Key Takeaways
- Confirmed Operational Impact: Vyncs confirmed a service disruption caused by an “unprecedented amount of network-level threat,” took systems offline as a precautionary measure, and has begun phased restoration — reporting 99% of servers operational with residual account-specific issues being addressed by customer support.
- Significant but Partially Unverified Claims: Ababil of Minab claims to have exfiltrated over 4 TB of data, wiped 250 TB of data, transmitted over one million notifications via the Vyncs application, and defaced the Vyncs website. While operational disruption is confirmed, the full scope of data impact has not been independently verified.
- Psychological Operations as a Core Tactic: Iranian-linked hacktivist groups, including Ababil of Minab, consistently employ psychological operations as a primary tactic — deliberately overstating technical impact to maximize reputational damage, erode public trust, and force disproportionate defensive responses. This is evident across both the LA Metro and Vyncs incidents.
- Early Detection Is Critical: Dataminr identified signals related to this incident in real time, enabling defenders to assess, respond, and communicate before claims escalated further — a decisive advantage in a threat environment where the window between a hacktivist post and widespread reputational damage is measured in hours.
Incident Overview
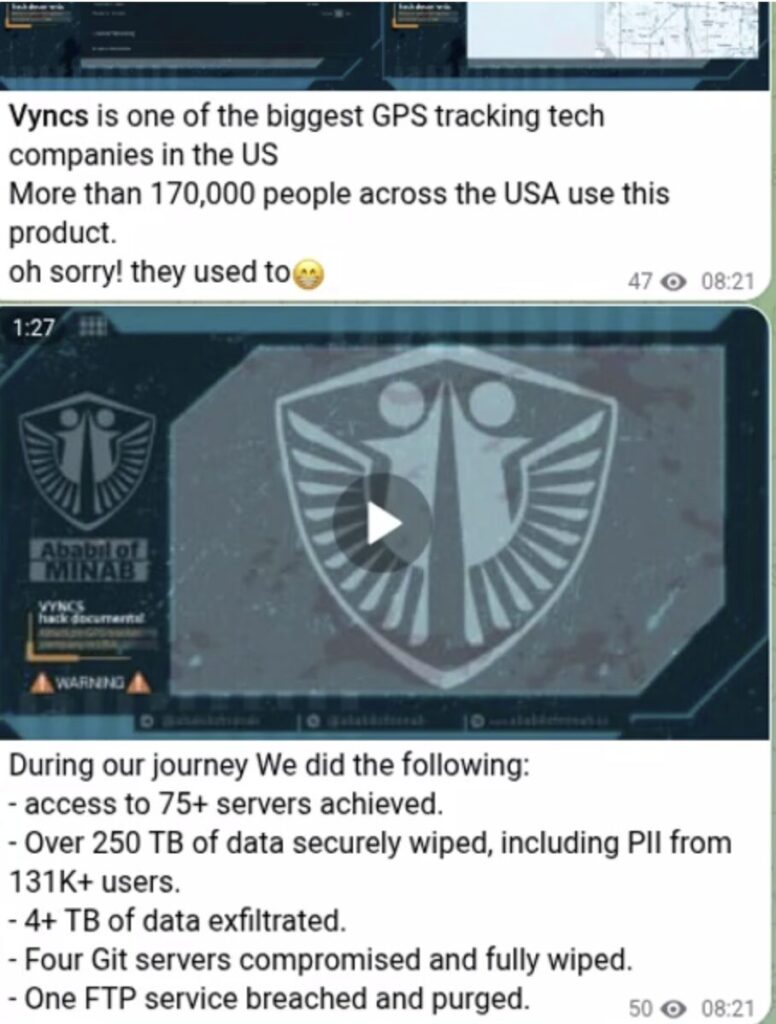
Ababil of Minab, a pro-Iranian hacktivist group, posted claims via their Telegram channel alleging a successful cyberattack against Vyncs, a consumer and commercial GPS tracking platform used for vehicle monitoring and fleet management. The group claims to have exfiltrated over 4 TB of data, destroyed 250 TB of data, transmitted over one million messages through the Vyncs application following the alleged platform compromise, and subsequently defaced the Vyncs website.
Vyncs confirmed the incident, attributing the disruption to an “unprecedented amount of network-level threat” and proactively taking its systems offline. The company has since reported that restoration is proceeding as planned, with 99% of servers back online and customer support actively addressing residual account-specific issues. As of the date of this brief, the Vyncs website remains non-functional and redirects visitors to the company’s Amazon product page — consistent with the group’s defacement claim.
