Executive Summary
- Challenge: Traditional security systems fail to connect intelligence, asset context, and action, leaving organizations vulnerable to preventable attacks.
- Solution: Dataminr for Cyber Defense integrates foresight, risk quantification, and AI-automated workflows to detect threats early, prioritize risks, and respond effectively.
- Impact: Real-world results include faster response times, reduced false positives, and significant cost savings for organizations across industries.
If you run a security operation at a financial institution, you already know the math doesn’t work. Your team is buried. Your tools generate more alerts than any analyst can reasonably process. Your asset inventory is a mix of crown jewels, legacy systems, and infrastructure nobody wants to own. And somewhere out there—on a dark web forum, in a Telegram channel, on a code repository—someone is already talking about how to get in.
The frustrating part isn’t that attacks happen. It’s that the information to prevent them often exists before they do—scattered across feeds, dashboards, and tools that don’t talk to each other. The window to act is there. Most organizations just can’t see it clearly enough, fast enough, to do anything about it.
That’s the gap this article is about. Not a gap in technology spending—most organizations have plenty of that. A gap in how intelligence, context, and action connect. Or more accurately, how they don’t.
We’re going to walk through a hypothetical attack on a large bank—entirely fictional, but built from patterns we see in real-world incidents every day. It’s designed to show where traditional defenses break down, why damage often comes from systems no one thought to prioritize, and what changes when foresight, focus, and action actually work together.
The Hypothetical Scenario: A Bank, a Click, and a Cascade
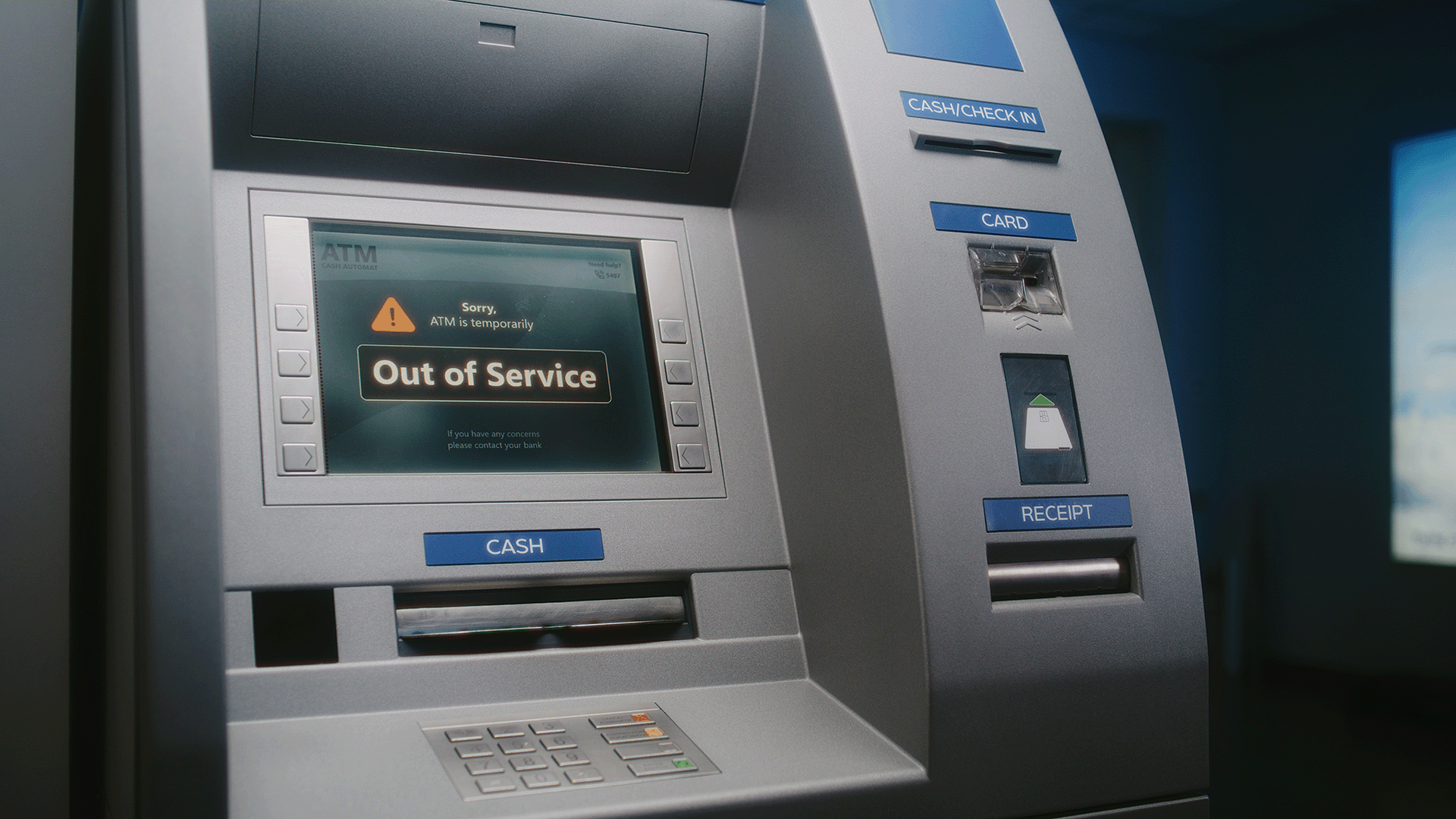
Imagine you’re on the cyber defense team at a large bank. Your environment is sprawling: online banking portals, ATM networks, credit card databases, branch point-of-sale systems, thousands of employee endpoints. Every asset has different value, different controls, different exposure. It’s the kind of environment where something is always on fire, and your job is figuring out which fire actually matters.
Meanwhile, on a dark web forum, Russian threat actors are having a conversation about targeting banks. They aren’t scanning randomly. They’re doing reconnaissance—identifying what looks valuable and what looks easy to exploit. The lowest-hanging fruit.
