Key Takeaways
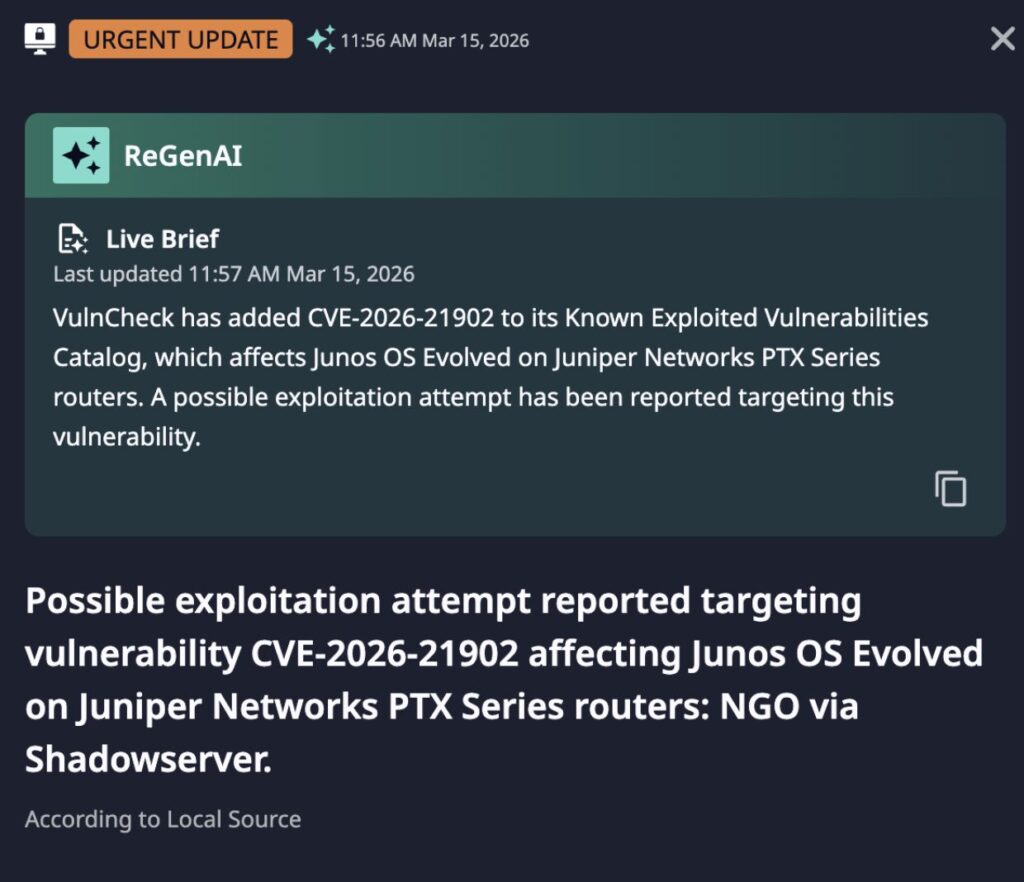
- A newly-disclosed vulnerability, CVE-2026-21902, can impact Juniper PTX devices and is now under possible exploitation in the wild.
- Such devices are typically used in high-bandwidth, high-traffic environments used by telecommunications providers and for communications between data centers.
- Adversaries are increasingly interested in compromising these types of equipment for espionage purposes, as seen in the long-running Salt Typhoon campaign.
Incident Overview
CVE-2026-21902 was initially disclosed by Juniper in late February 2026 as an out-of-band patch for an unauthenticated remote code execution (RCE) vulnerability in Junos OS Evolved for Juniper PTX devices. At the time of disclosure, no known exploitation of this critical vulnerability (CVSS 9.8) was occurring. However, shortly after disclosure, security researchers were able to analyze the vulnerability to produce working exploit code demonstrating a potential quick turn-around from disclosure to weaponization.
This potential was likely realized by 15 March 2026, when Shadowserver monitoring identified potential exploitation attempts for CVE-2026-21902, and the vulnerability was added to VulnCheck’s Known Exploited Vulnerabilities (KEV) database.
Although available information is not indicative of widespread exploitation, the severity and nature of the vulnerability make this a concerning development for organizations running the relevant hardware and software.
Dataminr Alert and Risk Assessment
CVE-2026-21902 affects Juniper PTX series routers. These are high-performance devices designed for routing traffic in environments such as telecommunications backbone networks and inter-datacenter communications. As such, these devices may not be commonly accessible externally, but represent a core functional component for many technology and communications organizations.
More concerning still is that vulnerabilities similar to CVE-2026-21902 have been weaponized by threat actors targeting the telecommunications and related industries. Most notable of these entities is the People’s Republic of China (PRC) linked Salt Typhoon, responsible for global breaches of multiple telecommunications networks for information gathering and espionage purposes. Another PRC-linked group, UNC3886, is also associated specifically with Juniper router targeting, albeit older versions of the Junos operating system.
Threat actors increasingly target network devices and appliances for a variety of purposes, from initial access to victim environments to the creation of proxy networks for malicious use. CVE-2026-21902 does not appear to fit this pattern given the nature and network location of the vulnerable devices. However, as part of long-running intrusions or espionage-focused campaigns, this vulnerability could be vital for adversaries to achieve access to critical networking equipment. Possibilities would then include data and traffic capture, traffic shaping, or even potential prepositioning for future disruptive operations on critical communication backbones.
CVE-2026-21902 may not, therefore, be a widely exploited vulnerability in the same fashion of vulnerabilities on widely-deployed, external-facing assets such as VPNs. But this vulnerability will be a significant item of concern for organizations running such equipment given the sensitivity and criticality of the functions dependent on or related to the vulnerable devices.
Immediate Actions & Recommendations
- Apply the Juniper patch for CVE-2026-21902 where possible as soon as is practical.
- Disable the anomalies service per Juniper guidance if patching is not possible and the anomalies service is not mission critical via the command request pfe anomalies disable.
- Limit connectivity to vulnerable devices to only known-trusted, required networks and systems when patching or workarounds are not possible.
Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Read Report