In February 2024, a ransomware attack against U.S. company Change Healthcare significantly disrupted patient care, including clinical decision support, eligibility verifications and pharmacy needs. It also rendered care providers and care facilities unable to receive payments, send bills and offer services.
In the UK, a ransomware attack on Synnovis, a critical pathology services provider to the country’s National Health Service (NHS) hospitals, led to hundreds of operations and appointments being cancelled in June 2024. It also severely impacted the delivery of vital healthcare services, such as blood transfusions and test results, for several months.
These are just two in a series of cyber crimes aimed at healthcare providers in the past few years, demonstrating the rapidly expanding risk landscape that organizations—both in the public and private sector—are facing today.
As cross-domain threats have rapidly evolved in type, impact and scope, Dataminr recommends organizations view them on a threat spectrum.
According to the U.S. Cybersecurity and Infrastructure Security Agency (CISA), cross-domain threats are defined as those that have ramifications in both the digital and physical domains. While the threat can originate from either domain, cross-domain threats often begin with a cyber threat vector, such as a ransomware attack, and then spill over into the physical world.
When threats in the digital and physical domains converge, the consequences are often real and significant as evidenced by the attacks on Change Healthcare and Synnovis.
Other times, cross-domain threats lead to major business and public infrastructure disruption. For example, when U.S. cybersecurity vendor CrowdStrike experienced a global IT outage in July 2024—causing millions of Windows systems to crash—operations of hospitals, airports, payment systems and personal computers worldwide came to a halt.
Expanding Risk Landscape vs. Security Convergence
Although related, there is a distinct difference between the expanding risk landscape and security convergence.
Expanding risk landscape: Increasing risk across all domains of an organization presented by high velocity, AI-powered threats, information overload, and organizational silos.
Security convergence: When an organization’s cyber and physical security operations are combined into a single, unified function.
The cross-domain threat spectrum
As cross-domain threats have rapidly evolved in type, impact and scope within the expanding risk landscape, Dataminr recommends organizations view them on a threat spectrum.
On one end of the spectrum are kinetic events that have an impact on the cyber infrastructure of organizations and industries. This includes physical threats to information technology (IT) and operational technology (OT) infrastructure, network and power outages, natural disasters and more. These events are not inherently cyber-related but can have significant impact on cyber infrastructure.
On the opposite end are cyber events that impact the physical world, such as cyber attacks against critical infrastructure that have varied ramifications—ranging from inconveniences for consumers to supply chain disruptions and third-party and vendor risk.
Consider the serious ripple effects of a ransomware attack against a manufacturing plant. For example, as semiconductors (or chips) are vital to the operation of cars and consumer electronics, a cyber attack against a semiconductor manufacturer is likely to significantly disrupt the automotive and consumer electronics industries.
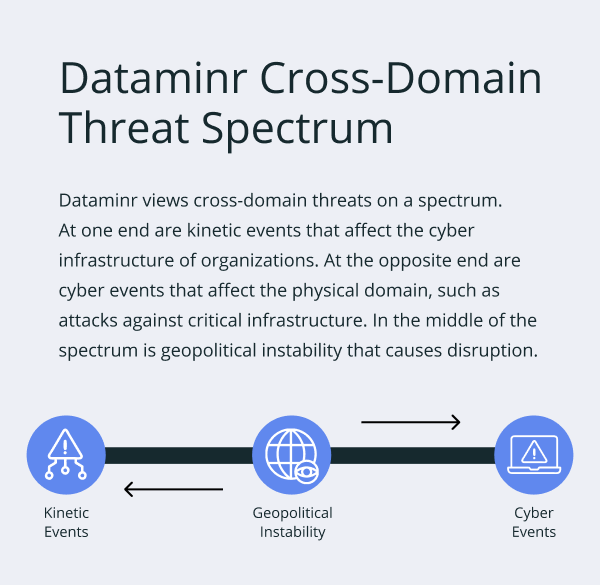
In the middle of the cross-domain risk spectrum lies geopolitical risk, which has increasingly become a major concern for organizations worldwide. According to a recent World Economic Forum report, nearly 60% of organizations say that geopolitical complications have shaped their cybersecurity strategy. One in three CEOs see cyber espionage and intellectual property (IP) theft as their top threat.
