Key Takeaways
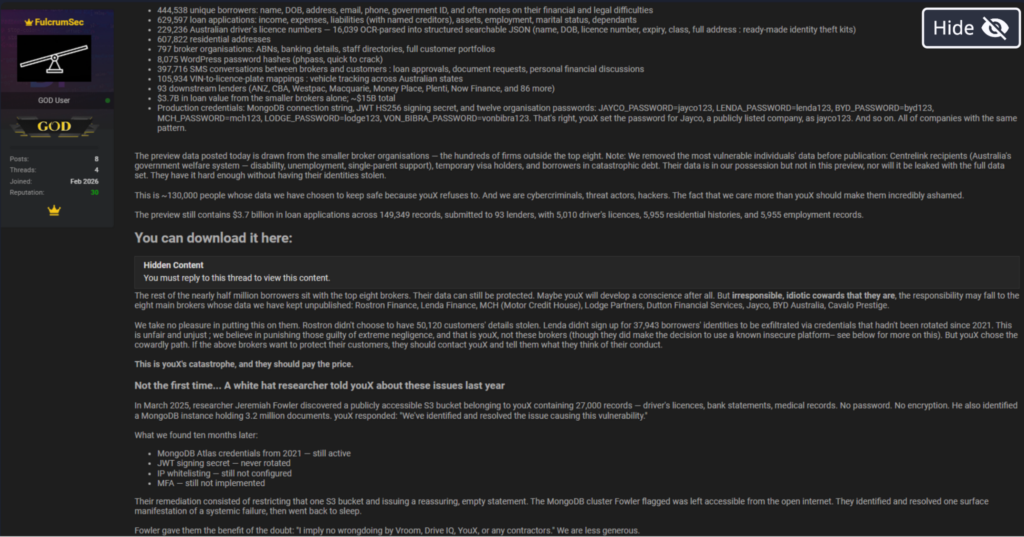
- Massive PII and Financial Exposure: The exfiltration targeted 22 production databases, including a MongoDB Atlas cluster, compromising government IDs, 229,000+ driver’s license numbers, and loan application details valued at $15 billion.
- High-Risk Credential Compromise: The theft of 8,075 password hashes for broker employees poses a critical risk for unauthorized live platform logins, especially as hashes reportedly use weak, easily crackable MD5 encryption.
- Aggressive Extortion Tactics: FulcrumSec utilizes a “steal and squeeze” model, bypassing encryption to focus on data exfiltration. They have actively engaged in public shaming by releasing internal emails, court summons, and plaintext data samples to pressure the victim.
- Systematic Security Failures: The group exploited unrotated credentials from as far back as 2021, a lack of MFA, and misconfigured cloud permissions—vulnerabilities previously flagged by researchers in March 2025.
Overview of the Incident
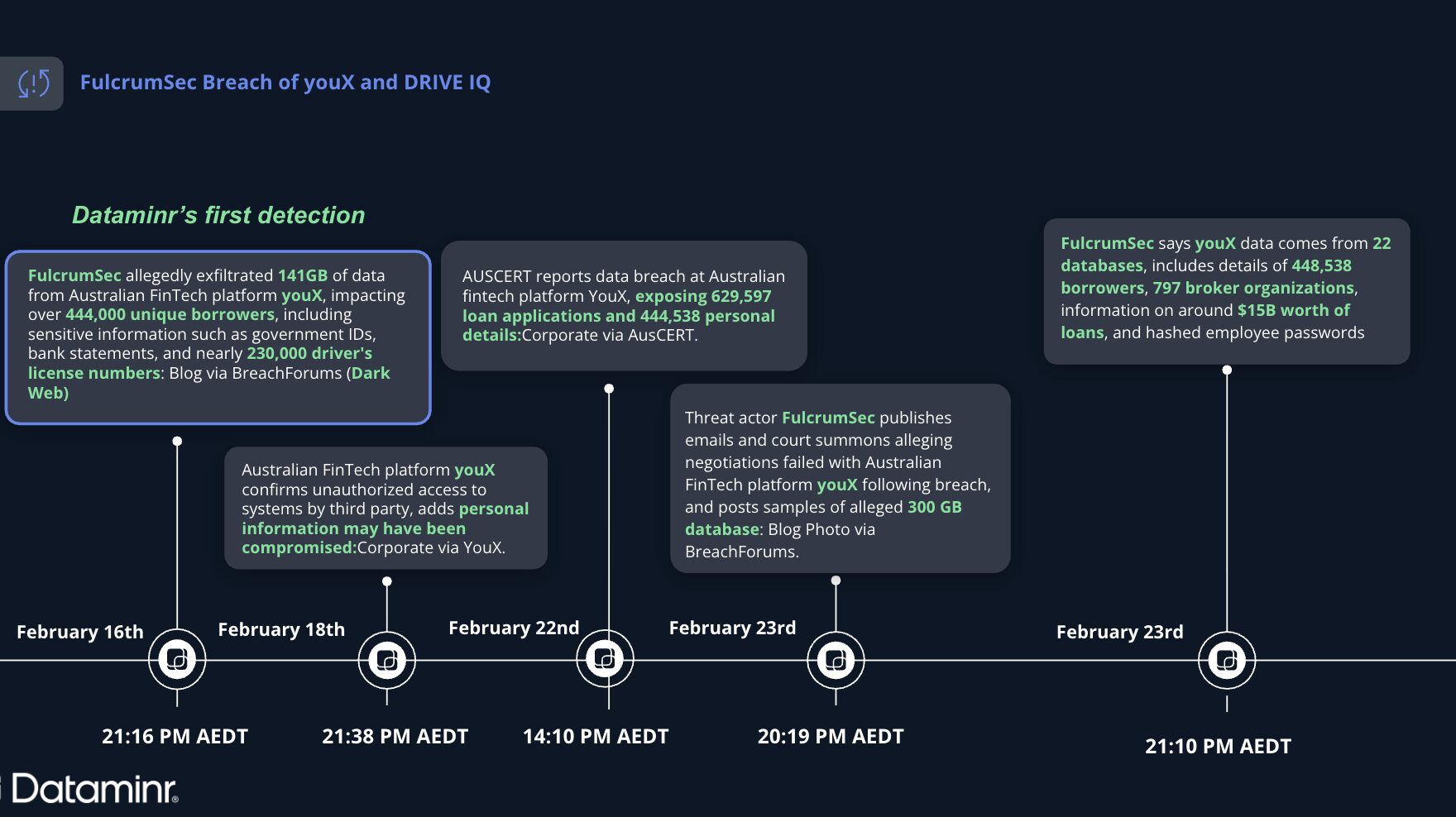