This incident follows other recent activity from Ababil of Minab. In a prior attack on LA Metro, the group claimed unauthorized access to transit systems, but no data access or deletion was confirmed. The deliberate inflation of impact claims is not incidental — it is a defining characteristic of Iranian-linked hacktivist operations broadly. Groups operating within Iran’s cyber influence ecosystem routinely use psychological operations to achieve strategic objectives that technical capability alone cannot deliver; undermining confidence in critical services, generating media coverage disproportionate to actual damage, and forcing organizations into costly and disruptive defensive postures. The “one million notification” and “250 TB destruction” figures have not been independently corroborated through publicly available information or social media evidence and should be treated with appropriate scrutiny.
That said, the confirmed disruption to Vyncs operations is real and significant. The ability to quickly identify, verify, and contextualize these claims is itself a defensive capability. What Dataminr provides — and what defenders need more than ever — is the ability to detect signals before they become crises. In a threat environment where hacktivist groups emerge and escalate rapidly, where a single Telegram post can generate outsized reputational damage regardless of technical reality, the organizations that survive are the ones with real-time intelligence that cuts through the noise.
Dataminr Alert
Technical Details
- Claimed Attack Scope: 4 TB of data exfiltrated; 250 TB of data wiped; mass notification abuse via the Vyncs application; website defacement.