The breach doesn’t start with a zero-day. It starts with a human moment. An employee who clearly slept through his last security awareness training clicks a phishing link promising free hockey tickets. (It’s always hockey tickets.) That single click installs malware and opens a backdoor. From there, attackers move laterally—probing for weak points, expanding access, looking for the path of least resistance.
Here’s what’s interesting: the core systems—the credit card databases—hold up. They’re well-controlled, heavily layered, and hard to crack. But the branch POS systems? Different story. Less fortified, less monitored, and deeply tied to daily operations. Once ransomware hits those systems, branches go offline. Revenue stops. Customers can’t transact. Executives start calling. Regulators start asking questions. One compromised laptop just became a full-scale operational crisis.
The Real Cost of “Non-Critical” Systems
In our hypothetical scenario, the damage is significant. A ransom payment to regain operational control. Millions in lost revenue from branch closures. Legal exposure from class-action settlements. Crisis communications costs. Months of executive and regulatory scrutiny that pulls leadership away from everything else. Long-term damage to the brand.
But here’s the lesson that gets missed in most post-incident reviews: the attackers never touched the crown jewels. They didn’t need to. They found the systems that were easiest to compromise and most capable of causing operational disruption.
This is where the conventional wisdom—”protect your most critical assets”—falls apart. Criticality isn’t just about data sensitivity. It’s about business impact relative to control posture. A well-defended credit card system, however important, is less of a real-world target than a vulnerable POS system—because the POS system lacks compensating controls and can take the whole operation down. Attackers don’t read your asset criticality matrix. They read your actual defenses.
Why Traditional Defenses Didn’t Catch This
This hypothetical attack wasn’t inevitable. It was the result of three systemic blind spots that show up in security programs everywhere:
Signal overload without relevance
The team had threat feeds—plenty of them. But the volume of alerts and indicators was so high—and so loosely connected to their actual environment—that the signals that mattered were buried. Knowing that “ransomware is increasing” doesn’t help when you can’t tell which ransomware campaigns are targeting your specific technology stack, in your geography, this week.
