Security teams missed 57% of cyber attacks in 2024—they learned about the compromise from an external entity, a hacker, or a threat researcher, not their own tools, according to the Mandiant 2025 M-Trends Report.
These weren’t underfunded teams. These were organizations running 83 tools from 29 vendors on average, according to the IBM Institute for Business Value. They had the pieces. What they couldn’t answer—quickly, confidently, and continuously—were three questions:
- What’s coming?
- What does it cost us?
- What do we do next?
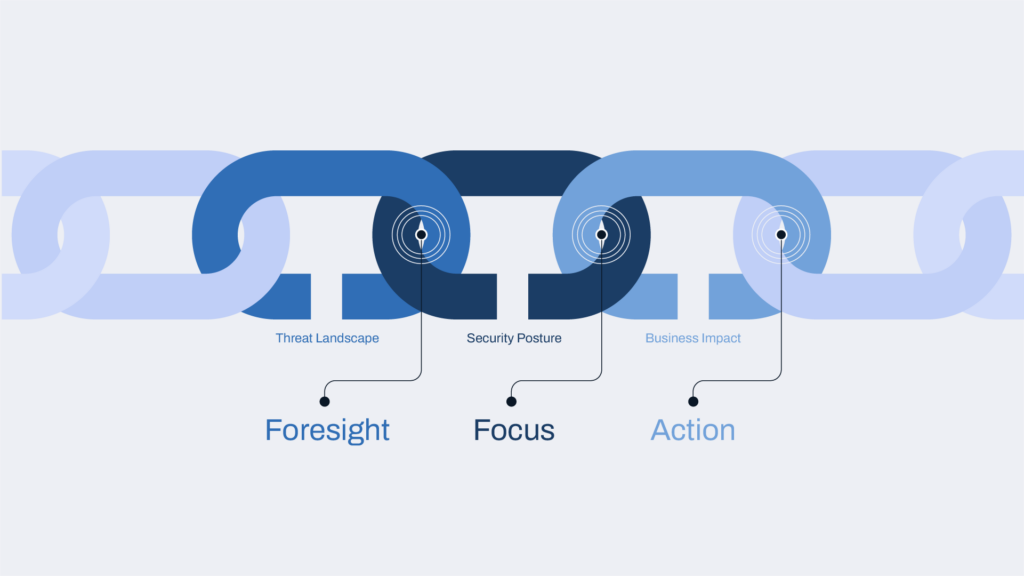
Those questions live in the gaps between tools—between the threat landscape, security posture, and business impact. And those gaps are where attacks succeed.
Download ebook: Mending the Broken Cyber Defense Chain
The Vision Behind the Acquisition—Now Realized
When Dataminr acquired ThreatConnect, the thesis was clear: unite the world’s fastest external threat detection engine with the industry’s most mature intelligence operations and risk quantification platform. Not to bundle products, but to build a preemptive threat and exposure intelligence solution suite that assembles and operationalizes real-time, client-tailored intelligence from first signal to risk-prioritized action.
Organizations already relied on Dataminr for real-time threat intelligence for the earliest signals of emerging threats, and we realized there was even more we could answer for our customers. Today, Dataminr for Cyber Defense delivers this expanded vision: foresight into what’s coming, focus on what it costs, and the action to do something about it—before impact.
“We acquired ThreatConnect with a clear vision: to unite external threat signals with internal telemetry and provide organizations with clarity on what threats are impacting their business so they can act with speed and precision,” said Ted Bailey, CEO and Founder of Dataminr. “The old model of static feeds is obsolete. If you aren’t linking the threat directly to your specific posture and real-time financial impact, you are operating blindly.”
Three Questions Most Security Programs Can’t Answer Fast Enough
“What’s coming?”
82% of security professionals worry they’re missing real threats because of data and alert overload, according to the Forrester 2025 Threat Intelligence Benchmark. Feeds surface threats after disclosure. By the time a picture forms, the window to act has narrowed—or closed.
“What does it cost us?”
While 88% of executives agree that measuring cyber risk is key to prioritizing investments, and 87% say it helps allocate resources effectively, only 15% of organizations are actually doing it at a significant level, according to PwC 2025 Global Digital Trust Insights. Control effectiveness, if measured at all, is not measured with real and specific threats in mind as informed by threat intelligence. Risk conversations with leadership are subjective, episodic, and disconnected from anything the business can act on.
