Key Takeaways
- Aggressive Claims vs. Limited Impact: Hacktivist groups frequently boast about compromising high-consequence targets (e.g., nuclear facilities, water systems), but most operations result in minor disruptions like website defacements or localized outages.
- Targeting Low-Hanging Fruit: Most successful compromises rely on identifying internet-exposed devices (PLCs or HMIs) and exploiting default or weak authentication.
- Operational Technology (OT) Incompetence: Threat actors often lack the deep system understanding required to bypass engineering safeguards or cause significant physical damage, though they may still impact small communities.
- State-Aligned Trajectory: A growing trend shows hacktivism overlapping with state interests, with groups like CyberAv3ngers and CyberArmyofRussia_Reborn linked to the IRGC and GRU, respectively.
- Simple Defensive Efficacy: Most hacktivist threats can be effectively neutralized by removing direct internet access for OT equipment and enforcing complex, multi-factor authentication.
Incident Overview
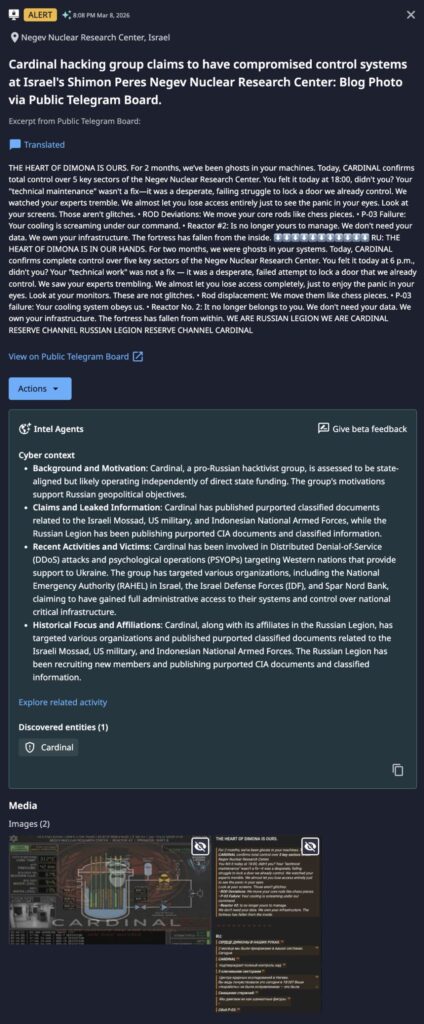
On 08 March 2026, as war raged across the Middle East, a pro-Russia “hacktivist” group known as “Cardinal” made a bold claim: that the Shimon Peres Negev Nuclear Research Center near Dimona, Israel, was hacked. The group posted pictures of their alleged exploits to Telegram, claiming they could manipulate control rods and similar infrastructure within the nuclear facility.