No asset context for prioritization
Knowing a threat exists is necessary but insufficient. The team couldn’t quickly answer: which of our assets are actually exposed? Which already have compensating controls? Which represent the highest business risk right now? Without that context, prioritization becomes a guessing game driven by CVSS scores and gut instinct—and those two inputs disagree more often than anyone likes to admit.
Slow, manual, disconnected response
Even when the team identified something worth acting on, response required pivoting between tools, stitching together context by hand, and making decisions under pressure with incomplete information. Every minute of that manual process is a minute the attacker is moving laterally. That’s the window where small compromises become large incidents.
These aren’t technology problems. They’re integration problems. Most security teams have the tools. What they don’t have is a system that connects the critical dots—what’s happening externally, what’s true internally, and what it means to the business—fast enough to change outcomes.
How Dataminr for Cyber Defense Changes the Outcome
Dataminr for Cyber Defense is built to close exactly these gaps—not by adding more tools to the stack, but by connecting intelligence, posture, and action into a single continuously operating system.
At its core, the platform helps teams answer three questions that define whether defense is proactive or reactive: What’s coming? What will it cost us? What should we do right now?
These map directly to three capabilities that have to work together to matter: foresight, focus, and action.
Foresight: Know What’s Coming
Answering: “What’s coming?”
Foresight is the ability to understand threats while they’re still forming—before disclosure, before exploitation, before impact. It’s the difference between reading about a breach in the news and knowing about the campaign that caused it days earlier.
Dataminr delivers this through multi-modal intelligence drawn from over a million public sources: dark web forums, social channels, technical signals, infrastructure shifts, geopolitical disruptions, and emerging threat narratives. More than 100 specialized AI models work in parallel to detect, correlate, translate, and contextualize signals across text, image, video, and audio. This isn’t a single general-purpose LLM processing things sequentially—it’s a multi-modal fusion AI architecture that compresses what would be days of analyst work into minutes.
But foresight isn’t about faster alerts. That’s a race to the bottom. It’s about faster understanding. Our Intel Agents don’t just detect a signal and pass it along—they assemble the puzzle pieces autonomously, correlating threat activity with your specific asset inventory, technologies, and exposure. The question shifts from “is this threat real?” to “does this threat matter to us?”
In the bank scenario, foresight would have surfaced dark web discussions about targeting financial institutions days before any phishing campaign launched. It would identify mentions of specific banking technologies and branch POS platforms and detect the ransomware campaign while it was still gaining momentum—automatically correlating those signals with the bank’s actual environment.
Focus: Know What It Costs
Answering: “What will it cost us?”
Visibility alone doesn’t solve the hardest problem in security: deciding where to act first. And traditional severity scores don’t, either. A CVSS 9.8 on a payment-processing cluster with confirmed exploitation trending globally is a fundamentally different problem than a CVSS 9.8 on a dev VM sitting behind four layers of controls. Same score, entirely different priorities.
Our Risk Quantifier capability addresses this by translating technical exposure into financial impact—expressing risk in dollar terms, not abstract severity. It combines external threat signals, internal asset inventories, existing security controls, and historical loss data to calculate expected financial loss. By continuously evaluating compensating controls, operational dependencies, and exploitation trends, it identifies where remediation will produce the greatest business impact.
In the bank scenario, this makes prioritization clear. Branch POS systems carry dramatically higher expected financial loss than the credit card databases—even though those databases appear more critical on paper—because the POS systems lack compensating controls, support daily operations, and sit in a weaker security posture. Security leadership immediately understands: this is the issue worth fixing today, and here’s why, in terms the board can act on.
That shared financial language transforms risk conversations from subjective debates into defensible decisions—across security operations, executive leadership, and the board.
Action: Know What to Do
Answering: “What should we do right now?”
Intelligence delivers real value only when it drives action. And in most security operations, that’s exactly where things stall. Insights sit in dashboards. Analysts rebuild context manually for every investigation. Response quality varies by who’s on shift and how much institutional knowledge they carry in their head.
