Almost immediately following the initial strikes on Iran in late February 2026, speculation swirled in the information security community about the potential cyber warfare element in the unfolding conflict. Since then, hundreds of claims have surfaced on cyber attacks linked to the conflict, with only a handful having been publicly acknowledged as successful. With the exception of the mass wiping event at a U.S. medical device company, which in turn prompted a limited and more psychological response from U.S. law enforcement, the ratio of actual events to potential noise has been skewed towards the latter.
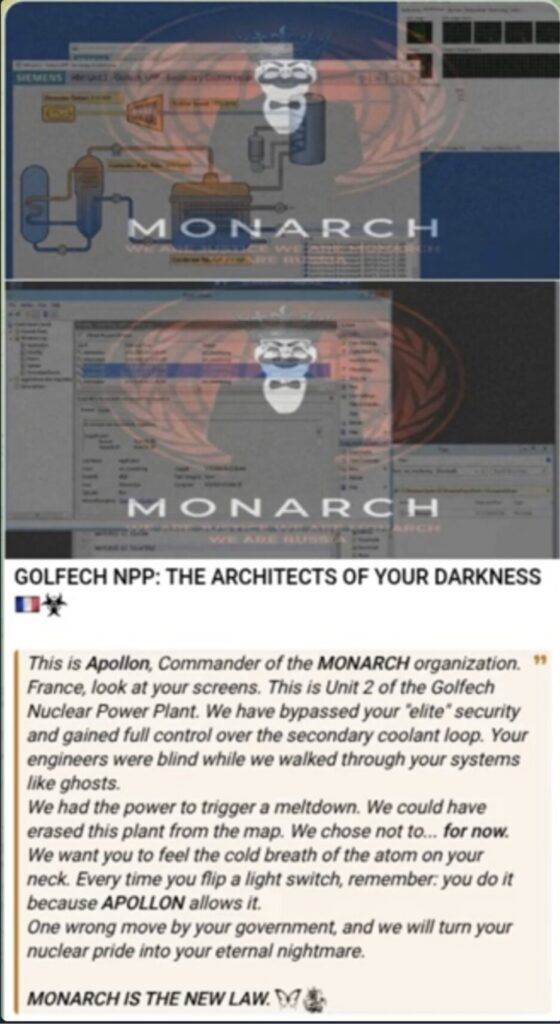
The majority of discussion about cyber incidents tied to the Iran war have unfolded across social media platforms like Telegram, where a veritable army of cyber personas referred to as “hacktivists” make concerning claims. Many, such as the group known as Monarch (fka Cardinal), claim critical infrastructure and nuclear power facility breaches. Although concerning if true, no evidence surfaced of a successful compromise at any of the supposed victims. As a result of events like this, a degree of nuance and caution is necessary in evaluating the cyber warfare element of the Iran war and what it tells us about conflicts in the future.
Shifting Trends
Irrespective of successes, the sheer volume of claimed incidents has increased significantly since the start of hostilities in February. Examining Dataminr’s cyber alerting data from the first 18 days of the conflict, there was nearly a fourfold increase in Iran-linked or -sympathetic entities claiming successful or impending cyber operations as the 18 days leading up to the conflict (February 9-27).
This substantial increase in activity—combined with historical (if somewhat dated) examples of Iran-linked disruptive cyber events from Shamoon and otherwipers to extensive distributed denial of service activity—makes tracking such actions both challenging and important for defenders. In the former case, the sheer volume of activity makes it frustratingly difficult to separate actual areas of concern from overall noise. In the latter, historical wipers causing severe impacts at oil and gas entities—much like what happened with the medical device manufacturer—mean defenders and analysts cannot simply disregard these items, either.
2012
Shamoon
Significant disruption of Saudi Aramco IT operations
2016
Shamoon2
Targeting of entities in Saudi Arabia
2016
StoneDrillt
Targeting of entities in Saudi Arabia
2019
ZeroClear
Targeting of Middle Eastern oil and gas and energy entities
2019
Dustman
Targeting of oil and gas entities in Bahraina
2020
DEADWOOD
Targeting Israeli private organizations and supply chain
2022
ROADSWEEP
Targeting Albanian government networks
2023
Bibi Wiper
Targeting various Israeli organizations
An exemplary selection of destructive, wiper-style malware associated with Iranian or Iran-adjacent threat actors since 2012. Source: Dataminr
Additional examination of Dataminr intelligence revealed 36 distinct groups, that are either empathic towards or directly affiliated with Iran, claiming varying degrees of cyber operations. These 36 groups advertised critical infrastructure targeting nearly 500 times, although approximately 80% of such actions were related to varying types of DDoS activity as opposed to direct manipulation or disruption of operating processes. While some particularly alarming statements have surfaced concerning energy and electric infrastructure, such as the nuclear items referenced above and alleged disclosure of Israeli electric sector information, none of these items have manifested as actual disruptions or similar impacts.
![The Iran-aligned group Handala Hack claims to have possession of [insert country]’s map of electricity and water infrastructure. Source: Dataminr](https://www.dataminr.com/wp-content/uploads/2026/03/Screenshot-2026-03-27-at-11.23.32-AM-1024x596.jpg)
Cutting Through the Noise to Understand the Real Threat
While most cyber events to date during this conflict have been underwhelming, the possibility nonetheless exists of more activity and impact in the future. Given the asymmetric nature of the Iran conflict, and Iran’s ability to respond with kinetic or physical attacks largely destroyed or limited, cyber and economic responses become their most powerful weapons. As demonstrated in the cyber attack against the medical devices manufacturer, organizations far removed from the physical battlefield may find themselves opportunistically targeted by Iranian or Iran-linked entities seeking to inflict any visible impact or damage.
We have thus almost certainly reached a point where some form of civilian, and not just military, targeted “cyber” is now an inevitable part of modern conflict. At present, much of this is relatively low-level (i.e., “cyber annoyance”) and at first glance easily dismissed. But as such conflicts emerge over time, the relative ease and low cost of opportunistic disruptive operations behind hacktivist personas become alluring ways to “hit back” when other options are not possible.
Nuanced understanding of this threat is therefore required to appropriately respond to events. Outlandish, unrealistic hacktivist statements should be treated with appropriate caution, but also not be blindly accepted as true. It is important to still acknowledge that there is always a realistic possibility that such groups could identify a vulnerability, gap, or similar for exploitation that may lead to significant disruption. Given the history of Iran and Iran-linked operations including the deployment of multiple forms of wiping malware or wiping capabilities, organizations must remain appropriately vigilant—understanding the reality of the threats in play while not overhyping every possible claim.
What This Tells Us About the Future
Ultimately, cyber-nexus events around the current Iran war are eclipsed by the physical realities of the conflict—from its impacts on global energy markets to the very real loss of life as a result of attacks and bombardment. By appropriately acknowledging where cyber fits into the broader narrative and correctly aligning its impacts and significance given available information, network defenders and leadership can orient themselves properly to the risk presented by such activity.
In the end, information security leaders and decision makers must remain aware of and attuned to the ebb and flow of such conflicts, both to recognize when items are unrealistic and unfounded, and when true concern is warranted given the possible impacts of a conflict-associated intrusion.

Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Read Report