Key Takeaways
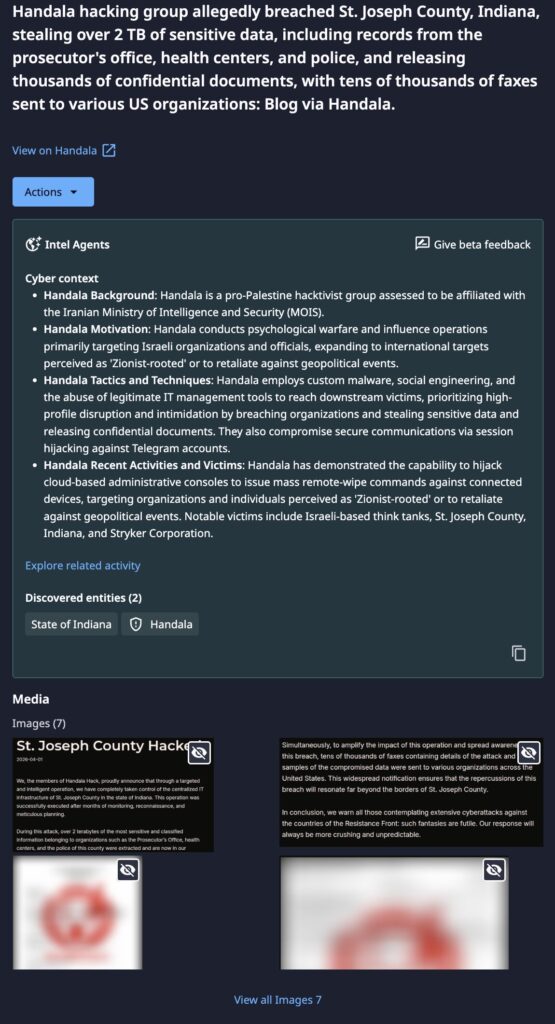
- Massive Data Exfiltration: Handala claims to have stolen over 2 TB of highly sensitive records, specifically targeting the prosecutor’s office, local health centers, and police departments.
- State-Linked Attribution: The group is assessed as a pro-Palestine hacktivist front affiliated with the Iranian Ministry of Intelligence and Security (MOIS), also tracked as Void Manticore and Storm-0842.
- Psychological Operations: The actors amplified the impact of the breach by releasing thousands of confidential documents and warning about outsized repercussions on other organizations.
Incident Overview
Handala, a disruptive Iranian-linked threat actor, announced the alleged successful compromise of the centralized IT infrastructure of St. Joseph County, Indiana. The group claims to have exfiltrated 2 TB of sensitive data containing records from the police department, health centers, and the prosecutor’s office.
Following the alleged theft, Handala released a message warning organizations about attacking Iran or its allies, as the group believes they can respond swiftly with widespread impact. They emphasized that the repercussions could “resonate far beyond the borders of St. Joseph County.” This activity is consistent with Handala’s broader strategy of psychological warfare following the February 2026 geopolitical escalations between the U.S. and Iran.
Technical Details
Handala typically leverages social engineering and session hijacking to gain initial footholds. Once inside, the group is known to abuse legitimate IT management tools to move laterally and maintain persistence. Most notably, in the March 2026 attack on a major medical device manufacturer, Handala gained access to a Microsoft Intune administrative console and wiped over 200,000 devices globally. The group’s TTPs frequently involve manual, “hands-on-keyboard” operations and more recently custom wiper malware (e.g., Handala Wiper, Hamsa Wiper) designed to overwrite the Master Boot Record (MBR).
Threat Actor Motivation
Handala is assessed to be a state-directed persona for Iran’s MOIS, used to carry out destructive cyber operations while maintaining a layer of deniability through hacktivist messaging. Their primary motivation is disruption and signaling rather than financial gain. The group targets organizations perceived as “Zionist-rooted” or those critical to U.S. infrastructure in retaliation for international military actions.
Dataminr Detection
Immediate Actions & Recommendations
Organizations can proactively protect themselves against Handala and groups who use similar tactics by doing the following:
- Harden Endpoint Management: Immediately secure all mobile device management (MDM) and endpoint management consoles, such as Microsoft Intune, with FIDO2-compliant hardware security keys and Just-in-Time (JIT) access.
- Audit Privileged Credentials: Review all administrative role assignments and audit logs for anomalous remote execution commands, specifically looking for mass wipe or system reset triggers.
- Monitor for Anomalous Access: Search VPN and RDP logs for successful logins originating from unusual geographic regions or hosting providers (e.g., Vultr, DigitalOcean, Kaopu Cloud), which are frequently used by Iranian proxy networks.
- Session Security: Implement strict policies to prevent session hijacking, including shortened session timeouts and the enforcement of re-authentication for sensitive administrative actions.
- Secure Sensitive Data: Segment and isolate critical data repositories, such as law enforcement and health records, ensuring that backups are immutable and stored off-network to prevent deletion by wiper malware.

Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report