Worldwide, 98% of organizations have integrations with at least one third-party vendor that has been breached in the last two years. Unfortunately, vendors are not always quick to identify or disclose a cyber attack or vulnerability. According to IBM, in 2023 it took the average organization 203 days to detect an attack, a window during which the organization and its customers were left at risk.
Zero-day vulnerabilities have increased in number year-over-year since the move to remote and hybrid work models. Threat actors have identified a method for exploiting these vulnerabilities in mass, causing significant disruption across several industries. The widespread utilization of zero-day exploits has changed the nature of vulnerability management and incident response, placing a greater emphasis on third-party risk management.
With the average data breach costing $4.45 million, visibility into vendor cyber vulnerabilities and attacks is critical. Here we outline the impacts of third-party attacks and best practices for ensuring comprehensive visibility of vendor risk.
3 best practices to improve visibility of third-party risk
Should a vendor breach occur, knowing what those risks might be is critical to preventing, or minimizing, significant and far-reaching implications such as monetary loss, erosion of customer trust, reputational damage and increased exposure to future attacks. The best practices outlined below can help cybersecurity teams get a clearer picture of potential third-party risk.
Assess vendor cybersecurity posture beforehand
The process of minimizing third-party risks begins even before engaging with a new vendor. Conducting thorough research about a prospective vendor’s cybersecurity policies, procedures and any past 8-K filings of security breaches helps cybersecurity teams understand the vendor’s level of vulnerability and appetite for risk. Teams can use this information to set cybersecurity requirements and obligations in vendor contracts, such as data protection measures, incident response procedures and compliance with industry standards or regulations.
Understand potential attack vectors
Despite a team’s due diligence in evaluating a vendor before the contract, incidents can still occur. Being proactive is key to mitigating threats. By understanding the sophistication of threat actors, tactics, techniques and procedures (TTPs), and victimology—as well as trends in activity relevant to an organization and its industry—cyber teams can take proactive measures against threats. This includes conducting penetration tests to inform an organization’s defense posture and improve contingency planning.
Stay vigilant to emerging threats with real-time threat intelligence
New threats continue to emerge and evolve. To know what to prepare for and what to remediate, cybersecurity teams must vigilantly monitor the changing external cyber landscape, including rising trends in victimology, TTPs and emerging threats through initial access brokerage as well as credential leaks, helping inform incident response plans.
Staying abreast of these trends can also increase the ability of cybersecurity teams to manage future incidents with the least amount of disruption to operations and with minimal financial impact—ultimately strengthening organizational resilience.
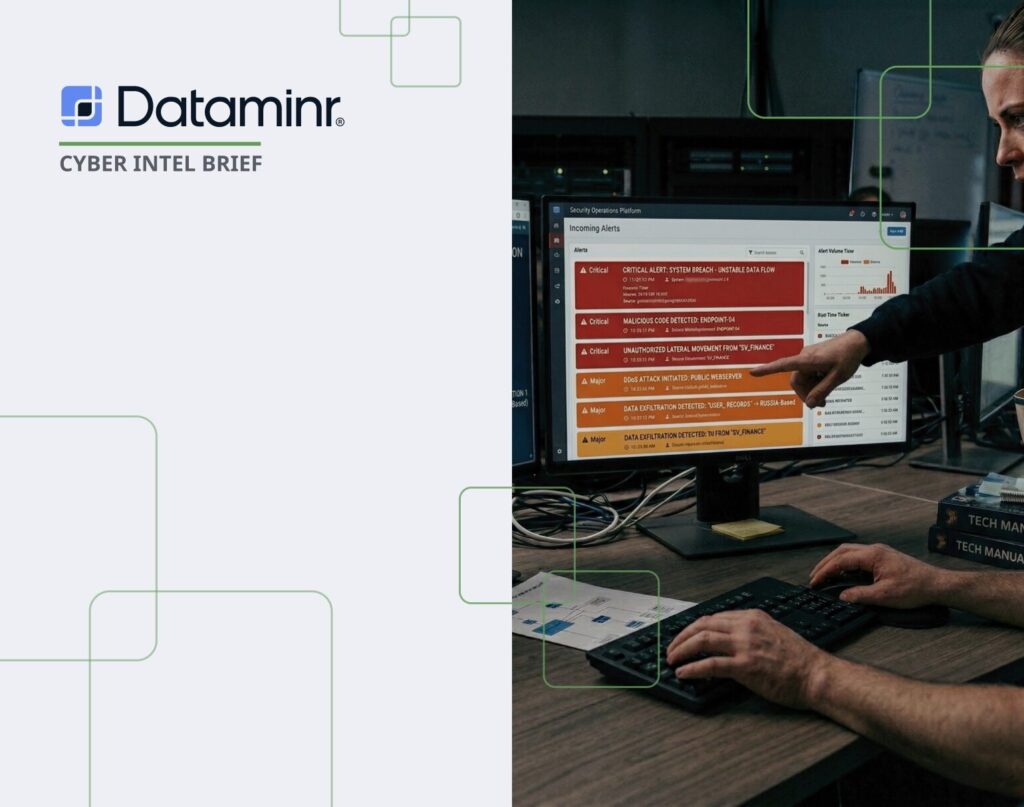
Advanced threat detection tools are a must-have for identifying third-party risks and critical events as they occur and evolve, be it seconds, minutes or days. When delivered in real time, cybersecurity teams get the lead time needed to take immediate action.
They can then quickly:
- Determine priorities
- Identify common or critical threats to their organization, industry and other vendors
- Surface relevant and actionable threat intelligence to senior leaders of appropriate teams
With the right alerts paired with deep contextual information, cybersecurity teams can properly evaluate the potential impact of a third-party event or threat, and action incident response playbook(s) as required.
Mitigating third-party risks is paramount to safeguarding an organization’s brand and financial stability. By proactively understanding potential vendor vulnerabilities, staying up to date with emerging threats and utilizing real-time intelligence, organizations can create better contingency plans for possible disruption, improve their overall defense postures and pre-empt or rapidly respond if an attack does occur—ultimately reducing the potential impact of vendor breaches.
Learn more about the role Dataminr Pulse for Cyber Risk plays in helping organizations proactively identify and mitigate risks through real-time cyber threat intelligence.