Dataminr’s Threat Intelligence Platform and Investigation Insights are designed to eliminate that translation gap. The TI Platform transforms intelligence from one-off alerts into structured, reusable intelligence that can be scored, routed, and applied consistently across detections, response, hunting, and reporting. Agentic workflows automatically ingest and enrich indicators, trigger response playbooks, and coordinate across security tools—isolating systems, validating control health, initiating IR cases, and adjusting detections. Human-in-the-loop guardrails ensure oversight, while every action feeds a continuous learning loop that sharpens the system over time.
Investigation Insights brings intelligence directly into the workflow by overlaying relevant context onto logs, alerts, tickets, and scan results—wherever analysts actually work, with federated search across more than 150 integrated systems. Instead of switching tools to investigate, analysts immediately see whether a threat is active, relevant, and worth action.
In the bank scenario, alerts arrive faster than traditional feeds and are automatically evaluated against the bank’s specific environment. If dark web chatter intensifies, if lateral movement indicators appear, if control posture changes internally—the platform detects it and responds with the right next step, aligned to the organization’s priorities.
Rewriting the Bank’s Story
Let’s rewind. Same bank, same threat actors, same employee with questionable judgment about hockey ticket offers. But this time, Dataminr for Cyber Defense is in place.
Foresight kicks in first
Days before the phishing campaign launches, dark web discussions about targeting banks are detected and correlated with the bank’s asset inventory. The system identifies that branch POS systems are mentioned in threat actor forums, and that similar institutions have recently been compromised through these endpoints. The team knows something is developing—and knows it’s relevant to them—before any attack infrastructure is deployed.
Focus quantifies what’s at stake
Instead of treating all critical systems equally, Risk Quantifier calculates that POS systems represent significantly higher expected financial loss than the better-protected databases—because of limited compensating controls, operational dependencies, and high business impact. POS hardening becomes an executive priority backed by defensible numbers, not a request stuck in a patching queue.
Action orchestrates the response
Automated workflows deploy additional monitoring to POS systems. Security awareness alerts about hockey-themed phishing go out to relevant employees. Existing controls are validated. IR playbooks are pre-positioned. When the phishing email arrives, enhanced detections flag it immediately, and the system isolates the compromised endpoint before lateral movement begins.
The ransomware never spreads. The branches never go offline. The damage never materializes. That’s not a technology fantasy. It’s the difference between a security program that reacts to incidents and one that disrupts them before they escalate. And it’s only possible when intelligence, context, and action operate as a connected system—not as separate tools, separate teams, and separate workflows hoping to converge under pressure.
Beyond the Hypothetical: What This Looks Like in Practice
The scenario above is fictional. The outcomes below are not. Dataminr for Cyber Defense detected a critical Fortinet zero-day vulnerability 38 days before CISA added it to their Known Exploited Vulnerabilities catalog. Organizations using the platform had over five weeks to harden defenses while the rest of the industry was still waiting to learn about the threat.
Across our customer base, the pattern is consistent:
- A Forbes 2000 healthcare system reduced incident response time from seven hours to 37 minutes—and is still improving.
- A Fortune 500 retailer compressed investigation tasks from two to five minutes each to two seconds.
- A Fortune 300 financial institution narrowed 200 million monthly SIEM events down to 12 actionable incidents.
- A Fortune 200 healthcare organization built 60+ workflow automations, saving $1.3 million per year in labor costs.
- 74% of surveyed customers reported false positive reductions of 25% or greater. 42% reported reductions of 50% or more.
These aren’t benchmarks from controlled environments. They’re production results from security teams dealing with the same sprawl, the same alert fatigue, and the same resource constraints you are.
The hypothetical bank didn’t have to lose millions. And neither does your organization. The intelligence to prevent most incidents already exists—the question is whether your security program can find it, understand it, and act on it fast enough to matter. That’s the problem Dataminr for Cyber Defense was built to solve.

Dataminr for Cyber Defense
Transform intelligence into a preemptive cyber advantage from first signal to risk-prioritized action.
Learn More