In February 2026, the threat actor group FulcrumSec allegedly exfiltrated approximately 300 GB of data from the Australian FinTech platform youX (formerly known as DRIVE IQ). The breach reportedly impacts over 444,000 unique borrowers and nearly 800 broker organizations. Following a breakdown in ransom negotiations, the threat actor republished samples of the stolen data, as well as alleged internal emails and court summons to pressure the organization. The exfiltration reportedly targeted 22 production databases, including a MongoDB Atlas cluster.
Dataminr Detection
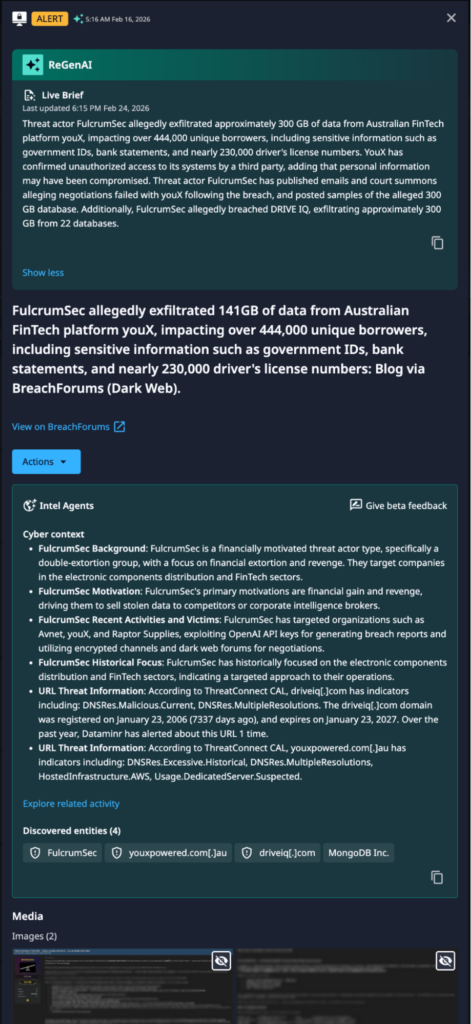
Technical Details of Incident
The exfiltrated data encompasses a significant volume of sensitive personally identifiable information (PII) and financial records, including government IDs, over 229,000 driver’s license numbers, financial statements, income and debt details, and residential and employment histories. Furthermore, the breach included 8,075 password hashes belonging to broker employees, posing a risk for unauthorized live platform logins, as well as private SMS conversations and loan application details valued at $3.7 billion. The infrastructure impacted includes a 141GB MongoDB Atlas cluster and a 16GB system identified as “prodApply.”
