Key Takeaways
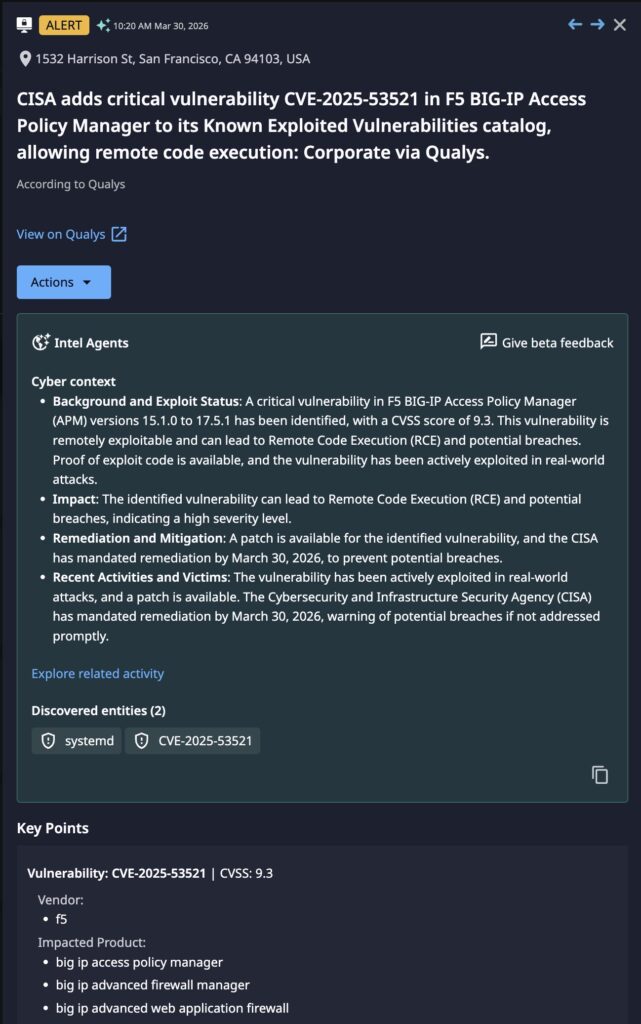
- Critical Severity: CVE-2025-53521 is a pre-authentication Remote Code Execution (RCE) vulnerability with a CVSS score of 9.3.
- Nation-State Nexus: The flaw is linked to UNC5221, a China-affiliated espionage group that reportedly breached F5’s internal engineering systems to gain a “roadmap” of undisclosed vulnerabilities.
- High Impact Components: The vulnerability affects the data plane of F5 BIG-IP Access Policy Manager (APM), Advanced Firewall Manager (AFM), and Advanced Web Application Firewall (WAF).
- Integrity Risks: Exploitation may involve stealthy modifications to sys-eicheck, the system integrity checker, potentially causing compromised devices to provide false health reports.
Incident Overview
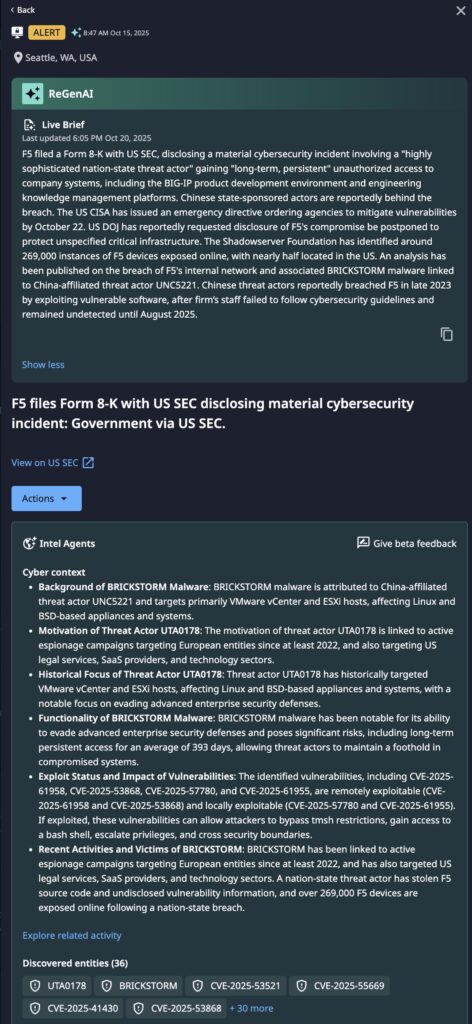
Initially disclosed in October 2025 as a denial-of-service (DoS) issue, CVE-2025-53521 was reclassified in March 2026 as a critical remote code execution (RCE) vulnerability with a CVSS score of 9.3. This adjustment followed evidence of active exploitation and a high-probability connection to a prior compromise of F5’s internal engineering knowledge management systems. In that breach, threat actors—identified as the China-nexus group UNC5221—reportedly accessed documentation on undisclosed vulnerabilities, effectively securing a roadmap of unpublished security flaws across the BIG-IP product line.