“What do we do next?”
76% of organizations can’t match the speed of AI-powered attacks, according to the CrowdStrike 2025 State of Ransomware Survey. Intelligence stalls at dashboards. Analysts rebuild context manually. Response varies by individual judgment, not operationalized intelligence.
Three Solutions That Deliver Cyber Defense Foresight, Focus, and Action
Dataminr for Cyber Defense is designed to provide the answers to those hard questions with offerings that empower all parts of your security infrastructure with the intelligence and context they need.
Client-Tailored Threat Intelligence

78% of security professionals now spend over 10 minutes investigating each alert (Critical Start). Most of that time goes to one question: does this matter to us?
Client-Tailored Threat Intelligence answers it automatically. Our AI fuses global external signals with your internal context—exposed assets, alert activity, vulnerabilities, control gaps—and delivers intelligence directly into your SIEM, EDR, ticketing system, and browser. No new portals. No tab-switching.
The difference: Intel Agents don’t just detect threats early—they tell analysts whether it matters to your specific environment, which assets are affected, and how the situation is likely to evolve. If your organization has exposed VPN appliances matching a vulnerable configuration, that gets elevated. If you don’t, it gets suppressed.
Examples: A Fortune 500 retailer: investigation tasks reduced from 2-5 minutes to 2 seconds. A major social media platform: time-to-close improved 300% in the first month. A Fortune 500 manufacturer: “saved ‘humans’ worth of time.”
Who this is for: SOC analysts, incident responders, CTI analysts, and threat hunters who need earlier awareness, faster triage, and immediate relevance—without manual enrichment.
What it answers: “This is happening—and it matters to us right now.”
Agentic TI Ops
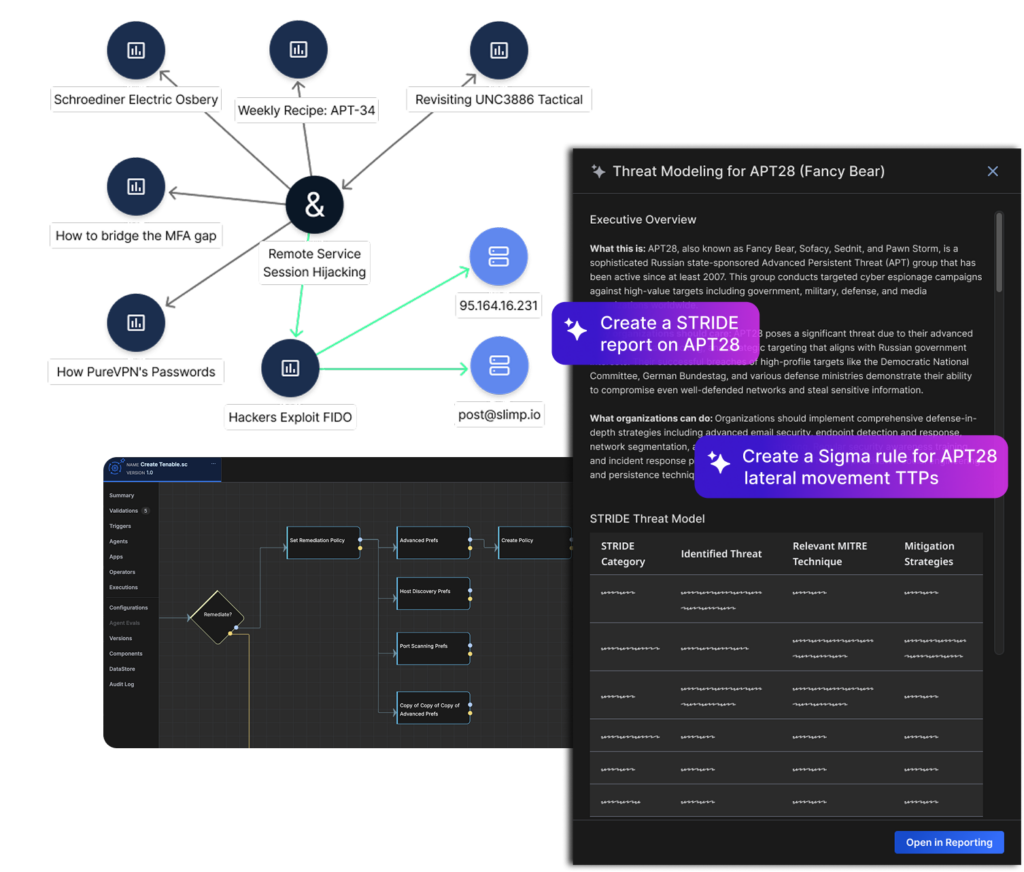
Producing finished, structured, reusable intelligence from early signals is still manual in most organizations. Enrichment, correlation, scoring, routing—it eats analyst hours. And most intelligence never makes it into detections or responses consistently.
