Today’s organizations face many multidimensional challenges, particularly when it comes to cybersecurity and digital risk management. In fact, cyber incidents sat atop the Allianz Risk Barometer’s ranking of the most important global business risks in 2022, and likely will continue to reign supreme in 2023.
Security and risk managers know that understanding the cyber threat landscape is essential to organizational resilience. However, what many might not realize is that there’s a massive, untapped data source at their disposal: the dark web.
Most believe the dark and deep web to be hotbeds of malware, cyber criminals and illegal activity. But with the right tools, you can use the dark web to detect and extract valuable data—that which provides the actionable insights needed to protect your organization against cyber crime.
But how can organizations leverage dark web data to their advantage? How can they access it in the first place? Let’s take a closer look and find out.
The evolution and power of the dark web
The dark web is rooted in secrecy. Developed originally as a tool for the U.S. Navy, it has evolved into an anonymous hub used as a repository for criminal activity, stolen data and compromised credentials.
It’s not hard to imagine the cybersecurity implications in a business context. Hackers often target organizations due to their abundance of sensitive and personal information. There are several significant cyber threats that exist on, or as a result of, the dark web:
- Targeted cyber attacks: Because it acts as a clearinghouse for malware and stolen credentials, cyber criminals often browse the dark web for underground marketplaces where they can hire hackers to launch a sophisticated attack against a unique target (e.g., a particular organization, location or even a specific employee).
- Insider data leaks: Malicious insiders, such as a disgruntled employee or other internal threat actor, leak or sell stolen data which easily makes its way to a dark web marketplace. While many data leaks are accidental, the end result is often the same, making the organization more vulnerable and exposed.
- Software vulnerabilities: The dark web is home to many hacker forums, where bad actors exchange intel about critical cybersecurity vulnerabilities and how to exploit them before they’re patched. For example, Log4Shell was a zero-day vulnerability in Apache Tomcat—one of the most widely used software solutions in the world. By the time it was patched in December 2021, it had already impacted roughly 93% of all enterprise cloud environments, cementing it as one of the most severe vulnerabilities ever discovered.