Dataminr identified this trajectory significantly ahead of public reclassification. On October 15, 2025, internal AI models escalated CVE-2025-53521 as a high-impact threat despite its then-current DoS rating. This early identification enabled defensive action five months before the March 28, 2026, CISA emergency mandate for federal remediation.
Technical Details
- Vulnerability Type: Pre-authentication Remote Code Execution (RCE).
- Attack Vector: The flaw resides in the data plane; attackers can execute arbitrary system commands via crafted requests without requiring valid credentials or user interaction.
- Affected Components: F5 BIG-IP Access Policy Manager (APM), Advanced Firewall Manager (AFM), and Advanced Web Application Firewall (WAF).
- Scope: Impacted versions include 15.1.0–15.1.10, 16.1.0–16.1.6, 17.1.0–17.1.2, and 17.5.0–17.5.1.
- Integrity Concerns: Exploitation may involve modifications to sys-eicheck, the BIG-IP system integrity checker, potentially causing compromised devices to return false health reports.
Threat Actor and Motivation
The F5 intrusion activity is attributed to UNC5221, a sophisticated China-affiliated espionage group. The group is known for zero days, maintaining long-term persistence and utilizing specialized tools such as the BRICKSTORM backdoor. Their primary motivation is the compromise of perimeter access infrastructure to intercept credentials, manipulate access policies, and establish a pivot point for lateral movement into protected internal networks.
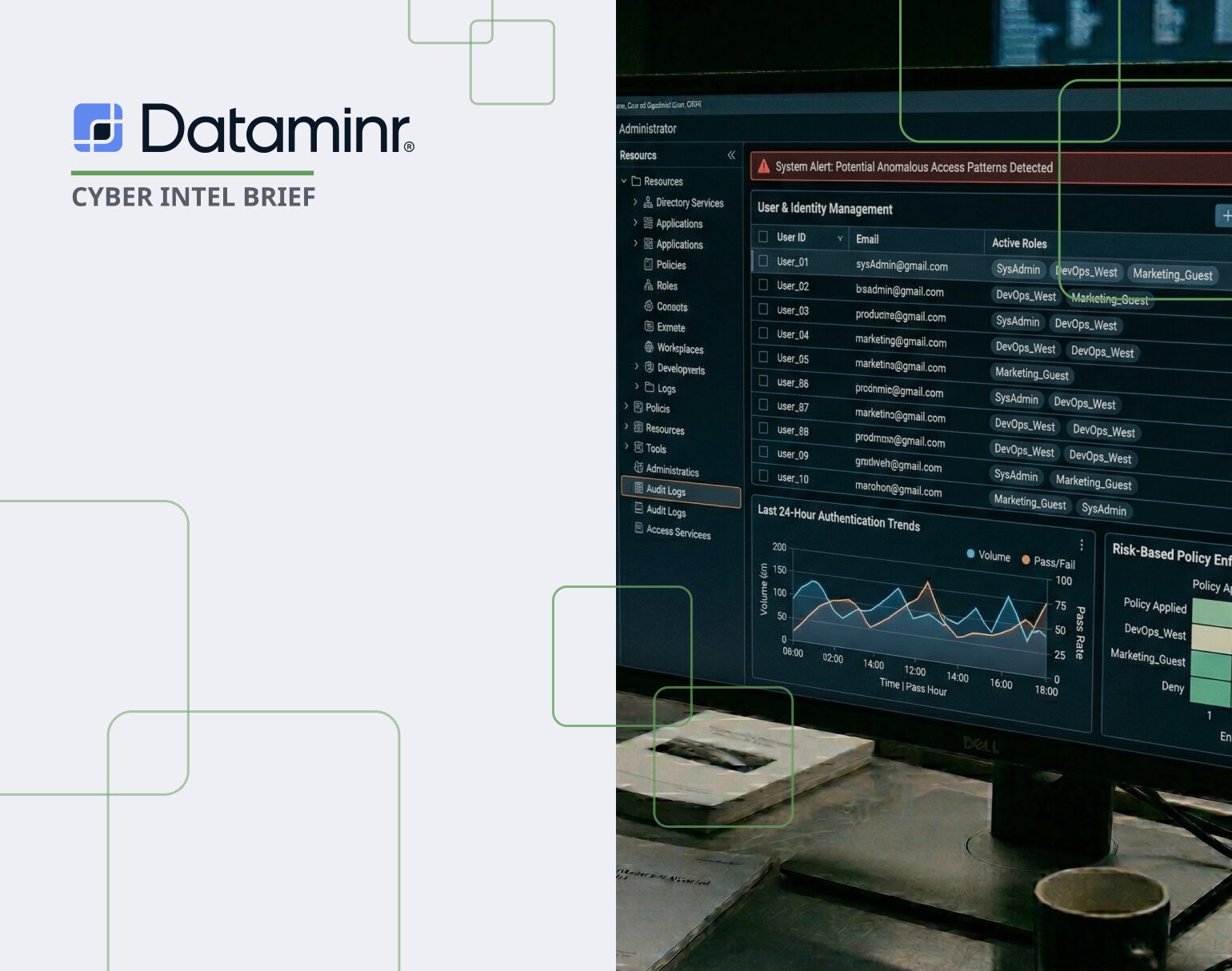
Dataminr Detection and Risk Quantification
According to Dataminr Continuous Control Monitoring with Risk Quantification, there are a number of elements that contribute to this being a vulnerability with both high impact and high likelihood of exploitation.