A few notable examples of cross-domain attack as a result of geopolitical tensions include:
- The U.S. government alleged that Salt Typhoon, a China-linked hacking group, was behind a massive data breach involving several major U.S. telecommunications companies as part of a wide-ranging espionage and intelligence collection campaign
- Pro-Ukraine hacking group, sudo rm-RF, targeted the Russia’s top state media provider and court websites, disrupting Russian’s ability to file lawsuits or view court hearing schedules
- The U.S. government pressed charges against three Iranian hackers for targeting and compromising email accounts of President Trump’s election campaign officials
The evolution of expanding risk
The expanding risk landscape is due to both the prevalence of IoT and OT devices, as well as the advancement of the tactics and procedures employed by threat actors. Our society, governments and businesses across all industries rely on these devices and the cloud much more than they did five or 10 years ago. This has created a significantly larger attack surface with new and expanding vulnerabilities and risks that have real world consequences. Furthermore, teams face a rapidly-increasing volume of information to analyze. And siloed organizational structures make it challenging to share and receive information with cross-domain counterparts.
And the stakes are high. According to the U.S. government, “the consequences of unintentional faults or malicious attacks [on cyber-physical systems (CPS) and IoT devices] could have severe impact on human lives and the environment.”
The pace and level of this dependence are only accelerating, making the attack surface that threat actors can manipulate and exploit ever-growing. Take for instance ransomware attacks. They surged by 74% in 2023 from the year before, with healthcare, financial services and industrial operations as the most commonly targeted industries by threat actors.
Continued rise in healthcare ransomware attacks
Ransomware attacks against healthcare organizations continued to increase in 2024, with 67% saying they experienced an attack in the past 12 months—compared to 60% in the previous year.
Source: The HIPAA Journal
As such, organizations in these industries tend to be much more forward-thinking and innovative in how they manage cross-domain threats to ensure business resilience and prevent financial, operational and reputational damages.
However, it’s important to remember that cross-domain threats are not limited to cyber-physical systems. As mentioned earlier, physical events can greatly impact digital infrastructure. As extreme weather events—such as hurricanes, heatwaves and winter storms—occur more frequently, data centers and other critical infrastructure become more vulnerable. Add to that the rise in cyber crimes and ongoing geopolitical tensions, and cross-domain threats become much more prevalent. Identifying and defending against credible threats in this environment is more challenging than ever.
Global response to the expanding risk landscape
Recognizing the surge in expanding risk and the urgent need to have a more holistic, innovative approach to respond to those threats, a number of regulators and governments have developed new regulations and initiatives.
In the U.S., CISA has published cyber-physical convergence scenarios documents to help organizations prepare for these risks. In September 2024, the U.S. Networking and Information Technology Research and Development (NITRD) National Coordination Office put out a request for public input for the creation of a National Plan for Cyber-Physical Systems Resilience Research. This initiative aims to shape a whole-of-government research and development (R&D) plan related to cyber-physical resilience across local, regional and national cyber-physical systems.
In December 2022, the European Commission issued the NIS2 Directive, which “establishes a unified legal framework to uphold cybersecurity in 18 critical sectors across the EU.” This directive requires the EU Member States to implement a national cybersecurity strategy to bolster their cyber defense. The 18 sectors covered in NIS2 include:
- Digital infrastructure such as public electronic communications networks and services
- Physical infrastructure like manufacturing of critical products and postal and courier services
More businesses are also realizing the impacts of cross-domain threats and how they can ultimately affect operational and business resilience. In response, they have taken steps to ensure tighter alignment between their cyber and physical security teams, which allows for a more holistic view of cyber-physical systems and risks.
Some companies have done this by creating a formal security operations center (SOC) that merges cyber and physical security teams into a single, unified function. Others forgo combining the teams and instead focus on ensuring effective collaboration and communication between the two, including following best practices like sharing incident response playbooks and conducting tabletop exercises together.
