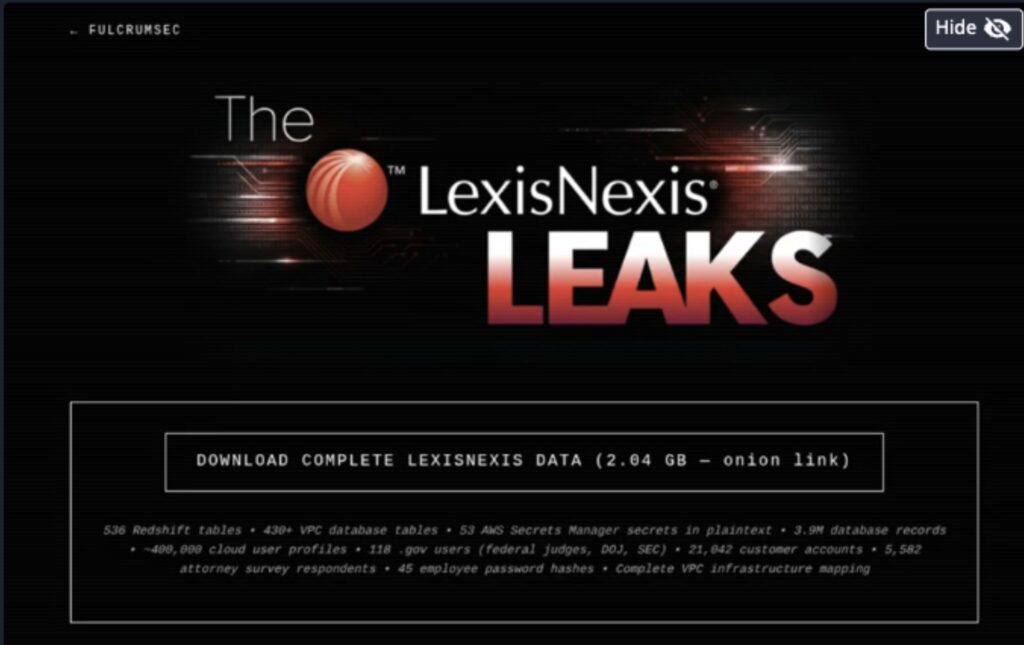
FulcrumSec claims to have exfiltrated the following data:
- Government Personnel Data: PII belonging to personnel from multiple U.S. state and federal agencies, creating heightened espionage and targeted social engineering risks.
- Sensitive Legal & Operational Data: The breach exposed sensitive data from top-tier law firms and thousands of internal feedback survey respondents, while revealing over 1,300 internal security incidents and extensive unpatched infrastructure vulnerabilities.
- Credential Exposure: 45 employee password hashes and 53 secrets from AWS Secrets Manager (including Salesforce and Oracle credentials).
- Plaintext Passwords: Discovery of plaintext customer passwords within the subject lines of customer support tickets, indicating systemic data handling failures.
FulcrumSec has published evidence of data exfiltrated on their dark web claims site, but Dataminr has not independently verified these claims.