- Active nation-state exploitation (suspected China-nexus UNC5221), an at least 12-month dwell time inside F5’s network, and the potential pre-deployment of Brickstorm backdoors on customer systems create an unusually elevated threat with estimated losses of $10M–$150M+.
- F5 BIG-IP devices have a well-documented history of mass exploitation (CVE-2021-22986, CVE-2022-1388), and breaches of identity and perimeter access infrastructure — including the MGM Resorts attack (~$100M in reported losses)—have historically driven losses well over $100M.
Dataminr alerted on this vulnerability months before the CISA mandate. By leveraging AI models to prioritize “high-potential” vulnerabilities, Dataminr helped organizations cut through the noise of standard vulnerability feeds. This proactive identification allowed security teams to:
- Investigate early signs of reconnaissance with Client-Tailored Threat Intelligence.
- Harden defenses on external-facing F5 assets with Agentic TI Ops.
- Avoid the emergency fire drill typically associated with CISA KEV deadlines by leveraging Investigation Insights.
Immediate Actions and Recommendations
- Prioritize Patching: Immediately update all vulnerable BIG-IP instances to verified fixed versions: 15.1.10.8, 16.1.6.1, 17.1.3, or 17.5.1.3.
- Conduct Forensic Audits: Review system logs for unauthorized use of the REST API (specifically /mgmt/shared/identified-devices/config/device-info) used for system-level reconnaissance.
- Validate System Integrity: Because native integrity tools may be compromised, organizations should consider an “isolate and replace” strategy for highly sensitive deployments rather than patching in place.
- Harden Perimeter Defenses: Restrict management interface access to authorized internal networks only and rotate all administrative credentials.
- Monitor for Web Shells: Audit web-facing directories for anomalous file creation or unexpected outbound connections, which are common post-exploitation indicators.

Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report