- Confirmed Impact: Network-level disruption significant enough to prompt voluntary system shutdown; website offline and redirecting to Amazon storefront.
- Notification Abuse: The claim of over one million application notifications suggests either unauthorized API access, compromise of a push notification service integrated with the platform, or abuse of an authenticated session with elevated messaging privileges.
Ababil of Minab published a video on their Telegram board, with the intent to demonstrate proof of impact. The below are screenshots of key moments of this video, with analysis on what is happening:
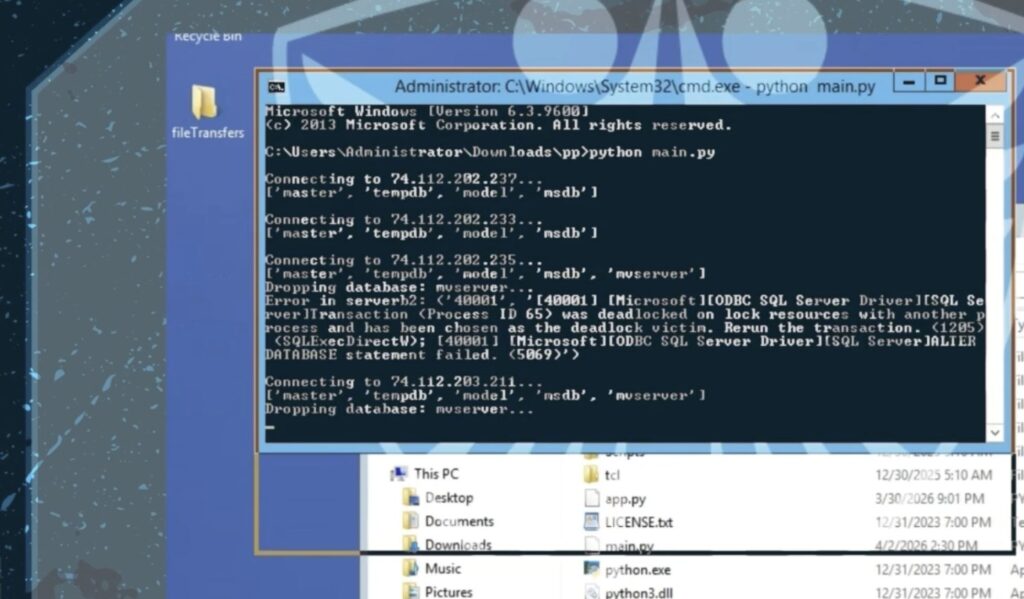
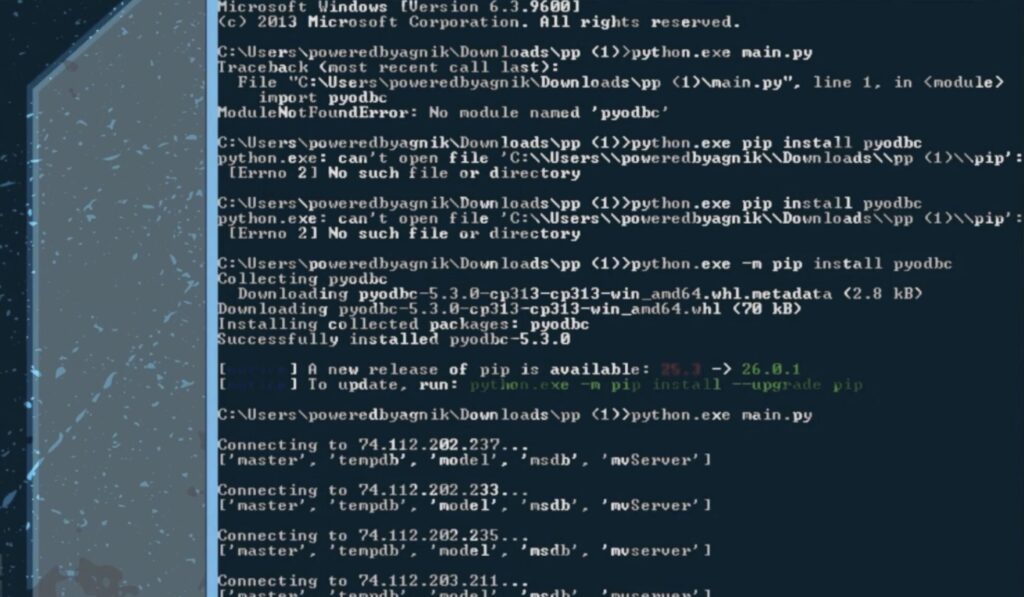
Screenshots 1 & 2 (Python script execution and database enumeration) A Python script (main.py) is being run from a Downloads directory, using the pyodbc library to connect to multiple SQL Server instances at IP addresses in the 74.112.202.x–203.x range. The script enumerates databases on each server, revealing the presence of mvServer (myVyncs) alongside standard system databases. In Screenshot 1, the script is actively issuing DROP DATABASE mvserver commands — one attempt hits a deadlock error, suggesting the database was live and in use at the time of the attack.
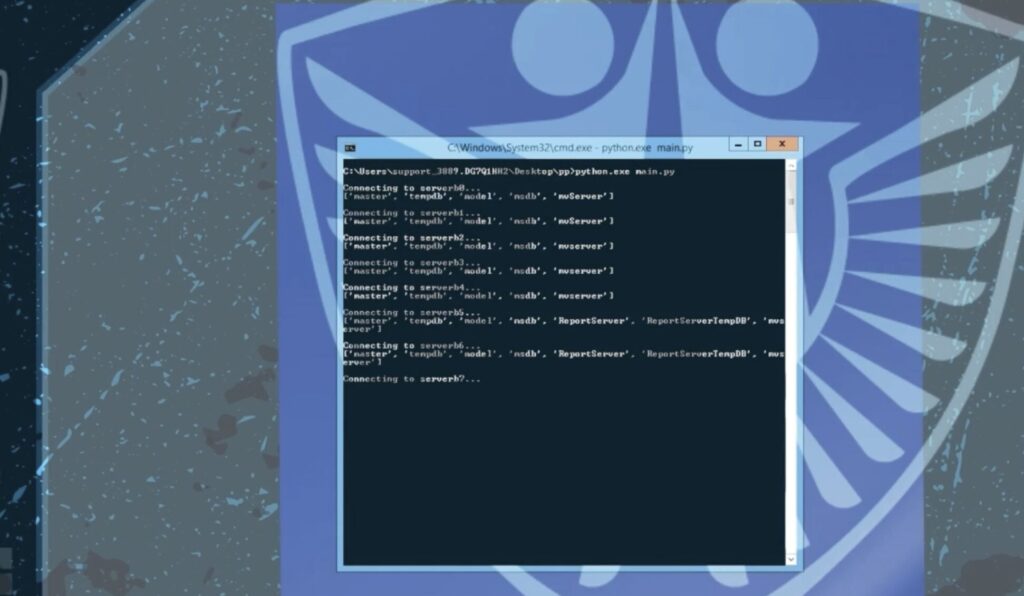
Screenshot 3 (Multiple server access) This shows the same script connecting sequentially to at least eight SQL Server instances labeled serverb0 through serverb7, all of which contain the mvServer database. Two servers also expose ReportServer and ReportServerTempDB databases, indicating SQL Server Reporting Services is deployed and accessible. This demonstrates broad lateral access across what appears to be a multi-server Vyncs database environment.