Agentic TI Ops adds a full intelligence operations layer. Intel Agents assemble evolving intelligence as threats develop. Our Agentic Threat Intelligence Platform structures it into reusable records, scores it, routes it, and distributes it across detection engineering, incident response, hunting, and reporting—automatically.
Examples: A Fortune 300 financial institution: 200 million SIEM events/month narrowed to 12 actionable incidents. A Fortune 200 healthcare org: 60+ automations and $1.3M/year saved. A Forbes 2000 healthcare system: incident response time reduced from 7 hours to 37 minutes.
Who this is for: Threat intelligence managers who need to produce and operationalize intelligence at scale—not just consume feeds. Detection engineers and incident responders who need high-confidence, finished intelligence without guesswork.
What it answers: “This has happened before, here’s how it evolves, and here’s what we do next — every time.”
Predictive Threat Exposure Management
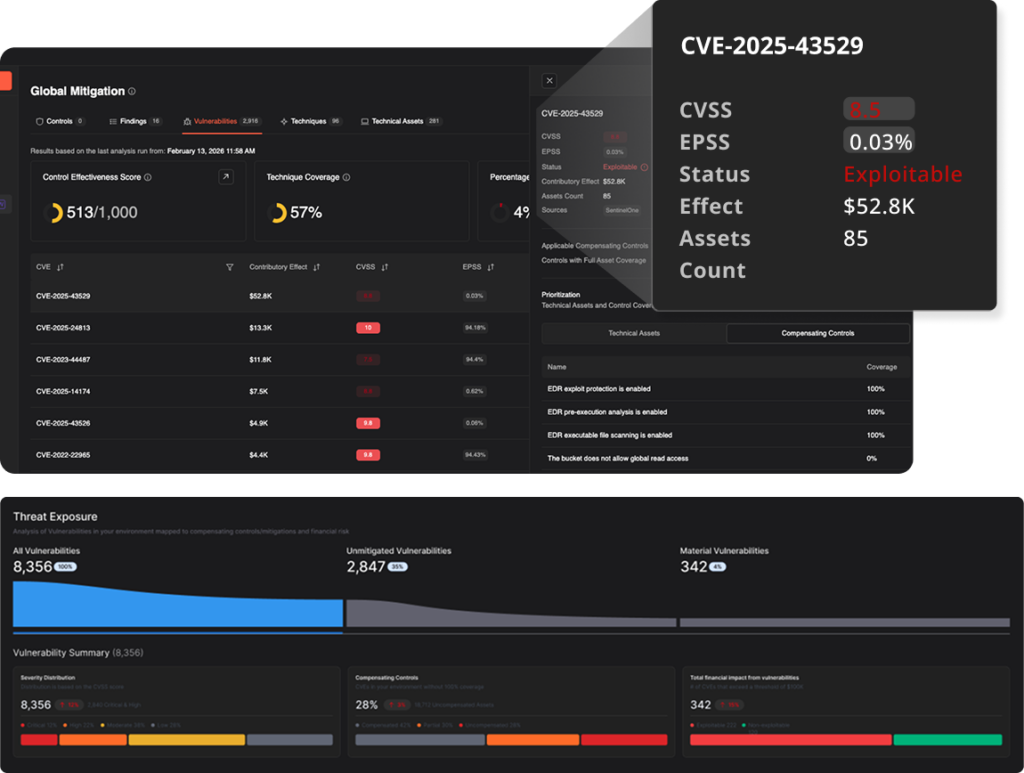
Most Continuous Threat Exposure Management (CTEM) initiatives stall because control effectiveness is assumed, not measured. Only quarterly snapshots get reported, controls drift, and the gap between “what we think is protected” and “what’s actually protected” widens silently.