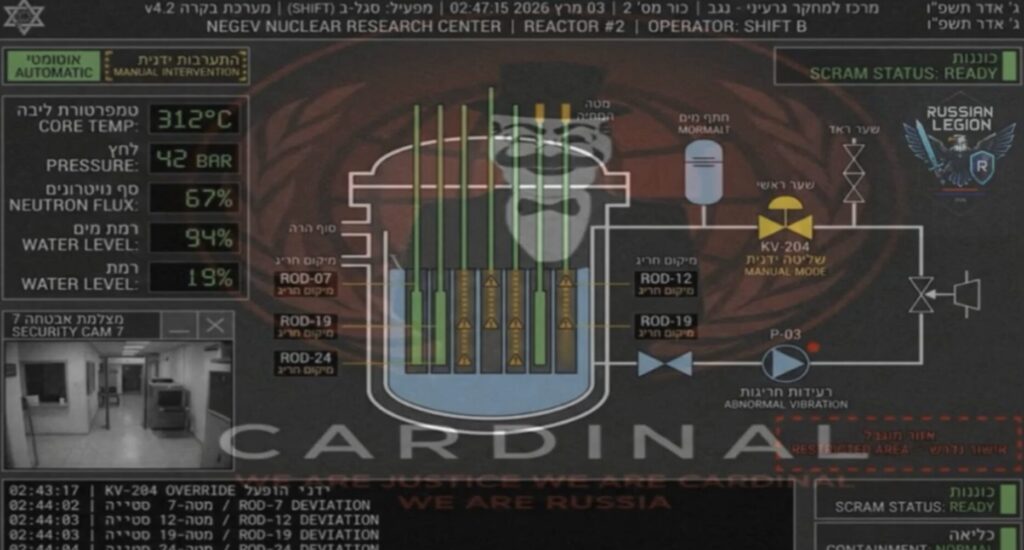
At first glance, such an intrusion appears significantly concerning as compromise of a nuclear reactor’s control systems could allow for effects ranging from “scramming,” or shutting down the reactor to removing control rods entirely to allow for uncontrolled fission. Yet no panicked statements or signs of distress from the allegedly affected nuclear center were recorded, and the frightening claims passed without statement or much notice. More interesting still, Cardinal’s claims come a bit less than two years after an entity cloaking itself in the dated “Anonymous” label claimed a similar hack of the same facility. The distance between alarming claims and any real world consequence is significant, and should give us pause when evaluating the claims of hacktivist entities.
Hacktivism in the Real World
“Hacktivism” itself is not new, dating back to defacement and similar activity decades ago. What has made hacktivism more interesting are two trends: the increasing overlap of hacktivism with state interests (if not outright state control), and the willingness of hacktivist entities to target or attempt to manipulate critical infrastructure systems. As a result, hacktivism now appears to represent a distinct and direct threat to civilians and societies, but such concerns must be tempered with the reality that hacktivist operations have largely been ineffective or extremely limited in scope, impact, or consequence.
So-called hacktivist operations have been aggressive in pursuing multiple critical infrastructure entities over the past several years. Examples include the following:
- Exploitation and defacement Unitronics devices in Israel and the United States water and wastewater sectors. by the CyberAv3ngers, a group linked to the Iranian Islamic Revolutionary Guard Corps, or IRGC, from 2023 to 2024.
- The compromise of water systems in the town of Muleshoe, Texas in 2024 by Russia-linked entity CyberArmyofRussia_Reborn, which is linked to Russia’s Military Intelligence or GRU.
- Unspecified pro-Russia entities compromising a small dam in Norway in 2025.

Between Russia’s long-running invasion of Ukraine and various conflicts in the Middle East since the Hamas terror attacks of October 2023, multiple “real world” events have fueled subsequent “hacktivist” actions largely (but not exclusively – see Predatory Sparrow) targeting European, North American, and Israeli entities. Yet for all the bluster and frightening claims of destruction, chaos, and similar, operations have been limited to defacement (as seen in the Unitronics hacks) or impacting relatively small and isolated entities. The former is simply annoying, while the latter does contain some element of concern but for very limited populations and use cases.
Note that exceptions to the above do take place. At the time of this writing, a US-based medical device manufacturer appears to have been the victim of a significant wiper attack by Handala, a pro-Palestinian hacktivist entity. Of note, Handala is closely associated with Iran’s Ministry of Intelligence and Security, making it more “state-directed” than merely “state-aligned” in the hacktivist sense. In any event, hacktivist entities (or those posing as such) cannot be completely disregarded, but their record of success (or lack thereof) should be noted to ensure defensive resources, attention, and concern are appropriately aligned with the scope and nature of the threat in question.
Recommended Approach and Key Actions
Based on this combination of either no or very limited impact in the vast majority of instances, we can rightly ask whether such hacktivist entities are worth much concern. As noted elsewhere, these entities can be viewed as “low skilled threats” that are largely opportunistic in nature with little understanding of the systems they access. From events to date, we can identify the following commonalities in hacktivist targeting of critical infrastructure:
- Dependence on identifying internet-exposed systems related to critical infrastructure operations, such as internet-connected programmable logic controllers (PLCs) or human machine interfaces (HMIs) often indexed through services such as Shodan.