Threat Actor Profile: FulcrumSec
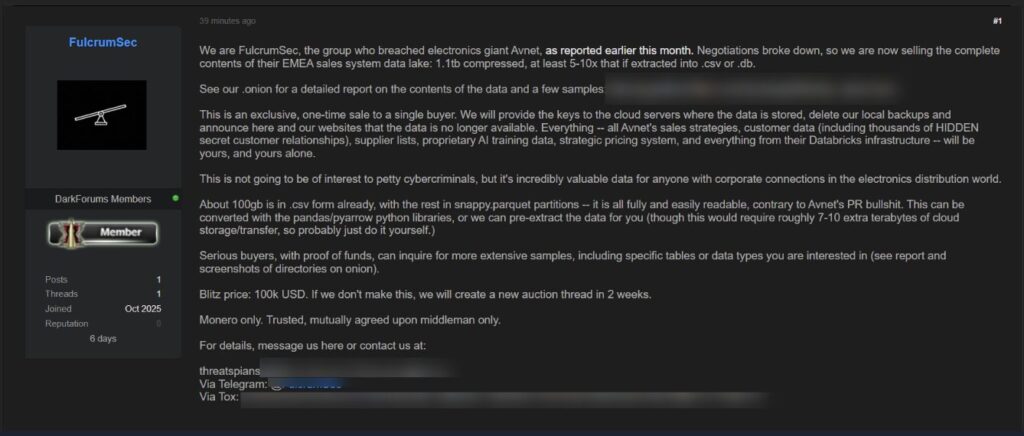
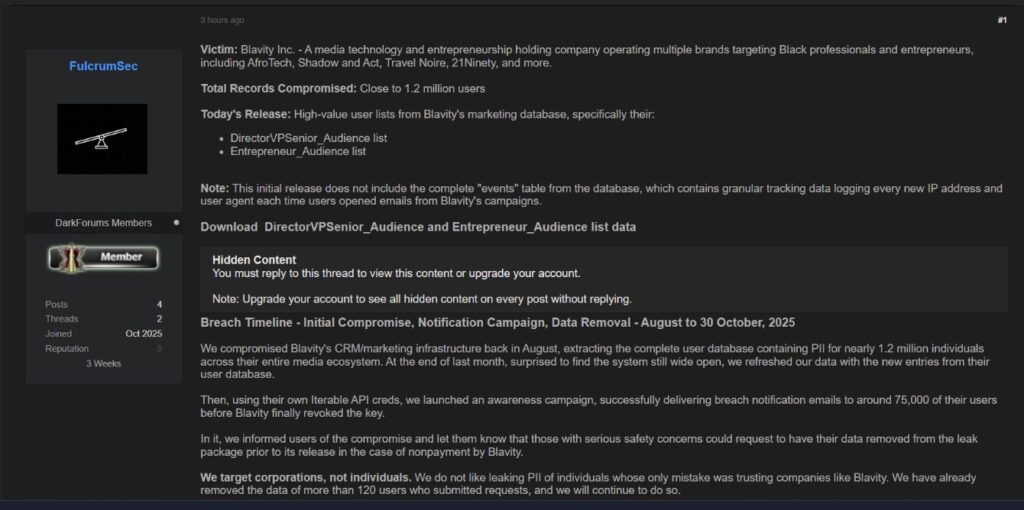
The group, known by the alias “The Threat Thespians,” was first observed around September 2025 and is primarily motivated by financial gain through extortion and data auctioning. Their operating model focuses on data exfiltration and blackmail, often bypassing system encryption entirely to “steal and squeeze,” and they communicate using the email addresses threatspians@fulcrumsec[.]net and their primary address, fulcrumsec@tuta[.]io.
Known Tactics, Techniques, and Procedures (TTPs)
FulcrumSec is known for high-speed data extraction, specifically targeting cloud-hosted databases and sales tools.
- Targeted Environments: Azure, Databricks, and externally hosted cloud storage clusters.
- Initial Access: Exploits unrotated credentials, API keys, and misconfigured cloud permissions. It is likely that they purchase credentials via Initial Access Brokers (IABs).
- Data Handling: They frequently exfiltrate data in compressed formats (e.g., 1.3 TB compressed which can expand to 7–12 TB raw).
- Pressure Tactics
- Double Extortion: Threatening to leak sensitive info unless paid.
- Public Shaming: They host a dedicated “Leak Site” on both the Clearnet and TOR networks.
- Counter-Messaging: They actively monitor victim public statements. If a victim claims the data is “unreadable” or “unimportant,” the group often releases plaintext samples to contradict them.