Predictive Threat Exposure Management continuously validates control performance using live telemetry, then translates threat exposure into dollar-denominated financial risk. Not CVSS scores. Not heatmaps. Dollars. When remediation actions are taken, the system shows measurable reduction in expected loss—in near real time.
Examples: A Fortune Global 500 manufacturer: “Our business leaders were unknowingly accepting massive cyber risk because we couldn’t communicate it in financial terms.” A Fortune 500 automotive distributor: “stopped relying on CVE scores and started understanding which ones matter in dollars and cents.” Another Fortune Global 500 manufacturer: 85% annualized savings across dozens of OT risk reduction projects.
Who this is for: CISOs justifying investments with evidence. Risk leaders replacing point-in-time assessments with continuous validation. Vulnerability management prioritizes by probable financial loss.
What it answers: “This matters, here’s what it costs, and here’s which actions reduce risk the most.”
What Makes AI-Native Cyber Defense Different?
Here’s the thing about most “AI-powered” security products: if you took the AI off, the product would still work. The AI is a layer—bolted on to classify text, generate summaries, speed up searches.
With Dataminr for Cyber Defense, the agentic AI is the product. Remove it, and there’s nothing left to run. We are AI-native. Our Intel Agents are powered by more than 55 proprietary tuned LLMs and over 12 years of event archive. They continuously detect, correlate, and assemble intelligence from over 1 million public data sources across text, images, video, and audio in 150 languages—processing over 43 terabytes daily.
When exploit chatter emerges on a dark web forum on Monday, Intel Agents are assembling a complete intelligence picture moments later—correlating actors, TTPs, infrastructure, IOCs, and CVEs while the threat is still forming. By Wednesday, when competitor feeds surface a generic alert with a CVE number and severity score, our customers have already patched exposed systems—hours, if not days, before.
In October 2025, our AI detected an actively exploited Fortinet zero-day 38 days before CISA added it to the KEV catalog. We benchmark ourselves on beating the KEV. We detected early warnings of the PowerSchool breach more than six months before it became public (Dataminr 2026 Cyber Threat Landscape Report).
Because the AI is the product, the system compounds over time. Every analyst action feeds back into your private instance’s agents. Intelligence gets sharper. Prioritization gets more confident. Customer results confirm it: 97% report improved effectiveness in tools like SIEMs, SOARs, and EDRs. 67% report cutting Mean Time to Respond by more than half.
What Happens When Threat Intelligence, Operations, and Risk Work as One System?
Each solution delivers standalone value. Combined, outcomes compound.
Each capability contributes unique data to the context provided by Intel Agents—early external signals, internal operational context, structured intelligence records, and financial risk models. The more capabilities active, the smarter the AI gets. This isn’t risk layered on top of intelligence. It’s intelligence, operations, and risk operating as a single, continuously learning system that answers: What’s coming, what does it cost us, and which actions reduce risk the most?
Dataminr for Cyber Defense also operationalizes both of Gartner’s emerging frameworks—Unified Cyber Risk Intelligence (UCRI) and Continuous Threat Exposure Management (CTEM)—end-to-end, from first signal to executable risk reduction.
The Bottom Line
Every 10 days a data breach goes undetected increases expected financial loss by $2,209,100 (aggregated historical cyber loss data, modeled using our Predictive Threat Exposure Management solution).
Dataminr for Cyber Defense answers the three questions that matter: What’s coming? What does it cost? What do we do next?—with agentic AI that assembles, tailors, and operationalizes intelligence continuously, from first signal to risk-prioritized action.
We’re showing it live at RSA Conference 2026, Booth #4419. Come see what preemptive cyber defense actually looks like. For the deeper story, download our ebook: Mending the Broken Cyber Defense Chain.

Dataminr for Cyber Defense
Transform intelligence into a preemptive cyber advantage from first signal to risk-prioritized action.
Learn More