Dataminr Detection
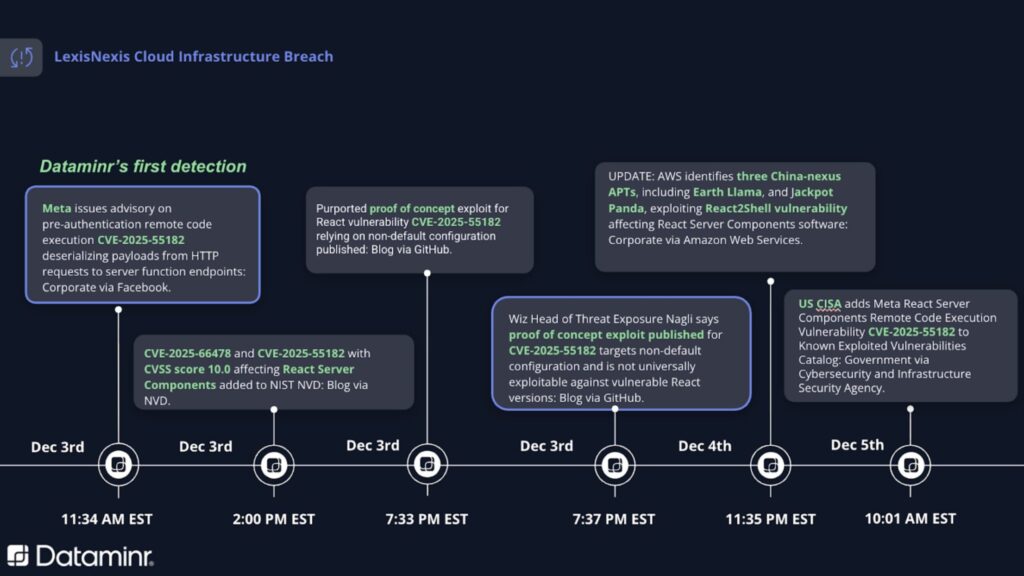
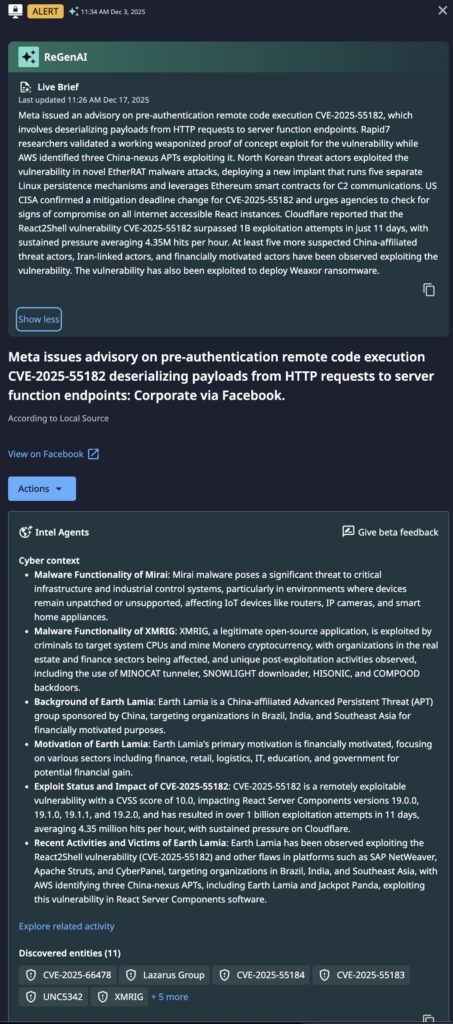
Dataminr alerted customers of the React2Shell vulnerability (CVE-2025-55182), beginning with a Meta advisory on December 3, 2025, at 11:34 AM EST, followed by a published proof of concept just eight hours later. This proactive notification preceded an AWS report on exploitation by China-nexus APTs on December 4 and occurred roughly 46 hours before CISA added the vulnerability to its Known Exploited Vulnerabilities (KEV) catalog on December 5.
Technical Details
The breach was reportedly facilitated via a vulnerable React container running under a specific AWS task role (LawfirmsStoreECSTaskRole) that had over-privileged access to production environments.
- Lateral Movement: Access to Secrets Manager provided the threat actors with credentials for integrated services, including Salesforce and Oracle databases, potentially allowing for deeper penetration into operational environments.
- Supply Chain Risk: The exfiltration of software supply chain credentials poses a direct threat to any organization with integrated software dependencies or API connections to LexisNexis services.
Per statements provided to BleepingComputer by LexisNexis, the breach is believed to be contained and the data exfiltrated was old and did not include PII or client application use data.
“Our investigation has confirmed that an unauthorized party accessed a limited number of servers.”