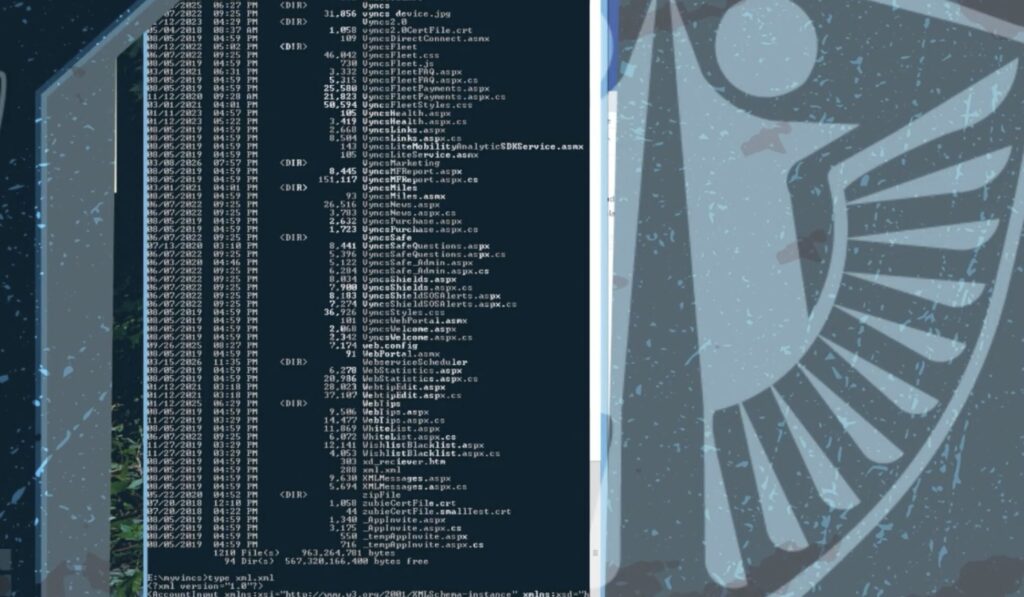
Screenshot 4 (Web application file system access) The actor has navigated the file system of what appears to be the Vyncs application server at E:\myvyncs, revealing over 1,200 files comprising the full ASP.NET web application — including source code files for Vyncs product features (Fleet, Safe, Shields, Miles), SSL certificates, and a web.config. They then read the contents of xml.xml, which contains an AccountInput XML structure, suggesting exposure of account-related data. This level of access goes beyond the database layer and indicates the actor has direct server or RDP-level access to the application host itself.
Threat Actor & Motivation
Ababil of Minab is a pro-Iranian hacktivist collective with a demonstrated focus on U.S.-linked organizations spanning infrastructure, commerce, and technology. Their operational model blends targeted technical intrusion with deliberate psychological operations — a tactic that is not unique to this group but is a defining characteristic of the broader Iranian hacktivist ecosystem.
Across both the LA Metro and Vyncs incidents, Ababil of Minab follows this well-established playbook: gain access, assert outsized impact, amplify via Telegram, and force targets into a defensive posture before an accurate counter-narrative can be established. Organizations should be prepared not only to remediate technically, but to respond informationally — with speed, accuracy, and a clear internal understanding of what has and has not been confirmed.
Immediate Actions & Recommendations
- Audit Application-Layer and API Access: Organizations using Vyncs for fleet or vehicle management should immediately audit API keys, connected accounts, and active sessions for signs of unauthorized access. Rotate all credentials where compromise is suspected.
- Monitor for Follow-On Phishing: Brand disruption of a customer-facing platform creates immediate conditions for phishing campaigns impersonating Vyncs customer support. Warn employees and end users not to respond to unsolicited communications claiming to be from Vyncs during the restoration period.
- Assess Third-Party Dependencies: Enterprise and fleet customers should evaluate operational exposure and activate contingency tracking protocols while Vyncs completes its restoration.
- Establish a Real-Time Counter-Narrative Posture: Given that psychological operations are a core TTP of Iranian hacktivist groups, security communications teams must treat rapid claim verification as an operational priority — not an afterthought. Monitor hacktivist Telegram channels and dark web forums for claims targeting their organization or sector. Dataminr’s real-time detection directly enables the speed required to get ahead of these narratives before they solidify in public discourse.
- Implement Phishing-Resistant MFA: Ensure all administrative, API, and platform access uses phishing-resistant multi-factor authentication (e.g., FIDO2 hardware keys) to reduce the risk of credential-based initial access consistent with this group’s known TTPs.
- Harden Network Perimeter Against Volumetric Threats: Given the confirmed network-level attack vector, organizations should review DDoS mitigation controls, rate limiting on public-facing APIs, and traffic anomaly detection thresholds.
Read the 2026 Cyber Threat Landscape Report
In a time of increasing cyber threats and AI-driven attacks, security teams need actionable insights to drive a preemptive cyberdefense strategy. This report analyzes global risks and offers the intelligence needed for a proactive cybersecurity strategy.
Download Report