- Exposed credentials: Cyber criminals frequently exchange stolen credentials acquired via a data breach or ransomware attack where they are sold at a lucrative price. Oftentimes “PR-styled” pages are used to attract buyers. They contain victim lists, data samples and the data of ransomed organizations that failed to pay.
Why leverage dark web data?
Only 15% of organizations globally have a fully developed preventative approach to cybersecurity and digital risk. In other words, most entities aren’t proactive enough when it comes to managing cyber risk.
Although the dark web is first and foremost a potential threat vector, security and risk managers should also understand it as a resource that can give them access to the information they need to prepare for and mitigate cyber risks.
Access to dark web data can help organizations:
- Identify data breaches sooner
- Mitigate risks faster
- Safeguard corporate and personal data
- Notify employees at risk of negative outcomes, including identity theft
- Change compromised credentials as quickly as possible
- Understand the scope of the cyber threats that affect the organization
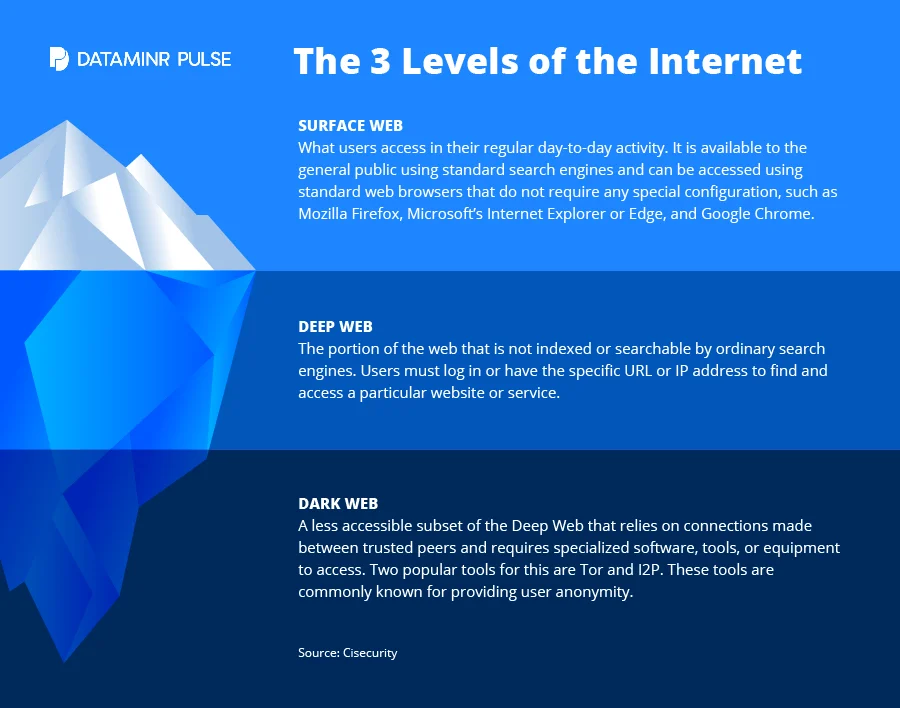
Because it’s below the surface web—that which we use on a daily basis—there’s no search engine to access dark web content. That’s not to say it isn’t possible. Normally, accessing the dark web requires anonymizing web browsing software, such as a Tor browser.
Use the dark web to mitigate risk
While it may be relatively simple to reach the dark web itself, the real challenge is sorting through the enormous sea of data floating beneath the surface. It’s estimated that less than 5% of the surface internet is indexed, meaning that everything else belongs to the deep and dark web.
Security and risk managers need a way to access the most relevant, mission-critical information quickly as high-impact events, especially cyber incidents, can escalate in seconds. But with over 75,000 terabytes of data on the dark web, there’s simply no way to uncover risk indicators in a timely manner. Doing so calls for the right technology and tools.
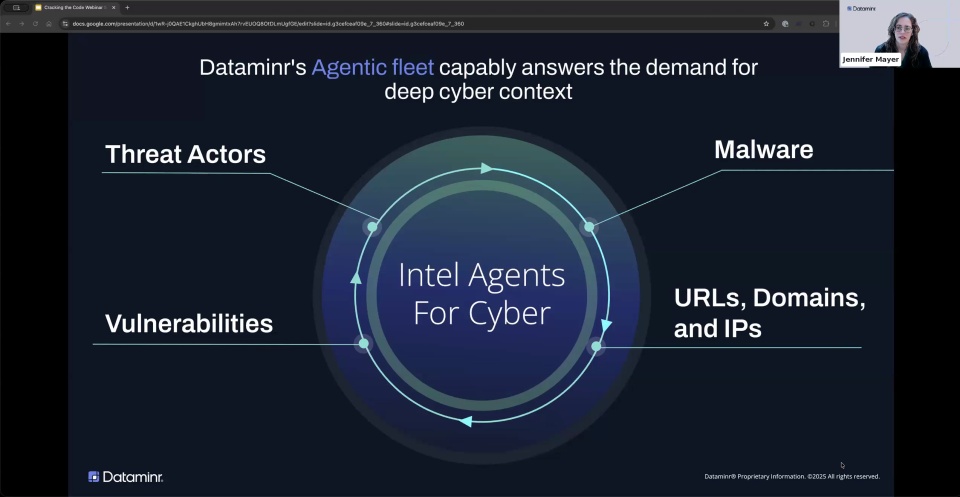
For example, real-time alerting solution Dataminr Pulse. It detects cyber threats as they emerge across the surface, deep and dark web and identifies vulnerabilities in internet-facing networks. Organizations that use Pulse are alerted to these threats as soon as they occur, oftentimes within seconds or minutes, helping them to mitigate risks more quickly and efficiently, including:
- Cyber-physical risks
- Cybersecurity policy and legislation
- Data breaches
- Distributed denial of service (DDOS)
- Phishing and malware
- Ransomware
- Threat actors
- Vulnerabilities
Learn more about Dataminr Pulse and its cyber risk capabilities.