- Reliance on default or weak authentication mechanisms for such devices allowing for easy access to exposed systems.
- Lack of understanding of system functionality, such as what specific actions would be necessary to cause a truly concerning event and that could circumvent other safety controls such as engineering safeguards.
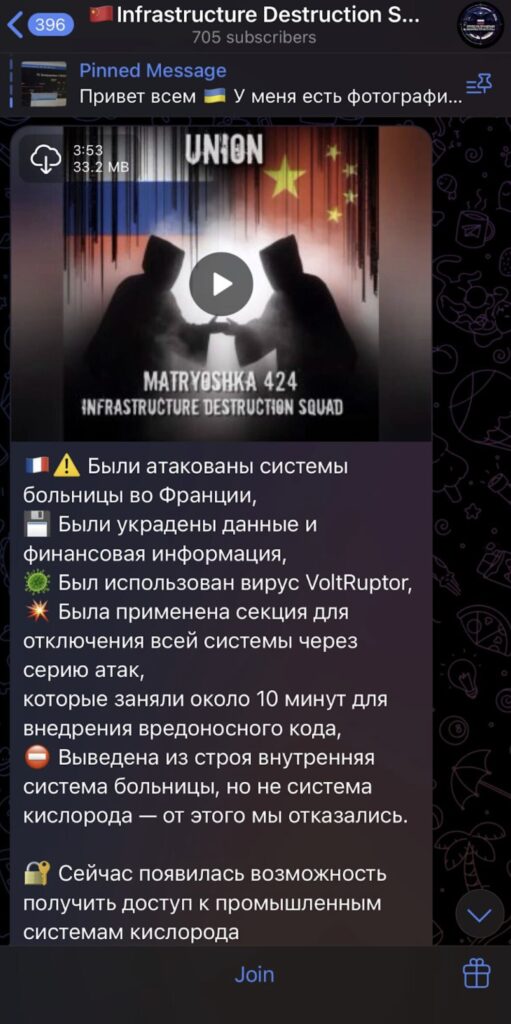
The result of all of the above is more “cyber annoyance” than “cyber war.” Certainly, small communities with similarly small utilities and service providers may be impacted by such entities. This is a concern of course, but scaling such operations to major population or economic centers appears far beyond the reach of these actors. While some hacktivist groups, such as the pro-Russia Infrastructure Destruction Squad, claim to possess specific capabilities for operational technology (OT) systems (“VoltRuptor”), no evidence has ever emerged to support this boast.
Despite the limited nature of most threats, the fact that these systems remain accessible to threat actors, even incompetent or “basic ones,” remains concerning. Based on an evaluation of known “hacktivist” compromises of critical infrastructure and related systems, there are two key actions that organizations can take to defeat the vast majority of such operations:
- Identify and remove direct internet access for critical systems such as OT equipment or similar management applications.
- Change default or simple passwords to more complex items, and where possible implement multifactor authentication.
Industry collaboration has shown us that the first action is highly achievable and demonstrates the need for organizations, especially smaller ones with fewer resources, to adopt security controls to reduce their attack surface. Meanwhile, the threat of these type of hacktivist operations to larger, security-mature organizations remains relatively small due to the use and enforcement of fundamental security best practices such as attack surface management and multifactor authentication enforcement.
At face value, hacktivist operations appear to be a significant concern, however they tend to fall apart under robust scrutiny due to either irrelevance or incompetence. That said, they can be highly disruptive to organizations that reside on the wrong side of the cyber poverty line, so they cannot be completely dismissed.
The potential impact of threats like these can be significantly reduced by implementing standard security controls and hygiene, which helps ensure continuity of services and protect organizational integrity. By adopting a realistic approach to the hacktivist threat instead of hyping it beyond reason or available evidence, we can adequately address this issue and starve this nuisance of oxygen.