Previous FulcrumSec Claims Against Impacted Organizations
October 7, 2025: U.S.-based electronics company Avnet:
November 10, 2025: U.S. media company Blavity:
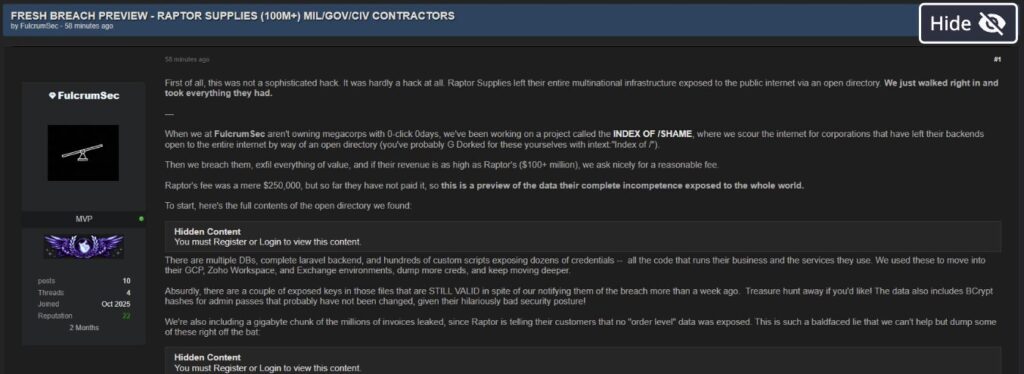
December 15, 2025: UK-based industrial parts company Raptor Supplies:
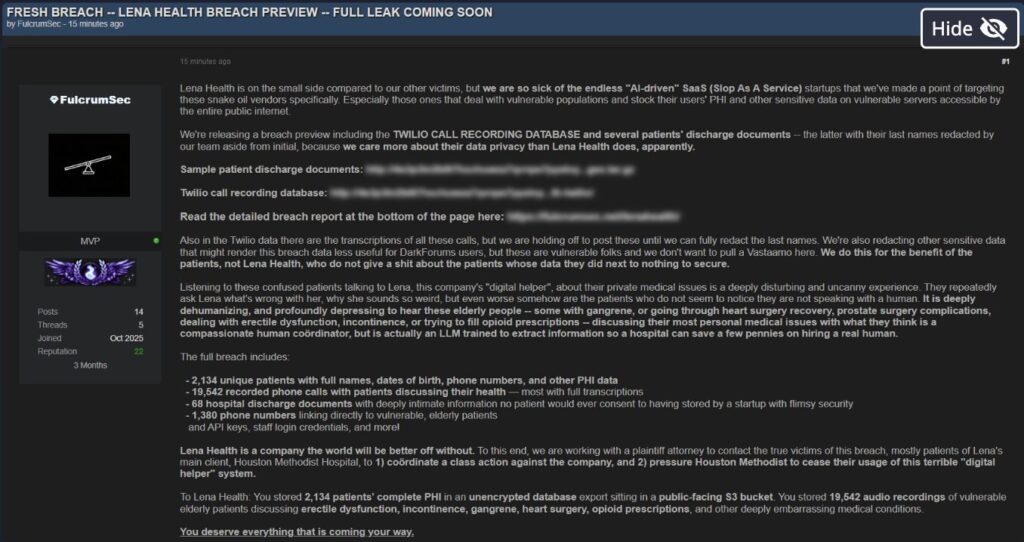
January 26, 2026: U.S. healthcare company Lena Health:
Dataminr’s Recommendations
To protect an organization against FulcrumSec and other threat actor groups that leverage similar TTPs, security teams should consider the following:
- Red Team Exercise: Conduct automated and manual “secret mining” across the SDLC—targeting Git commit histories, CI/CD pipeline logs, and misconfigured cloud storage (S3/Azure Blobs)—to identify exposed API keys and credentials; subsequently, attempt to use discovered secrets to bypass IAM restrictions and demonstrate lateral movement into production databases or sensitive cloud environments.
- Database Hardening: Audit and secure all MongoDB and cloud storage instances. Ensure they are not publicly accessible and utilize end-to-end encryption for data at rest and in transit.
- Enforce Universal MFA: Immediately implement phishing-resistant MFA across all administrative and broker accounts to neutralize the threat of compromised password hashes.
- Credential Rotation: Force a mandatory password reset for all internal employees and external broker users. Rotate all API keys and cloud service credentials (especially for MongoDB Atlas).

Stay Ahead of Emerging Threat Actor Activity
Learn more about how Dataminr helps cybersecurity customers get ahead of emerging threats.
Learn More