According to CISA, those that establish a formal means for the two security functions to work together will be more resilient against and better prepared to identify, prevent, mitigate and respond to cross-domain threats.
Prepare for and protect against cross-domain threats
Staying up to date on new and emerging risks is a constant challenge for any organization, especially if the business relies on third-party vendors—such as suppliers, manufacturers, distributors and more. Each third-party partner is a potential attack vector.
If a vendor has a vulnerable attack surface, it could be used to gain access to the various organizations for which it provides services. Those organizations are then more at risk to cyber threats such as a data breach. The more vendors a company uses, the larger its attack surface and the more potential vulnerabilities it can have.
To gain the earliest and clearest line of sight into such cross-domain threats, security operations on both the cyber and physical sides of the house should ensure they have access to real-time alerting tools and technology. Organizations, particularly those that have established modes of collaboration among all security teams, are then able to quickly respond to and effectively mitigate threats no matter the origin or type of impact.
Download eBook: The Importance of AI and Public Data to Address Third-Party Risk
There are two key ways organizations better protect themselves against cross-domain threats.
No.1: Invest in the right tools and technology
Real-time alerting solutions are key to detecting and responding to threats as soon as possible. Dataminr Pulse for Cyber Risk, for example, surfaces cross-domain threats and risks as soon as they arise and provides updates in real time and as they evolve.
More specifically, Dataminr’s ReGenAI—a new form of generative AI—distills multidimensional events into concise event briefs, then automatically updates and regenerates those briefs as events unfold. This allows security leaders and teams to gain rapid understanding of an incident, so they can quickly determine the impacts on their organization and protect their employees and assets more effectively.
Take for instance when PowerSchool—a student information system used by educational institutions worldwide—experienced one of the largest breaches to school districts across North America. The threat actor gained access to personal and confidential data of 62.4 million students and 9.5 million teachers. In the wrong hands, this data could be dangerous, costly and even life-threatening.
Six months prior to the breach, Dataminr Pulse alerted customers six times that PowerSchool credentials were on sale on illicit sites. Dataminr also uncovered a track record of compromised credentials for sale, with dozens of mentions of PowerSchool on the dark web since 2023. These early warnings allowed organizations to:
- Proactively engage with PowerSchool
- Ensure appropriate mitigation measures were taken
- Require their PowerSchool users to reset entity login credentials
- Initiate a thorough risk assessment to evaluate their exposure to PowerSchool and whether the rise in dark web activity warranted further action
Businesses also need tools that enable them to assess their attack surface (e.g., network infrastructure), practice cyber hygiene and develop robust response playbooks.
No. 2: Acquire industry and cross-sector insights
This is vital. Security teams should communicate with their industry peers to learn how they are managing cross-domain threats. This includes asking: How are phishing campaigns and/or ransomware groups targeting your organization? What vulnerabilities are consistent across your industry, whether that be an industrial control system (ICS), a customer relationship management (CRM) platform or a specific piece of software that’s ubiquitous in your sector?
In addition, tackling cross-domain threats calls for improved cooperation across various sectors. Governments, corporations and security experts must join forces, pooling resources and exchanging information to create a robust defense against cyber criminals and state-sponsored threats.
The expanding risk landscape is not a new concept and it will only become more prevalent due to the proliferation of OT and IoT devices. Organizations should also keep in mind that cross-domain threats exist in a threat spectrum and the attack surface is ever-growing. Businesses that understand this and take swift action to strengthen their resilience against expanding risk will be in a much better position to respond to and recover from a threat when—not if—it occurs.
Dataminr Pulse for Cyber Risk
See how organizations like yours use Dataminr Pulse for Cyber Risk to strengthen resilience against cross-domain risks.
Learn MoreThis article has been updated from the original, published on May 19, 2023, to reflect new events, conditions or research.
Dataminr Guide to Cyber-physical Security Convergence
Gain a deeper understanding of cyber-physical threats and learn best practices for mitigating them.
Download Guide