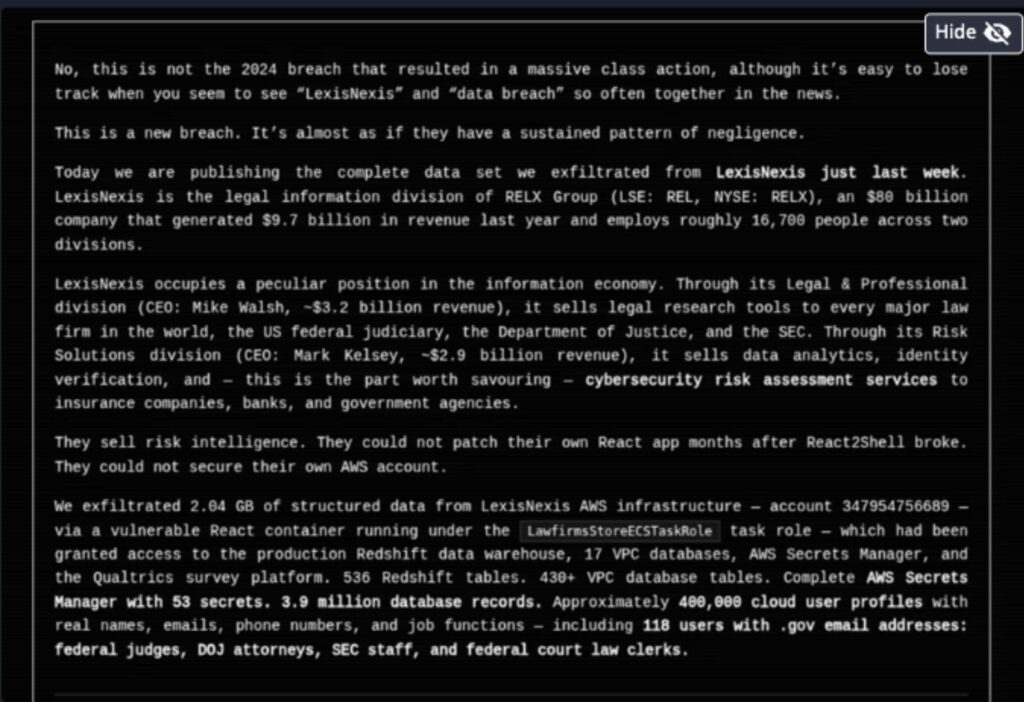
FulcrumSec has claimed responsibility. Their tactics involve high-pressure extortion and reputational damage. As part of this extortion process the threat actor published a report that projected specific financial liabilities for LexisNexis, including GDPR fines and lawsuit settlements. Dataminr research indicates that this report was possibly AI-generated. By specifically highlighting the theft of government personnel data, the group appears to be aiming for maximum visibility and regulatory pressure, positioning the breach as a matter of national security.
As a result of this breach, the threat actor claims to have access to:
- 536 Redshift tables
- 430+ VPC database tables
- 3.9M database records
- “~400,000” cloud user profiles
- 118 .gov users “(federal judges, DOJ, SED)
- 21,042 customer accounts
- 5582 attorney survey respondents
- Complete VPC Infrastructure mapping
Immediate Actions & Recommendations
Organizations utilizing LexisNexis for identity verification, legal research, or financial compliance must take immediate steps to mitigate downstream impact:
- Rotate Secrets & API Keys: Immediately rotate all API keys and service account tokens used for LexisNexis integrations. Audit AWS Secrets Manager or similar vaults for any shared or overlapping credentials.
- Credential Reset & Audit: Force password resets for any employees whose credentials may have been involved. Organizations should audit internal logs for any unauthorized access to Salesforce or Oracle databases.
- Review Identity Verification Workflows: Financial and government entities using LexisNexis for KYC/AML or identity checks should implement secondary verification layers (e.g., out-of-band MFA) to defend against synthetic identity fraud using stolen LexisNexis data.
- Harden Support Systems: Ensure ticketing systems do not allow the entry of sensitive data in unencrypted fields. Implement automated DLP scanning for “Subject” and “Description” fields.
- Monitor for Spear-Phishing: Alert government and executive personnel to an increased risk of highly targeted social engineering attacks leveraging the PII exfiltrated in this breach.
- Legal & Compliance Review: Evaluate third-party risk and notification requirements under GDPR/CCPA if your organization’s data was processed through the affected LexisNexis environments.

Stay Ahead of Emerging Threats
Learn more about how Dataminr helps cybersecurity customers get ahead of emerging threats.
Learn More